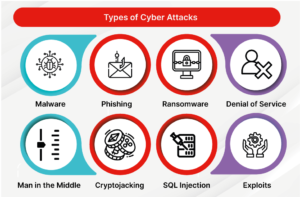
Types of Cyber Attacks
What is a Cyber Attack?
A cyber attack encompasses deliberate actions aimed at compromising a computer or any component of a computerized information system, with the intent to alter, dismantle, or pilfer data while also exploiting or causing harm to a network. The frequency of cyber-attacks has increased in tandem with the growing prevalence of digitalization in the corporate sector in recent years. While a wide array of attack methods exists, the compilation of different Types of Cyber Attacks encompasses a selection of the 20 most frequently encountered cases.
Top 20 Most Common Types of Cybersecurity Attacks
1. DoS and DDoS Attacks
A denial-of-service (DoS) attack is specifically engineered to inundate the resources of a system to such an extent that it becomes incapable of responding to valid service requests. A distributed denial-of-service (DDoS) attack shares the objective of depleting the resources of a targeted system. A Distributed Denial of Service (DDoS) assault is launched across a diverse range of host machines that have been infected with malware and are under the control of the attacker. These attacks are commonly known as “denial of service” attacks, as they render the victim site incapable of delivering services to users seeking access.
A Denial of Service (DoS) attack involves overwhelming the target website with a high volume of fraudulent requests. Due to the necessity of the website to address every request, its resources are depleted by the cumulative responses. This phenomenon renders the website incapable of providing its usual services, frequently leading to a full cessation of its operations.
Denial of Service (DoS) and Distributed Denial of Service (DDoS) assaults are distinct from other forms of cyber attacks in that they facilitate unauthorized system access acquisition or the expansion of existing access privileges by hackers. In the context of these attacks, the perpetrator derives immediate advantages from their endeavors. On the contrary, DoS and DDoS network assaults aim to disrupt the operational efficiency of the targeted service. If the perpetrator is employed by a commercial rival, they could potentially get financial gains from their actions.
A Denial of Service (DoS) attack can also be used to exploit vulnerabilities for another form of attack. Following a successful Denial of Service (DoS) or Distributed Denial of Service (DDoS) assault, it is common for the targeted system to be forced offline, making it susceptible to additional forms of malicious attacks. A commonly employed strategy for mitigating Denial-of-Service (DoS) assaults involves the implementation of a firewall system that possesses the capability to discern the authenticity of incoming requests directed toward a certain website. Subsequently, imposter requests can be disregarded, enabling the unobstructed flow of regular traffic. An instance of a significant cyber assault of this nature transpired in February 2020, targeting Amazon Web Services (AWS).
2. Man-in-the-Middle Attacks
The Man-in-the-middle (MITM) cyber attack variants pertain to cybersecurity compromises, enabling an assailant to intercept and monitor the exchanged data between two individuals, networks, or computing systems. The term “man in the middle” attack is derived from the attacker’s strategic placement between two communicating parties. The perpetrator is effectively engaging in surveillance of the communication between the two entities.
During a Man-in-the-Middle (MITM) attack, the two entities engaged in communication experience a sense of normalcy in their interaction. Unbeknownst to them, the individual responsible for transmitting the message engages in unauthorized manipulation or interception of the communication prior to its arrival at the intended recipient. There are several measures that can be used to safeguard oneself and one’s organization from Man-in-the-Middle (MITM) attacks. These include the utilization of robust encryption protocols on access points, as well as the adoption of a virtual private network (VPN) for enhanced security.
3. Phishing Attacks
A phishing assault is a deceptive tactic employed by hostile individuals who send fraudulent emails that mimic the appearance of reputable and trustworthy sources with the intention of illicitly obtaining sensitive information from the recipient. Phishing attacks are characterized by the integration of social engineering techniques and technology. The term “phishing” is derived from the analogy of an attacker engaging in a metaphorical act of “fishing” to gain unauthorized access to a restricted area, employing the deceptive “bait” of an apparently reliable sender.
In order to carry out the attack, the malicious individual may provide a hyperlink that redirects the user to a webpage designed to deceive them into unwittingly acquiring malicious software, such as viruses, or inadvertently disclosing their confidential information to the attacker. In several instances, the affected individual may lack awareness of their compromised state, enabling the assailant to target further members inside the organization without arousing suspicion of malevolent conduct.
