Paragon Solutions: Israel Spyware Firm Unknowingly Disclosed itself on LinkedIn

An Israeli spyware firm, Paragon Solutions, exposed itself accidentally. Know how!”
Once the sole purview of national intelligence services, the field of high-end cyber-surveillance has evolved into a thriving private sector.
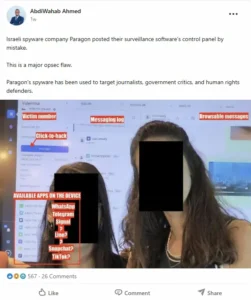
According to a recent study, an Israeli spyware company made a serious security breach that unintentionally exposed the export of “occupation technology” from the Palestinian territories to the rest of the globe.
Citizen Lab
| A program marketed for “national security” has become one of the most widespread government monitoring systems on the planet, thanks to the licensing of Israeli-made Pegasus spyware to about 45 countries worldwide, including at least 5 to 14 EU states. |
Exposure by “Accidental”
The main focus of Eldin’s research is a significant operational security (OPSEC) breach by an Israeli company, which is frequently associated in these circles with organizations such as Intellexa or the now-defunct QuaDream.
The company’s own infrastructure servers that were used to direct and manage malware were either left unguarded or could be recognized by a certain “digital fingerprint” in their code, which led to the disclosure.
Researchers and journalists were able to observe who was being targeted as well as how the spyware operated, thanks to this release. The “accident” revealed a unique map of the tools’ global circulation, demonstrating that they are being supplied to a number of regimes for the purpose of monitoring journalists, political opponents, and dissidents in addition to being utilized for national security.
Which Tool is Used?
The particular tool mentioned in Eldin’s most recent report is called Predator, and it was created by Intellexa (together with its subsidiary Cytrox).
- Context: Although NSO Group’s Pegasus is the most well-known malware, Predator has become its main competitor.
- The Exposure: The “accidental exposure” Eldin describes was when researchers were able to see Intellexa’s internal systems and customer management interfaces, exposing the company’s remote access to its own customers’ systems to track how they were using the spyware.
How does the Tool Work?
The “mercenary spyware” Predator uses a complex infection chain to function:
- Zero-Click & One-Click Exploits: It frequently infects a phone through a “zero-click” exploit (where the phone is infected just by getting a message or through “Aladdin,” a malicious advertising system) or a “one-click” link (posing as a news story or shipment update).
- Stealth Mechanism: Predator has the ability to suppress recording signs, according to recent technical deep dives. An orange or green dot typically appears on an iPhone when the microphone or camera is turned on. To conceal these dots and prevent the victim from realizing they are being watched, the predator employs a “single hook” in the iOS code.
- The “Alien” Loader: Predator functions on Android using a component known as “Alien.” Alien downloads and conceals the primary Predator spyware by infiltrating the fundamental system processes (such as “Zygote”).
- Anti-Analysis: A “kill switch” and an error-reporting mechanism are features of the utility. The malware will self-destruct and return an error code to the operator explaining why the infection failed if it detects that a security researcher or a privacy-conscious user is using analysis tools (such as netstat to monitor network connections).
