Researchers Uncover Hidden RDP Brute-Force Attack Infrastructure Linked to Ransomware Operations

Cybersecurity Investigation Uncovers Complex Infrastructure Linked to Credential Theft and Ransomware-as-a-Service Operations
A recent cybersecurity investigation began with a familiar alert: a brute-force attack on a remote server’s Remote Desktop Protocol (RDP) service. However, as researchers dug deeper, they uncovered a complex web of infrastructure linked to credential theft and potential ransomware-as-a-service operations.
Initial Discovery
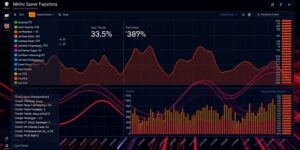
The investigation started with an examination of Windows event logs, which revealed a high volume of failed login attempts against the RDP service. While such attacks are common, the researchers noticed that the attackers had eventually succeeded in logging in, and what happened next was unusual.
Unusual Behavior
Instead of deploying ransomware or conducting a single intrusion, the attackers began searching for stored login credentials on the compromised host. This behavior suggested that the attackers were interested in gathering authentication data to use elsewhere, rather than just targeting the system itself.
Broader Implications
As the investigation progressed, analysts discovered that the attackers’ activity extended beyond the compromised host. The credentials being collected appeared to be part of a wider strategy for gaining access to other systems and environments. This pattern of credential harvesting and reuse is commonly associated with initial access brokers, who breach networks and sell access to ransomware operators.
Infrastructure Discovery
The researchers’ analysis led them to a geographically distributed network of systems linked through VPN services. These systems appeared to be used to relay traffic and conceal the origin of the attackers’ activity. By mapping these connections, researchers identified an organized infrastructure supporting the operation.
Ransomware-as-a-Service Ecosystem
The infrastructure suggested a coordinated setup designed to maintain persistence, evade detection, and move laterally across targets. This type of infrastructure is often used in ransomware-as-a-service ecosystems, where different groups handle different stages of the attack, from initial access to data theft and extortion.
Conclusion
The investigation highlights how routine cybersecurity alerts can sometimes reveal much larger threats. In this case, a common attack technique – repeated password guessing against a remote service – became the thread that allowed investigators to trace activity across multiple systems and uncover a broader cybercriminal infrastructure.