Phishing attempts can be thwarted by employing discernment when selecting which emails to open and which links to click on. It is imperative to exercise vigilance when examining email headers, refraining from interacting with any elements that are dubious in nature. Please verify the settings associated with the “Reply-to” and “Return-path” fields. It is necessary for them to establish a connection with the identical domain as presented in the email.
4. Whale-phishing Attacks
The term “whale-phishing attack” is derived from its targeting of high-profile individuals within a company, sometimes referred to as “whales.” These individuals typically hold positions in the C-suite or possess significant authority within the organization. These persons are prone to possess information that may hold value for potential attackers, including proprietary information pertaining to the firm or its operations.
In the case that a specifically targeted individual, sometimes referred to as a “whale,” becomes a victim of ransomware, there is an increased probability of them acquiescing to the ransom demands. This inclination arises from their desire to avert the dissemination of information regarding the successful cyber assault, which might potentially inflict harm upon their personal or organizational reputation. Whale phishing assaults can be mitigated through the implementation of similar precautionary measures employed to counter phishing attacks. These measures include diligently scrutinizing emails, attachments, and URLs while remaining vigilant for any indications of dubious destinations or characteristics.
5. Spear-phishing Attacks
The term “spear phishing” is used to describe a distinct form of phishing attack that is aimed at specific individuals or groups. The assailant invests effort in conducting thorough research on their prospective victims, subsequently composing messages that are highly tailored to resonate with the individual targets. These assaults are commonly referred to as “spear” phishing due to the attacker’s focused targeting of a specific individual or entity. Identifying a spear-phishing attack might be challenging due to the perceived authenticity of the message.
Frequently, spear-phishing attacks employ the technique of email spoofing, wherein the content within the “From” field of the email is manipulated, creating a false appearance that the email originates from a different sender. The potential candidates for establishing trust with the target individual are those inside their social network, close acquaintances, or business associates. In addition, perpetrators may employ the technique of website cloning in order to create an illusion of authenticity in their communication. Website cloning is the replication of a genuine website by an attacker with the intention of inducing a false sense of security in the target. The individual, on the assumption that the website is authentic, then experiences a sense of ease and proceeds to disclose their personal information.
Just like conventional phishing attempts, spear-phishing assaults can be mitigated by diligently scrutinizing the information provided in all sections of an email and refraining from clicking on any hyperlink whose authenticity cannot be verified.
6. Ransomware
Ransomware is a type of malicious software that restricts access to a victim’s machine until a ransom is paid to the perpetrator. Once the payment has been transmitted, the assailant proceeds to furnish the victim with information pertaining to the process of regaining control over their computer. The term “ransomware” is fitting as it accurately describes a type of malware that extorts a ransom from its targeted individual or organization.
During a ransomware attack, the intended victim inadvertently acquires ransomware, either by accessing a malicious website or by opening an email attachment containing the malware. The malware has been specifically designed to take advantage of vulnerabilities that have not yet been resolved by either the maker of the system or the IT department. Subsequently, the ransomware proceeds to encrypt the workstation of the targeted entity. In certain instances, ransomware can be employed as a means of targeting several entities by obstructing access to either numerous computer systems or a pivotal central server that is critical to the functioning of commercial activities.
The act of impacting many computer systems is frequently achieved by deliberately delaying the activation of system infiltration until several days or even weeks following the initial penetration of the malware. The malware possesses the capability to transmit AUTORUN files across interconnected systems through either the internal network or Universal Serial Bus (USB) drives that establish connections with many machines. Subsequently, upon the attacker’s initiation of the encryption process, it operates concurrently on all compromised systems.
In several instances, the creators of ransomware deliberately construct the programming code in a manner that enables it to circumvent conventional antivirus protection. Hence, it is crucial for consumers to exercise caution in selecting websites to visit and hyperlinks to click on. One effective measure to mitigate numerous ransomware attacks is the utilization of a next-generation firewall (NGFW) equipped with advanced capabilities. This NGFW is capable of conducting thorough data packet inspections by leveraging artificial intelligence (AI) algorithms, which are designed to identify and analyze the distinguishing features associated with ransomware.
7. Password Attack
Passwords are widely used as a means of access verification by the majority of individuals. Consequently, discovering the password of a target is an appealing prospect for a hacker. There are several approaches available to accomplish this task. Frequently, individuals store duplicates of their passwords on physical media such as paper or sticky notes in close proximity to or within their workspaces. In the context of unauthorized access to a system, someone with malicious intent has two potential avenues for obtaining a password: either by independently discovering it or by engaging in a transactional arrangement with an insider who possesses the password.