Impact on Systems and Victims
1. Total Surveillance: After installation, operators can access:
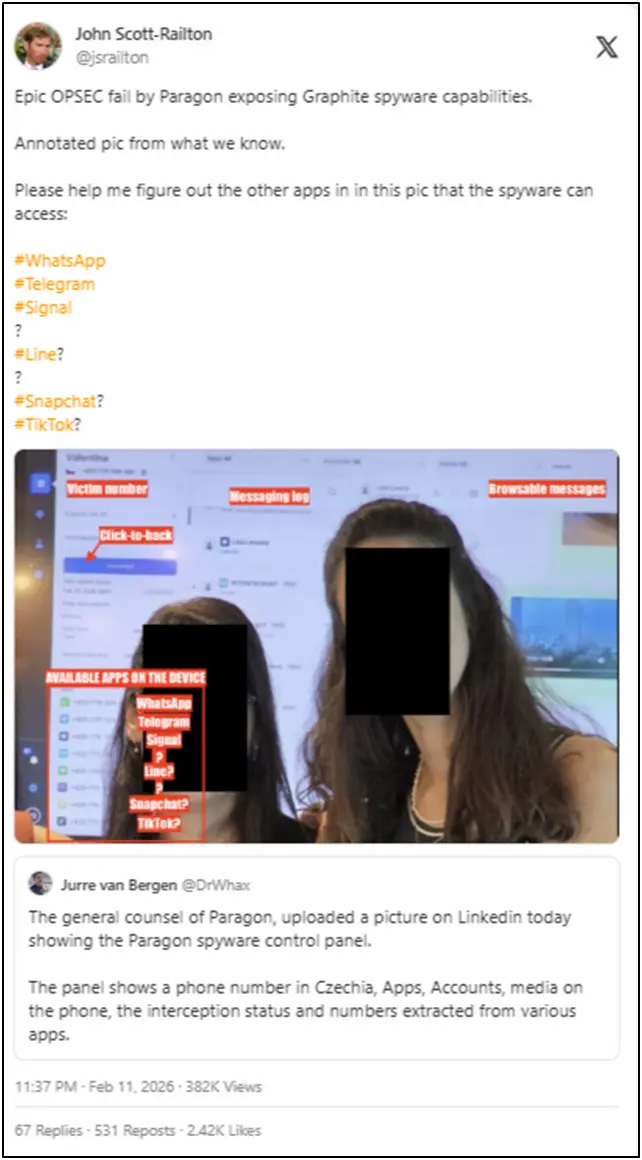
- Encrypted Chats: It records messages on the device both before and after encryption in order to read them from Telegram, WhatsApp, and Signal.
- Live Monitoring: It can activate the camera and microphone to capture footage or background noise.
- Data Exfiltration: Photos, call logs, contacts, and GPS history are all stolen.
2. Psychological Impact: Because the spyware is “invisible” (it doesn’t drain batteries or cause overheating), victims frequently go months or years without realizing they are being watched, which is a serious invasion of privacy and safety for political figures, journalists, and activists.
The “Occupation-to-Export” Pipeline
Eldin contends that the Israeli occupation of Palestinian territory serves as the main “testing ground” for these technologies. He explains a pipeline that cycles:
- Field Testing: The everyday observation of Palestinians in the West Bank and Gaza perfects new surveillance techniques, including bulk data harvesting, phone hacking (Zero-Click vulnerabilities), and facial recognition.
- Unit 8200 Origins: The majority of the founders of these companies are former members of Israel’s top signals intelligence unit, Unit 8200. They “privatize” state-funded knowledge into profitable enterprises.
- Global Export: After being “battle-proven,” these weapons are marketed to governments around the world. Eldin emphasizes that a nation purchasing this technology is importing a particular logic of control rather than only purchasing software.
Ahmed Eldin
| These spyware companies frequently serve as an unofficial diplomatic branch of Israel. Sales of such potent instruments are often used to forge strategic partnerships with authoritarian regimes or as a “sweetener” in normalization agreements. |
Geopolitical Implications and Shadow Diplomacy
- The “Palestine Effect”: Eldin presents a theory he refers to as the “Palestine Effect,” which holds that strategies and technology developed during the occupation eventually “show up” elsewhere, especially in Western democracies (e.g., utilized by police departments in the United States or by European governments to track activists).
Why Paragon Wants You to Think It’s “Different?”
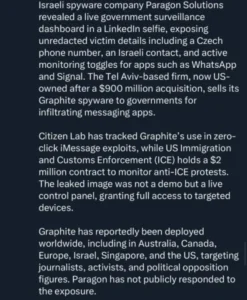
As a result of the NSO Group and Intellexa controversies, Paragon Solutions has become a new player in the Israeli surveillance market. Paragon has put a lot of work into positioning itself as the “ethical” alternative in the mercenary spyware business, in contrast to its predecessors, which have been subject to worldwide censure and blacklisting.

The “White Hat” Marketing Strategy
Paragon presents itself as a business that exclusively sells to “democratic” countries or those with strict human rights regulations. They want to steer clear of the legal ramifications and public relations catastrophes that destroyed NSO Group by establishing themselves as a responsible law enforcement partner.
They assert that they have stringent internal control committees that screen all prospective customers to make sure the technology isn’t being utilized against human rights advocates or journalists.
