Over 280,000 WordPress Sites Attacked Using WPGateway Plugin Zero-Day Vulnerability
Over 280,000 WordPress Sites Attacked Using WPGateway Plugin Zero-Day Vulnerability
If you want to learn web development, then you can use WordPress. Why? That’s because it’s easy to operate and provides you with several plugins to maintain your content quality. Those who have experience in building websites can benefit more with the support of WordPress.
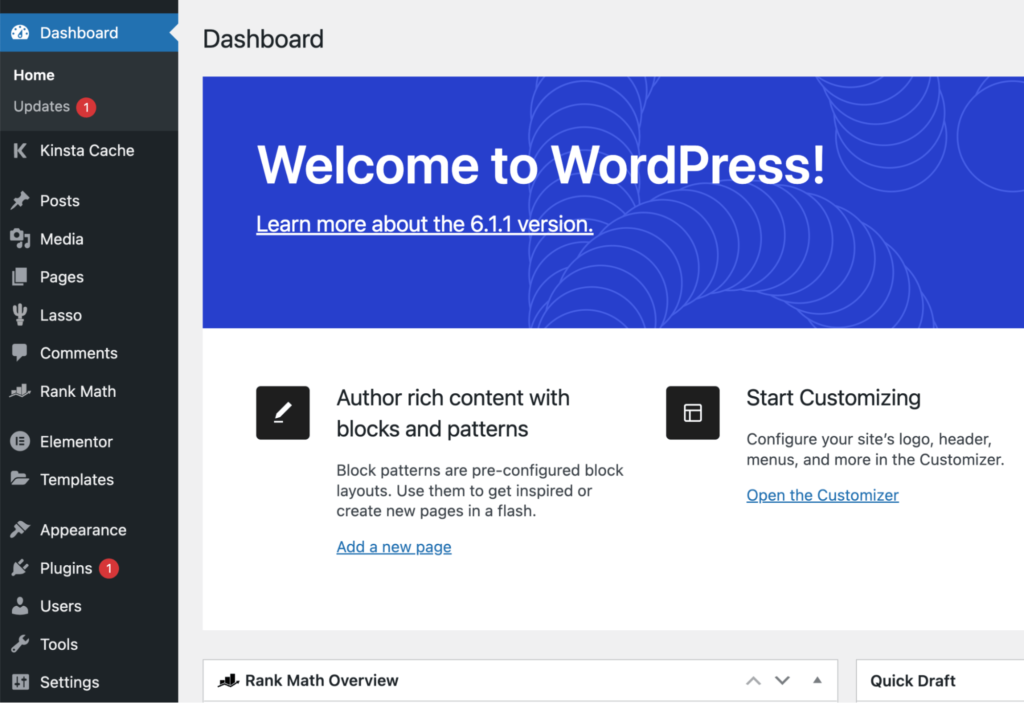
Moreover, one can customize their websites made on this platform several times with various themes. Developers like this platform a lot. But a piece of news came in front of everyone that didn’t suit the moment.
The latest version of WPGateway (WordPress Premium Plugin) comes out with a zero-day flaw. The flaw was found out by adversaries in the wild and exploited on the spot. Due to that, several sites were victimized. Well, that’s one of the confident actions taken by adversaries.

Adversaries took access to those sites and that’s a big issue for several organizations that are bound to those websites. Vulnerabilities were found as CVE-2022-3180 with a CVSS score of 9.8.
WordPress Security Company WordfenceDue to the flaw of the latest version of the WPGateway Plugin, adversaries got access to the websites of several victims. “Part of the plugin functionality exposes a vulnerability that allows unauthenticated attackers to insert a malicious administrator,” Wordfence researcher Ram Gall said in an advisory. Wordfence said it blocked over 4.6 million attacks attempting to take advantage of the vulnerability against more than 280,000 sites in the past 30 days. |
Moreover, if we talk about the WPGateway, then it is built in order to support site admins with the installation, backup, cloning of WordPress Plugins, and themes via a unified dashboard.
You can indicate that your website has been victimized by seeing your website’s plugin have an admin username of “Rangex”.

| Additionally, the appearance of requests to “//wp-content/plugins/WPGateway/WPGateway-webservice-new.php?wp_new_credentials=1″ in the access logs is a sign that the WordPress site has been targeted using the flaw, although it doesn’t necessarily imply a successful breach. |
More information about the security flaw has been held back so that other adversaries could not exploit it more. Without the availability of a patch, more users can become the victim, so they’re advised to remove the plugin from their WordPress Installations. That is only till the launch of patches.
A BackupBuddy named WordPress Plugin also came in contact with a zero-day flaw which came to the senses of people. After that, a patch was unleashed for the previous flaw.
“The disclosure also arrives as Sansec revealed that threat actors broke into the extension license system of FishPig, a vendor of popular Magento-WordPress integrations, to inject malicious code that’s designed to install a remote access trojan called Rekoobe.”
Make sure to read all tech-related news and blogs that get updated every day. Many cybersecurity information providers offer daily news on how technology is becoming the source of evil for the innocent. Learn, Research, and Grow!
Kindly read more articles :
U.S. Imposes New Sanctions on Iran Over Cyberattack on Albania
A Suspected Cyber Fraud of ₹15 Lakhs Happened with an Engineering Firm by Local Police






