Malicious Browser Extension Has Been Widely Used To Surveillance Email IDs by North Korean Hackers

In North Korea, a malicious intent black hat hacker is functioning with full interest duly deploying a malicious extension on Chromium-based web browsers that is fully able to compromise Email content from Gmail and AOL.
SharpTongue, an activity cluster from a widely renowned cyber security enterprise named Volexity imputed this malware in order to share overlappings with an opposing collaborative publicly termed with the name Kimsuky.
The activity cluster – SharpTongue possesses a history of identifying people working for some prominent organizations in the US, Europe, and South Korea who “work on topics involving North Korea, nuclear issues, weapons systems, and other matters of strategic interest to North Korea,” said by the primetime investigators Thomas Lancaster and Paul Rascagneres.
The usage of the mentioned knave extensions during the attacks is not a fresh culture. In the year 2018, the malicious threat actor was observed using a Chrome plugin as an integral section of the campaign named Stolen Pencil just to contaminate its targets and rob the confidential browser cookies, User IDs, and Passwords. However, the recent spying trial is strictly distinguished in that it utilizes the extension with the name Sharpext, to loot some of the crucial and sensitive types of the Email database.
In addition to this, the investigators commented further, “The malware directly inspects and exfiltrates data from a victim’s webmail account as they browse it.”
Moreover, the aimed browsers comprise Google Chrome, Naver’s Whale browsers, and Microsoft Edge, with the particular mail-stealing malware dedicatedly developed to reap data from Gmail and AOL sessions.
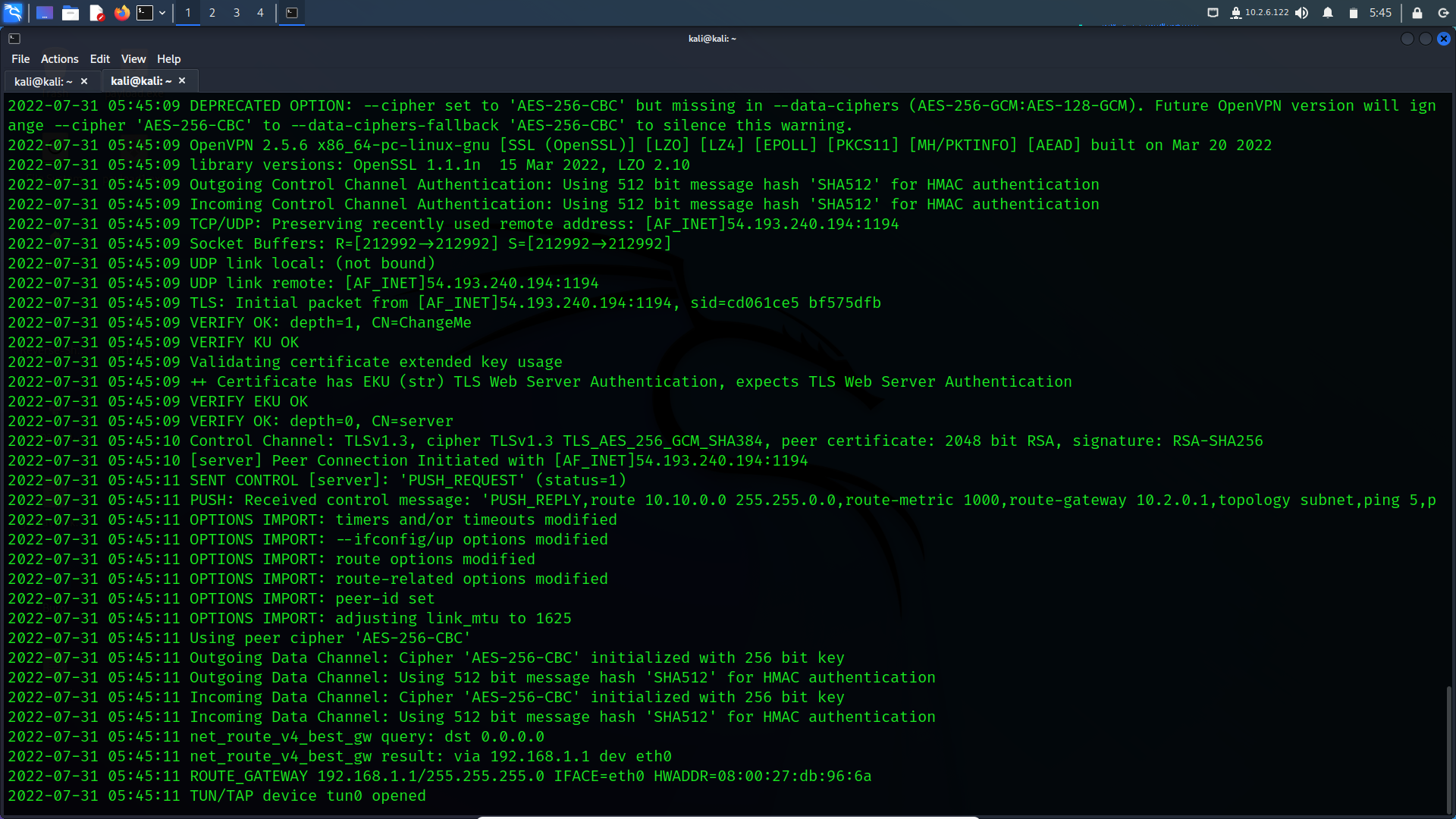
Further, installation of the add-on is achieved by several measures of substituting the web browser’s Preferences and Secure Preferences files with those particular obtained from a distant server subsequent to a confirmed data infringement of an aimed Windows system. However, this particular step is triumphant by allowing the individual DevTools panel inside the functioning tab to comprise the Email account and the attachments from a target’s mail inbox. In addition, some distinctive steps are taken simultaneously to conceal any alarming messages about operating developer mode extensions.
The top-notch cyber security firm Volexity has now marked the campaign as ‘quite successful,’ describing the malicious threat actor’s capability to compromise the databases of thousands of Email Accounts from several targets by deploying the malware. In addition to the give a concrete node their words, the investigators said, “This is the first time Volexity has observed malicious browser extensions used as part of the post-exploitation phase of a compromise. By stealing email data in the context of a user’s already-logged-in session, the attack is hidden from the email provider, making detection very challenging.”
Subsequently, the research intel came after many months since the Kimsuky threat actor was linked to invasions against political agencies duly found in the countries like Russia and South Korea to provide the latest version of a remotely channeled trojan with the name Konni. Recently in the last week, a cyber security firm Securonix revealed an active attack campaign compromising high-quality targets, comprising the nations like Poland, the Czech Republic, etc. as important parts of the campaign codenamed as STIFF#BIZON curated just to disperse the Konni malware to the target spots.
Meanwhile, the techniques and the dedicated tools utilized in the incursions point to a specified North Korean hacking group which calls itself APT37, some concrete level of proof is collected referring to an attack infrastructure depicts the engagement of the Russian-based hacker’s group – APT28 (also known as Fancy Bear or Sofacy) actor.
In the conclusion, the main concentrating point in the whole case is the utilization of Konni malware in affiliation with the spycraft likenesses to APT28 as per the investigators. In addition to their statement, they further added that it could be a scenario of a particular group disguising themselves as another one just in order to confuse the research team and draft a soul escape.
I expect you like this article, read more of mine in the following similar news articles:
Fresh Cyber Attacks Methods Have Been Imposed By Hackers Right After Microsoft Bar Macros by Default