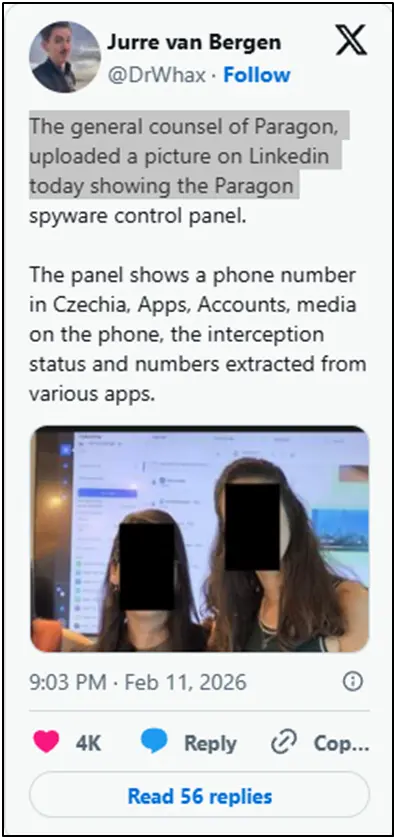
The Product: Graphite
Graphite, Paragon’s flagship tool, is made to get beyond the encryption of contemporary cellphones. Paragon notes that although it works similarly to Pegasus or Predator, its technology is meant for “targeted” surveillance of terrorists and serious criminals rather than the “mass” or “indiscriminate” surveillance associated with its rivals.
The Reality Check

- The Pipeline remains the same: Nearly all of Paragon’s employees are veterans of Israel’s Unit 8200, just like its competitors. Graphite’s “battle-proven” techniques and technological underpinnings come from the same occupation-to-export pipeline.
- Lack of External Oversight: Although they are self-regulated, Paragon claims to have internal ethics committees. The history of the spyware industry has demonstrated that the parent corporation has very little control (or incentive) to prevent misuse once a contract is signed and the software is in the hands of a foreign government.
- Strategic Ties: Paragon has strong ties to the Israeli security establishment and has drawn substantial investment from American venture capital firms despite its “ethical” image. This implies that Paragon is merely the next generation of the same industry, made to be more “palatable” to Western authorities and the U.S. Department of Commerce, rather than a “different” product.
How to Prevent Becoming a Victim?
Although blocking mercenary spyware is quite challenging, you can drastically lower your “attack surface”:
- Enable Apple’s Lockdown Mode: This is the best defense for high-risk iPhone users, such as journalists or activists. It turns off a number of characteristics that malware utilizes to enter, such as link previews and sophisticated web technology.
- Reboot Daily: Since many of these exploits are “non-persistent,” they reside in the temporary memory (RAM) of the phone. Every 24 hours, restarting your phone can “kick out” the spyware, making it necessary for the attacker to use a costly hack to regain access.
- Disable iMessage and FaceTime: Turning them off while not in use eliminates a significant point of entry for zero-click attacks.
- Use an Ad-Blocker: Using a system-wide ad-blocker or a privacy-focused browser (like Firefox Focus) gives an extra layer of protection because dangerous advertising is used by programs like “Aladdin” to infect phones.
- Avoid Sideloading: Apps from sources other than the official Google Play Store or Apple App Store should never be installed.
What to Do if You are Already a Victim?
If you think you’ve been singled out:
- Do Not “Factory Reset” Immediately: The forensic evidence required to demonstrate that you were hacked might be erased by a reset.
- Isolate the Device: Disable cellular data and Wi-Fi, or place the phone in a Faraday bag (or an unpowered microwave to block signals).
- Check with MVT: Check for “Indicators of Compromise” (IoCs) in your device backups using the Mobile Verification Toolkit (MVT), an open-source program created by Amnesty International.
- Contact Experts: Speak with groups like Access Now’s Digital Security Helpline or Citizen Lab. They are experts at spotting these particular state-level dangers.
- Replace the Hardware: The only surefire way to eradicate high-level malware like Predator or Pegasus is to throw away the actual device and start over with a new phone and SIM card. Because the spyware might be concealed in the backup files, never restore from a backup.
The Crisis of Accountability
These businesses frequently get around the export restrictions that are in place for conventional weapons because they are private companies. Even when organizations like NSO Group, the company behind Pegasus, are sued or blacklisted, new businesses with the same employees and technology almost instantly appear under various names (e.g., Cytrox or Intellexa).
About The Author
Suraj Koli is a content specialist in technical writing about cybersecurity & information security. He has written many amazing articles related to cybersecurity concepts, with the latest trends in cyber awareness and ethical hacking. Find out more about “Him.”
Read More:
Cybersecurity Jobs Available Now: Top 10 In-Demand Roles for 2026








