Critical Vulnerability Discovered in Atlassian Bitbucket Server and Data Center

Before continuing to the news, let’s talk about Bitbucket Server for those who don’t know what that is. As with any other server, the bitbucket server is a combo of Git Server and a Web Interface product. That is written in Java and built with Apache Maven. Users with the help of this server can run basic Git operations while reading and writing the codes.
Atlassian is the developer of Bitbucket Server. A few days ago, Atlassian unleashed patches for a security flaw in Bitbucket Server and Data Center. Due to which result could be the execution of malicious codes on vulnerable installations.
Atlassian Bitbucket server Flaws and Solutions
The vulnerability was tracked as CVE-2022-36804 which got the CVSS Score of 9.9. Well, the nature of the issue is explained as a command injection vulnerability in several endpoints. Those vulnerabilities could be easily exploited via specially customized HTTP requests for the victim.
Related news here: https://www.bleepingcomputer.com/news/security/atlassian-bitbucket-server-vulnerable-to-critical-rce-vulnerability/
Atlassian said in an advisory
“An attacker with access to a public Bitbucket repository or with reading permissions to a private one can execute arbitrary code by sending a malicious HTTP request.”
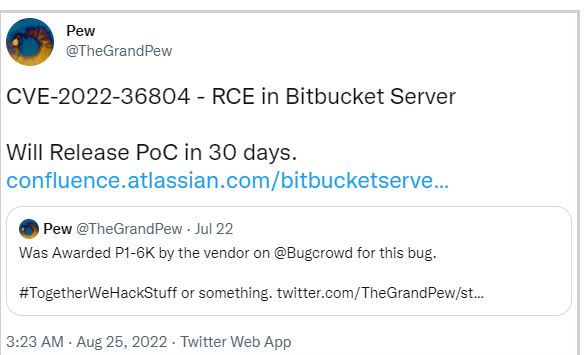
@TheGrandPew (Researcher) was the one who listed the shortcomings of Bitbucket. After he discovered the incidents, he reported them with a sense of urgency. Those vulnerabilities made a big impact on every version of Bitbucket Server and Datacenter that was released after the date – 6.10.17, inclusive of 7.0.0 and the ongoing ones. The versions that got affected by this vulnerability are as follows.
- Bitbucket Server and Datacenter 7.6
- Bitbucket Server and Datacenter 7.17
- Bitbucket Server and Datacenter 7.21
- Bitbucket Server and Datacenter 8.0
- Bitbucket Server and Datacenter 8.1
- Bitbucket Server and Datacenter 8.2
- Bitbucket Server and Datacenter 8.3
Solutions to the Issues
As a temporary solution, where the genuineness of patches isn’t confirmed, Atlassian made a decision. Due to that, the recommendation for people is to turn off public repositories while making use of “feature.public.access=false“. That is to prevent unauthorized users from accessing to exploit the flaw.
But you can’t take it as your win, as the attacker still has the advantage on his hands. That’s because he has the user account with him. In simple terms, a cybercriminal could take advantage of the account as he still possesses the original credentials he got from various tactics and tools.
Advice for Users
Older versions‘ users whose version got some impact due to this loophole must upgrade to the latest version ASAP. That’s to reduce the risk of potential threats that could appear because of the loophole’s existence. Now, you must have understood the fact that why shouldn’t anybody click on the suspicious links and check out the updates on information and technology every time? Learn, Research, and Grow!