In addition to other malicious activities, an assailant may attempt to intercept network traffic in order to obtain passwords that have not been encrypted by the network. In addition, social engineering techniques may be employed, whereby the target is manipulated into disclosing their password under the guise of resolving a potentially significant issue. In certain instances, the perpetrator may employ the strategy of guessing the user’s password, especially if the user has chosen a default password or one that is easily memorable, such as “1234567.”
In addition, perpetrators frequently employ brute-force techniques in order to make educated guesses for passwords. The brute-force method of password hacking involves employing rudimentary knowledge about an individual or their occupational designation in an attempt to ascertain their password. For instance, the utilization of personal information such as an individual’s name, birthdate, anniversary, or other easily accessible characteristics can be employed in many permutations to decrypt their password. The data shared by individuals on social media platforms can potentially be exploited as a means to carry out a brute-force password attack. Passwords that are formed using personal information such as an individual’s recreational activities, specific hobbies, names of pets, or names of children might be susceptible to being easily guessed by brute-force attackers.
A hacker may employ a dictionary attack as a means to determine a user’s password. The dictionary attack is a method employed to ascertain a target’s password by utilizing commonly used words and phrases typically found in a dictionary.
An efficacious approach to mitigating brute-force and dictionary password attacks involves implementing a lock-out policy. This security feature restricts entry to devices, websites, or applications by implementing an automated mechanism that disables access following a certain threshold of unsuccessful login attempts. By implementing a lock-out policy, the potential intruder is limited to a certain number of attempts before being prohibited from further access. In the event that an existing lockout policy is in effect and an individual’s account becomes locked due to excessive login attempts, it is advisable to modify the password.
In the event that an assailant employs a methodical approach such as a brute-force or dictionary assault to make educated guesses at your password, it is plausible that they will make a record of the passwords that proved unsuccessful. For instance, in the event that an individual’s password consists of their surname followed by their year of birth, and unauthorized individual attempts to input the birth year before to the surname during the last endeavor, there exists a possibility that they may successfully guess the password in the subsequent effort.
8. SQL Injection Attack
SQL injection is a prevalent technique employed to exploit websites that rely on databases for user interaction. Clients refer to computer systems that retrieve data from servers. An SQL attack involves the utilization of a SQL query transmitted from the client to a database residing on the server. The instruction is introduced, or “injected,” into a data plane as a substitution for a conventional element, such as a password or login. The database server executes the command, resulting in a successful system penetration.
In the event of a successful SQL injection, various consequences may arise, such as the unauthorized disclosure of confidential information or the unauthorized alteration or removal of critical data. Moreover, a malicious actor has the capability to perform administrative tasks, such as initiating a shutdown command, potentially disrupting the normal operation of the database.
In order to mitigate the risk of a SQL injection attack, it is advisable to employ the least-privileged model. The least-privileged architecture restricts access to important databases exclusively to individuals who possess an essential necessity to do so. In instances where a user possesses authority or sway within the organizational structure, their access to certain sections of the network may be restricted if their job responsibilities do not necessitate such privileges.
An instance of restricting the CEO’s access to some network locations, although possessing the requisite authorization to access the contents inside, can be observed. The implementation of a least-privileged policy serves as a preventive measure against unauthorized access to sensitive regions. This policy not only safeguards against malicious individuals but also protects well-intentioned individuals who may inadvertently expose their login credentials to potential attackers or leave their workstations unattended.
9. URL Interpretation
URL interpretation is the manipulation and falsification of certain URL addresses by malicious actors, who exploit this technique to illicitly get sensitive personal and professional information belonging to their targets. This form of attack is commonly known as URL poisoning. The term “URL interpretation” is derived from the understanding that the attacker has knowledge of the specific sequence in which the URL information of a webpage should be inputted. Subsequently, the assailant proceeds to “interpret” the aforementioned syntax, employing it as a means to gain unauthorized entry into restricted domains.
In order to carry out a URL interpretation attack, an unauthorized individual may engage in the act of speculating potential URLs that might be exploited to acquire administrative privileges on a website or to infiltrate the website’s backend system with the intention of compromising a user’s account. Upon reaching the desired webpage, individuals possess the ability to interact with the site’s interface or acquire confidential data pertaining to its users.
