Lucifer- Penetration Testing Tool for Automated Network Penetration Testing

Lucifer – A Powerful Penetration Tool For Automating Penetration Tasks Such As Local Privilege Escalation, Enumeration, Exfiltration
How to Setup Lucifer Penetration Testing Tool
git clone https://github.com/Skiller9090/Lucifer.git
cd Lucifer
pip install -r requirements.txt
python main.py --help
If you want the cutting edge changes add -b dev to the end of git clone https://github.com/Skiller9090/Lucifer.git
Commands
| Command | Description |
|---|---|
| help | Displays This Menu |
| name | Shows name of current shell |
| id | Displays current shell’s id |
| show | Shows options or modules based on input, EX: show <options/modules> |
| options | Shows a list of variable/options already set |
| set | Sets a variable or option, EX: set |
| set_vars | Auto sets need variables for loaded module |
| description | Displays description of the module loaded |
| auto_vars | Displays is auto_vars is True or False for current shell |
| change_auto_vars | Changes the auto_var options for one shell, all shells or future shells |
| reindex | Re-indexes all modules, allows for dynamic additions of modules |
| use | Move into a module, EX: use |
| run | Runs the current module, can also use exploit to do the same |
| spawn_shell | Spawns a alternative shell |
| open_shell | Open a shell by id EX: open_shell |
| show_shells | Show all shell ids and attached name |
| set_name | Sets current shells name EX: set_name |
| set_name_id | Set a shells name by id EX: set_name_id |
| clear | Clear screen |
| close | Kills current input into opened shell |
| reset | Resets Everything |
| exit | Exits the program, can also use quit to do the same |
Command Use
-
No-Arg Commands
help– to display help menuname– shows name of current shellid– shows current shell idoptions– shows a table of set options/varsset_vars– automatically sets vars needed for the loaded module (default defined in a module)description– show description of current loaded moduleauto_vars– displays current setting of auto_vars (auto_vars if true will automatically run set_vars on module load)run– runs the module with the current options,exploitworks the samespawn_shell– spawns a new Shell instanceshow_shells– shows all open shells ids and namesclear– clears the terminal/console screenclose– kills the input to current shellreset– resets everything (not implemented)exit– quits the program
-
Arg Commands
show <options/modules>– displays a list of set options or modules depending on argument.set <var_name> <value>– sets a variable/optionchange_auto_vars <to_set> <args>:<to_set>– can be true or false (t or f) (-t or -f)<args>:-g= global – sets for all shells spawned-n= new – sets this option for future shell spawns-i= inclusive – no matter what, set current shell to <to_set>
use <module> <args>:<module>– path to module<args>:-R– Override cache (reload dynamically)
open_shell <id>– opens a shell by its idset_name <name>– set the name of the current shellset_name_id <id> <name>– set the name of the shell specified by
Using Java
Lucifer allows for Python and Java code to work side by side through the use of LMI.Java extension. For this to work you will need to install jpype1, to do this run the following command in your python environment:
pip install jpype1
From here you are free to interact with LMI.Java.compiler and LMI.Java.luciferJVM which allows you to call java functions and instantiate java classes through python, more documentation of this will be created later on, on the lucifer wiki.
Examples
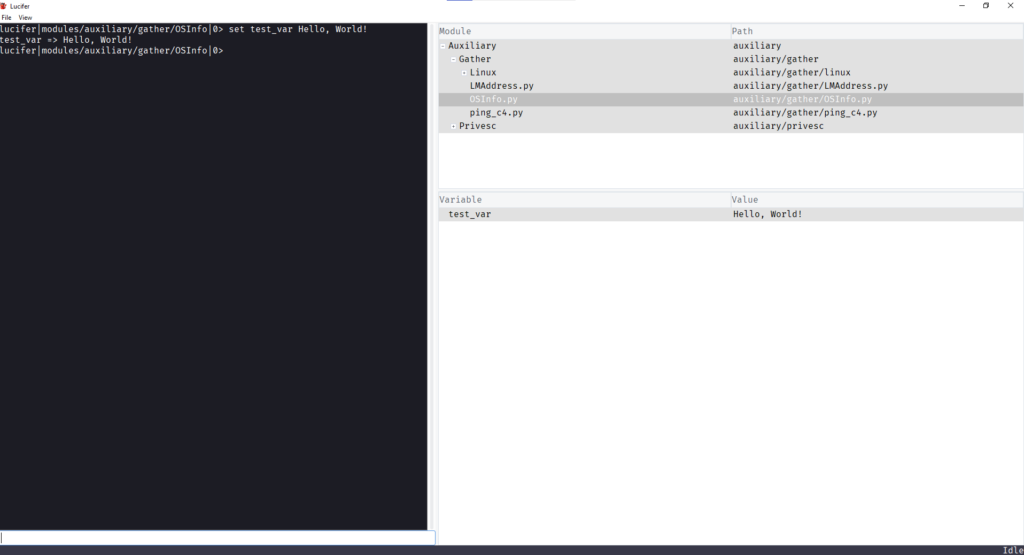
Settings Variables
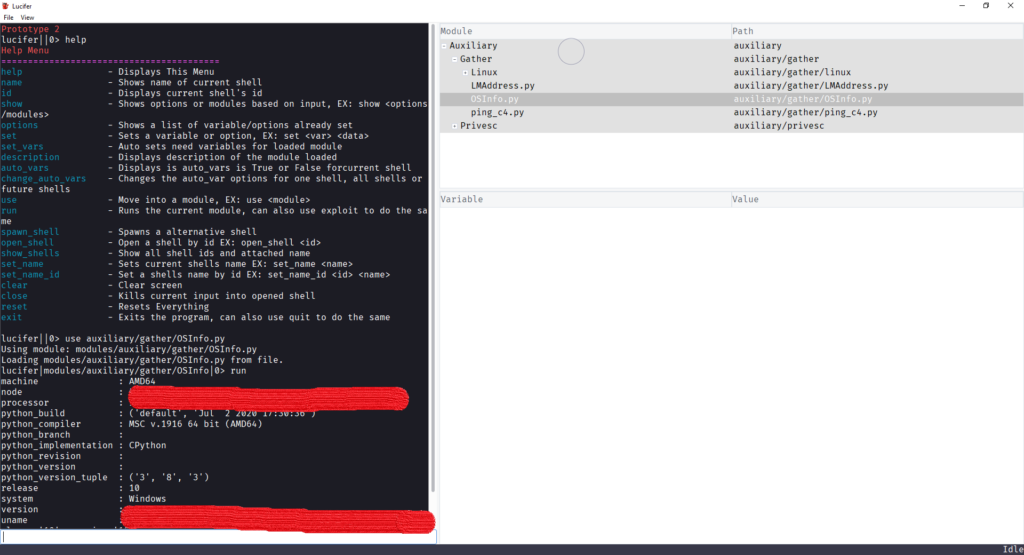
Running Module
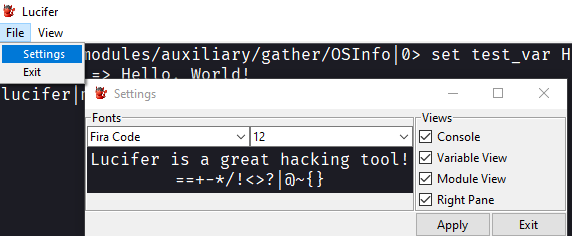
Settings