Phishing Scams Using Fake Party Invitations: How to Protect Your Passwords
Fake Party Invitation Phishing Scams Target Internet Users
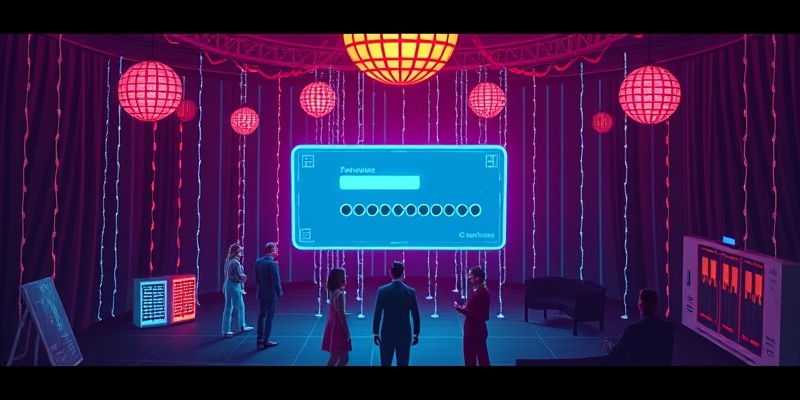
In a recent wave of phishing attacks, cybercriminals are leveraging fake party invitations to deceive internet users into divulging sensitive information and installing malware on their devices.
“These scams mimic popular invitation platforms, utilizing psychological tactics to create a sense of urgency and curiosity among potential victims.” — Rachel Tobac, CEO of SocialProof Security
Methods Employed by Phishers
- Malware injection: When a user clicks on a seemingly dead link, malware is silently installed on their device, allowing attackers to harvest passwords and personal data without the victim’s knowledge.
- Credential harvesting: Victims are redirected to a webpage that requests login credentials, providing phishers with unauthorized access to personal accounts.
Protecting Against Phishing Scams
Experts recommend being cautious when receiving unexpected invitations, avoiding suspicious links, and reporting phishing attempts to your service provider. Trust your instincts and prioritize online safety by ignoring unfamiliar or unsolicited communications.
Larger Trend of Sophisticated Attacks
This phishing campaign is part of a larger trend of increasingly sophisticated attacks, including fake E-ZPass toll notices, phony DMV warnings, and IRS impersonation attempts. According to a 2025 McAfee survey, nearly a quarter of Americans have fallen victim to a tax scam or know someone who has.
Conclusion
As the cybersecurity landscape continues to evolve, it is essential for individuals and organizations alike to remain vigilant and adopt best practices for online security.