As an illustration, in the event that an unauthorized individual endeavors to gain access to the administrative area of a website named GetYourKnowledgeOn.com, they may input the URL http://getyourknowledgeon.com/admin, which will thereafter direct them to an administrative login page. In certain instances, the administrative login and password may consist of the default values “admin” and “admin” or exhibit a level of simplicity that renders them highly susceptible to guessing. The potential assailant may have already deduced the administrator’s password or significantly reduced the number of potential passwords. Subsequently, the assailant proceeds to systematically test each potential entry point, successfully breaches the system’s defenses, and subsequently acquires the capability to corrupt, pilfer, or eradicate data at their discretion.
In order to mitigate the risk of URL interpretation attacks, it is advisable to employ robust authentication mechanisms for all critical sections of your website. This may require the implementation of multi-factor authentication (MFA) or the use of strong passwords composed of seemingly random characters.
10. DNS Spoofing
Domain Name System (DNS) spoofing involves the manipulation of DNS records by a malicious actor, resulting in the redirection of network traffic towards a counterfeit or “spoofed” website. Upon accessing the deceptive website, the individual may inadvertently disclose confidential data, which can subsequently be exploited or traded by the unauthorized party. The hacker may also create a website of substandard quality, with insulting or provocative information, with the intention of tarnishing the reputation of a rival company.
In a DNS spoofing attack, the assailant capitalizes on the user’s perception that the website they are accessing is authentic. This grants the assailant the capacity to engage in unlawful activities under the guise of a blameless organization, at least as perceived by the individual visiting the website.
In order to mitigate the risk of DNS spoofing, it is imperative to ensure that the DNS servers are regularly updated. The primary objective of attackers is to exploit vulnerabilities present in DNS servers. It is worth noting that the latest software versions frequently incorporate patches that effectively address identified vulnerabilities.
11. Session Hijacking
Session hijacking is considered to be one among several types of Man-in-the-Middle (MITM) attacks. The assailant assumes control of a communication session occurring between a client and a server. In the context of the attack, the computer employed by the perpetrator assumes the Internet Protocol (IP) address of the client computer, deceiving the server into maintaining the session under the false assumption that it is interacting with the legitimate client rather than the attacker. The efficacy of this type of attack stems from the server’s reliance on the client’s IP address as a means of authentication. In the event that the IP address of the attacker is introduced during an ongoing session, the server’s awareness of a potential security breach may be hindered due to its involvement in a pre-established and trusted connection.
In order to mitigate the risk of session hijacking, it is recommended to employ a Virtual Private Network (VPN) as a means of accessing servers that are essential to the operations of a business. In this manner, all forms of communication are subjected to encryption, thereby preventing unauthorized access to the secure tunnel established by the virtual private network (VPN).
12. Brute force attack
The term “brute-force attack” derives its origin from the rudimentary or straightforward tactics utilized by the attack. The assailant employs a method of attempting to ascertain the login credentials of an individual who possesses authorization to access the designated system. Once individuals successfully achieve the desired outcome, they are granted access or inclusion.
Although it may appear to be a laborious and challenging task, perpetrators frequently employ automated programs known as bots to obtain access to user credentials illicitly. The perpetrator furnishes the automated program with a compilation of credentials that they believe would grant them entry into the restricted zone. Subsequently, the automated system proceeds to test each option while the assailant assumes a passive role and awaits the outcome. Upon successful input of the appropriate credentials, the perpetrator attains unauthorized entry.
In order to mitigate the risk of brute-force attacks, it is advisable to incorporate lock-out restrictions within the framework of your authorization security architecture. Upon reaching a specific threshold of unsuccessful tries, the user endeavoring to input their credentials experiences a state of being locked out. This process often entails “freezing” the account to prevent any attempts made by others using different devices or IP addresses from circumventing the lockout.
It is advisable to employ randomized passwords that do not contain common phrases, dates, or numerical sequences. This approach demonstrates efficacy as it illustrates that even in the event of an attack when an assailant employs software to make attempts at guessing a 10-digit password, the considerable amount of time required for successful completion would span several years of continuous efforts.
13. Web Attacks
Web assaults are a category of security risks that specifically exploit weaknesses found inside web-based systems. Whenever an individual inputs data into a web-based application, they are essentially triggering a command that prompts the system to produce a corresponding answer. As an illustration, when initiating a monetary transfer through an online banking platform, the information provided by the user serves as instructions for the program to access their account, withdraw funds, and subsequently transmit them to the designated recipient’s account. Adversaries operate within the parameters of such requests and exploit them for their own benefit.
