A Windows 11 Automation Tool Can Easily Be Hijacked
Well, developers act like they know everything and sometimes this kind of thinking becomes the reason for hijacking and data breaches. Controlling fire with petrol isn’t some kind of joke, so you must calculate the consequences before recruiting new forces to act.
Microsoft is now on the HOT TOPIC because a tool that is inbuilt in Microsoft devices can give access to someone who has already got the upper hand on the devices. However, this is something a researcher found out so the patches have already been on updates.
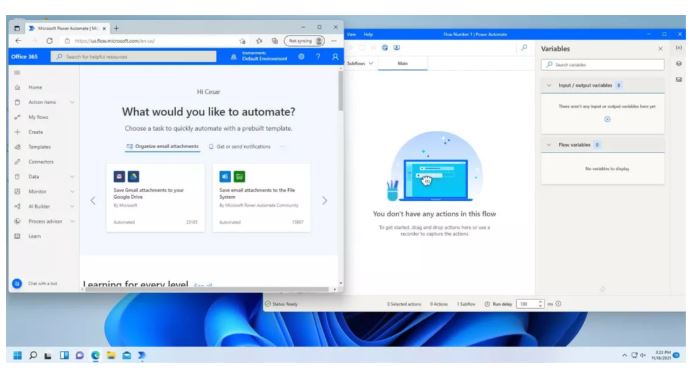
Randomly this news popped up on the news filters and came out as awareness for organizations to secure their networks and devices after going through the mess in the news. So, the tool that is the main hot spot is Microsoft’s Power Automate.
With the help of this tool, hackers can spread ransomware and keyloggers only if the device is already in possession of the attacker. Well, above all automating mundane tasks has been on the easy list over the past few years.
Let’s look at some of the benefits that come with the tools provided with the devices such as Drag-and-Drop automation software. With the support of this tool, you can easily have a track record of how many hours you have worked in a spreadsheet.
There, on the other side, a to-do list will be ready for you, if you get your name in an email. Tools and technology can make your life easier halfway. But they could be riskier too. There’s no second opinion to it.
A security researcher has observed an easier way to hijack Microsoft’s Software Automation Tool. By accessing it, they can send ransomware to connected devices and breach data with ease.
| Michael Bargury, (Co-founder and CTO) Zenity,
Well, earlier the automation tool was in use as the way it was designed. But instead of doing the regular operation, it came into the spotlight as it can be used for deploying malware. “My research showed that you can very easily, as an attacker, take advantage of all of this infrastructure to do exactly what it is supposed to do,” Bargury says. “You [then] use it to run your payloads instead of the enterprise payloads.” “Every business user now has the power that the developer used to have,” Bargury says. “You can exfiltrate data outside of the corporate networks through this trusted tunnel, you can build keyloggers, you can take information from the clipboard, you can control the browser,” Bargury says. This type of attack could be hard to detect, as it uses official systems and processes throughout, Bargury says. “When you think about the architecture, this is a remote code execution tool that is built by Microsoft and signed by Microsoft throughout the way,” Bargury says. Before his DefCon talk, Microsoft’s team reached out to him, Bargury says, and pointed out that business network admins can restrict access to Power Automate tools by “adding a registry entry” to their devices. As the possible risks around low-code/no-code applications become more obvious, Bargury says companies may need to reassess their policies. “It’s very important to monitor what RPA agents are doing,” he says. |
Bargury thinks adversaries can use Power Automate to spread malware payloads more quickly, explaining “how” in a June DefCon presentation. He released the code for the attack, called Power Pwn, in August.
“The researcher’s work was documented at the DefCon hacker conference, last month and has since released the code.” Bargury’s organization’s priority is to assist in securing low-code/ no-code apps. Moreover, he uploaded demos, and the processes helpful in running the attack to help increase awareness of the potential issues companies face.
Ahead of the DefCon talk, Bargury made several demos representing how it is easier to use Power Automate to unleash ransomware on affected devices. There, other ones had ways adversaries can steal authentication tokens from a device.
Power Automation
- Well, Microsoft’s Power Automate was the main tool to be used in this attack. This tool was built into Windows 11.
- To start the attack first, the tool takes the form of robotic process automation (RPA). In this process, the computer imitates humans’ moves to accomplish goals.
- To get notified each time, there will be an RSS feed ready for you.
- Toto achieve that you can prepare a customized RPA process.
- In the market, you’ll see a count of thousand + automation existing. Moreover, Microsoft’s software can connect to:
- Outlook,
- Teams,
- Dropbox,
- and other apps.
- Power Automation (software) is part of a broader low-code/ no-code movement.
- It aims to make tools users can use to create things without having extra coding skills.
Process of Attack
Before Attack Preparation
- Let’s look at the research’s beginning. In this context, the adversary must have gained control of the user’s PC (whether via phishing/ an insider threat).
- After accessing the device, attackers need to take a few more steps to modify the RPA setup. In reality, they are simple.
- “There’s not a lot of hacking here,” says Bargury, who dubbed the whole process Power Pwn and is documenting it on GitHub.
STEP to ATTACK
- First, an adversary must set up a Microsoft Cloud Account, that is the tenant. That is to get admin controls over any devices assigned to it.
- It will permit the malicious account to run RPA processes on an end user’s device.
- On an already compromised device, an adversary just needs to assign it to the new admin account. To do that, an adversary can use a simple command line, called silent registration.
- “Once you do that, you will get a URL that would allow you, as an attacker, to send payloads to the machine,” Bargury
| Note
PCs in organizations are frequently insecure. That is due to a lack of patches and updates. E.g. – an adversary would have already gotten into a corporate network. |
Anonymous Spokesperson, Microsoft
Microsoft’s spokesperson downplayed the attack’s impact, saying that an account must be accessed by an adversary before it could be used. “There is no mechanism by which a fully updated machine with antivirus protections can be remotely compromised using this technique,” the spokesperson says.
“This technique relies on a hypothetical scenario where a system is already compromised or susceptible to a compromise using existing techniques like social engineering—both for the initial and any subsequent network attack,” the spokesperson adds, recommending that people keep their systems up to date.
Solution
If you do this, then accounts will fall under control that could sign in to power automation. They think that it can reduce the chances of hijacking. However, to succeed, Bargury says, the move relies upon security teams having consistent and clear policies across their organizations, which isn’t always the case.
News, Globally
Many users think that RPA tools are a good way to hijack someone’s device. But there are several ways in which the attacker could exploit loopholes to do something fishy. In early 2020, Microsoft’s security team found six hacker groups, including a Chinese APT, inside the network of one company.
Microsoft, Event Report
One of the hacker groups used automated systems to remove data. “In an uncommon move, the attacker used the customer’s existing systems, including eDiscovery, the Compliance Search feature, and Microsoft Flow, to automate stealing its search results.”
Alert!
“You cannot expect to provide all of the business users in an enterprise with capabilities that were, up until a few months ago, reserved only to developers and expect everything to go well.”









