Android Zero-Day Vulnerabilities in Pixel Phones Were Exploited by Forensic Firms, Warned by Google
Android Zero-Day Vulnerabilities in Pixel Phones Were Exploited by Forensic Firms, Warned by Google

The exploitation of two Android security vulnerabilities that affect Google Pixel smartphones by forensic organizations has been disclosed by Google.

The following zero-day vulnerabilities are classified as high-severity:
- CVE-2024-29745: Information disclosure vulnerability in the firmware component.
- CVE-2024-29748: A privilege escalation vulnerability in the firmware component.
“Information suggests that the [vulnerabilities] might be the subject of restricted, targeted exploitation,” Google wrote in an advisory dated 2 April 2024.
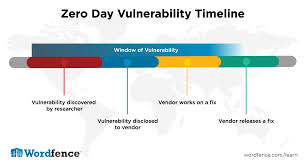
Although the technology behemoth refrained from disclosing further details regarding the attacks capitalizing on these vulnerabilities, GrapheneOS maintainers stated that “forensic firms are actively exploiting them in the wild.”
A series of posts on X (previously Twitter) stated, “CVE-2024-29745 pertains to a weakness in the fast boot firmware that facilitates unlocking, flashing, and locking.”

“Forensic firms are rebooting smartphones in After First Unlock state into fast boot mode on Pixels and other devices to take advantage of flaws there and then dump memory.”

GrapheneOS identified CVE-2024-29748 as a vulnerability that local attackers could exploit to disrupt a factory reset initiated via the device admin API.
The revelation occurred over two months subsequent to the GrapheneOS team’s revelation that forensic firms are capitalizing on firmware weaknesses affecting Google Pixel and Samsung Galaxy smartphones in order to illicitly acquire data and monitor users’ activities while the devices are idle.

Additionally, it demanded that Google implement an auto-reboot function to hinder the exploitation of firmware vulnerabilities.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager entered the field of content in an unusual way. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.