This essay will later examine two prevalent web threats, namely SQL injection and cross-site scripting (XSS). In addition to employing cross-site request forgery (CSRF) assaults and parameter tampering, hackers also utilize these techniques. A Cross-Site Request Forgery (CSRF) attack involves the manipulation of a victim into unknowingly executing an activity that ultimately serves the interests of the attacker. As an illustration, users may initiate an action that triggers a script specifically developed to modify the login credentials required for accessing a web application. With the acquisition of the updated login credentials, the hacker gains the ability to access the system under the guise of the authorized user.
Parameter tampering refers to the act of modifying the parameters that have been implemented by programmers as security measures, with the intention of undermining or bypassing the safeguards put in place to secure certain processes. The execution of the procedure is contingent upon the input provided in the parameter. The perpetrator effectively modifies the settings, circumventing the security systems that rely on such parameters.
In order to mitigate the risk of web attacks, it is imperative to conduct thorough examinations of web applications to identify and rectify any existing vulnerabilities. One potential strategy for mitigating vulnerabilities in a web application while minimizing performance effects involves the implementation of anti-CSRF tokens. A token is transferred between the user’s web browser and the web application. Prior to the execution of a command, the authenticity of the token is verified. If the command is verified, it is executed; otherwise, it is denied. Another approach that can be employed is the utilization of SameSite flags. These flags restrict the processing of requests just to those originating from the same site, effectively neutralizing any potential influence exerted by an attacker’s constructed site.
14. Insider Threats
On certain occasions, it is seen that the most perilous individuals emerge from within the confines of an organization. Individuals who are employed by a corporation present a distinct risk because to their inherent access to various systems and, in certain instances, administrative powers that grant them the authority to make significant alterations to the system or its security protocols.
Furthermore, individuals within the organizational structure frequently possess a comprehensive comprehension of the cybersecurity framework in place, along with a profound awareness of the organization’s response mechanisms to potential attacks. This knowledge has the potential to facilitate unauthorized entry into restricted locations, manipulate security configurations, or determine the optimal timing for executing an attack.
One effective strategy for mitigating insider threats within firms involves implementing access restrictions for employees and granting system privileges just to individuals whose job responsibilities necessitate such access. In addition, for a limited number of individuals who require authorization, the implementation of Multi-Factor Authentication (MFA) is recommended. This security measure necessitates the use of both knowledge-based authentication and possession of a physical item in order to get access to a sensitive system. As an illustration, the user may be required to input a password and connect to a USB device. In other arrangements, a handheld device generates an access number that necessitates user authentication. Access to the secure area is contingent upon the accurate input of both the password and the numerical value.
Although the implementation of MFA may not provide a foolproof defense against all types of assaults, it does facilitate the identification of the perpetrators of an attack or an attempted attack. This is mostly due to the limited number of individuals who are authorized to access sensitive areas initially, thereby narrowing down the pool of potential suspects. Consequently, this tactic of limited access can function as a deterrent. Within a business, cybercriminals possess the knowledge that identifying the offender is a straightforward task due to the limited number of viable suspects.
15. Trojan Horses
A Trojan horse assault employs malevolent software that is concealed within an ostensibly authentic program. Upon the execution of the program by the user, the concealed malicious software within the Trojan possesses the capability to establish an unauthorized access point, commonly referred to as a backdoor, into the targeted system. This illicit entry point can then be used by hackers to infiltrate the compromised computer or network. The nomenclature of this menace derives from the narrative of the Hellenic warriors who clandestinely concealed themselves under an equine structure, therefore effectuating an infiltration of the fortified city of Troy, ultimately culminating in their triumph in the conflict. Upon the acceptance and subsequent entry of the “gift” into the confines of Troy, the Greek warriors swiftly emerged and launched an assault. Similarly, an unknowing user may inadvertently allow an innocuous-looking application to enter their system, introducing a concealed hazard.
In order to mitigate the risk of Trojan assaults, it is imperative to provide users with clear instructions to refrain from downloading or installing any software or files unless the authenticity and trustworthiness of the source can be verified. Additionally, Next-Generation Firewalls (NGFWs) include the capability to analyze data packets in order to identify potential Trojan attacks.
16. Drive-by Attacks
During a drive-by attack, an unauthorized individual infiltrates an inadequately secured website by implanting harmful code. Upon a user’s visit to the website, the script is immediately performed on their machine, resulting in its infection. The term “drive-by” is derived from the observation that the victim can become infected just by passing by the website and visiting it. There is no necessity to engage in any type of interaction, such as clicking on elements or providing personal information, on the website in question.
In order to mitigate the risk of drive-by attacks, it is imperative for users to ensure that they are utilizing the latest software versions across all their computer systems. This includes updating apps such as Adobe Acrobat and Flash, which are commonly employed during internet browsing activities. Additionally, the utilization of web-filtering software can enable the detection of potentially hazardous websites prior to user access.
17. XSS Attacks
Cross-site scripting (XSS) involves the transmission of malicious scripts by an attacker through clickable material, which is subsequently delivered to the browser of the targeted individual. Upon the victim’s interaction with the material, the script is triggered and then executed. The web application considers the input provided by the user as legitimate due to their prior authentication and session establishment. Nevertheless, the executed script has undergone modification by the assailant, leading to an inadvertent action being carried out by the individual referred to as the “user.”
An instance of a cross-site scripting (XSS) attack has the potential to modify the parameters of a transfer request that is transmitted over an online banking application. In the fraudulent solicitation, the designated beneficiary of the monetary transfer undergoes a substitution of their name with that of the perpetrator. The perpetrator has the potential to modify the sent amount, obtaining a greater sum of money than originally planned by the recipient.
Utilizing a whitelist of permissible entities is a highly effective approach to mitigating cross-site scripting (XSS) attacks. In this manner, the online application will only accept inputs that have been approved, disregarding any other submissions. Another strategy that can be employed is known as sanitizing when the data being inputted is thoroughly analyzed to identify any potentially hazardous elements.
18. Eavesdropping Attacks
Eavesdropping attacks pertain to the unauthorized interception of network traffic by a malicious entity. Through this method, a malicious actor has the ability to gather user identifiers, passwords, and other sensitive data, such as credit card details. The act of eavesdropping can be categorized into two forms: aggressive eavesdropping and passive eavesdropping.
Active eavesdropping is the deliberate insertion of software by a hacker into the pathway of network traffic. This software is designed to intercept and gather information, which the hacker subsequently analyzes in order to extract usable data. Passive eavesdropping attacks are distinguished by the hacker’s engagement in the act of “listening in” or eavesdropping on transmissions with the intention of identifying and appropriating valuable data.
Both active and passive eavesdropping can be classified as forms of Man-in-the-Middle (MITM) attacks. One effective method for mitigating such risks is the implementation of data encryption techniques, which serve to safeguard sensitive information against unauthorized access or utilization by malicious actors, irrespective of their utilization of active or passive eavesdropping techniques.
19. Birthday Attack
The birthday attack involves the exploitation of hash algorithms, which serve the purpose of verifying message authenticity, by an adversary. The hash algorithm serves as a digital signature, which the recipient of the message verifies before accepting it as genuine. In the event that a hacker is capable of generating a hash value that matches the one appended by the sender to their message, the hacker can effortlessly substitute the original message with their own. The receiving device will successfully receive the transmitted data due to the presence of a matching hash value.
The term “birthday attack” is derived from the birthday paradox, a phenomenon that arises from the statistical likelihood of two individuals sharing the same birthday in a group of 23 persons exceeding 50%. Therefore, it may be argued that although individuals perceive their birthdays to be unique, like hashes, the level of uniqueness is not as substantial as commonly believed.
In order to mitigate the risk of birthday attacks, it is advisable to employ longer hash functions for the purpose of verification. As the number of digits in the hash increases, the probability of generating a matching hash decreases substantially.
20. Malware Attack
The term “malware” encompasses a broad category of software that is specifically designed to be malicious, as indicated by the prefix “mal-” in its name. Malicious software, commonly referred to as malware, has the capability to infiltrate a computer system and alter its normal operations, potentially resulting in data loss, unauthorized surveillance of the user, or interception of network traffic. Malware has the capability to propagate between devices or persist within a single device, exerting its effects solely on the host system.
A variety of attack techniques, including MITM attacks, phishing, ransomware, SQL injection, Trojan horses, drive-by attacks, and XSS assaults, may incorporate different types of malware.
During a malware assault, the installation of the malicious software is required on the targeted device. The completion of this task necessitates active engagement from the user. Hence, apart from employing malware-detecting firewalls, it is imperative to provide users with proper education on software to steer clear of, links to verify prior to opening, and emails and attachments to refrain from interacting with.
How News4Hackers Can Help?
The suite of cybersecurity capabilities offered by Craw Security, a subsidiary of News4Hackers, is capable of mitigating a wide range of assaults, including those mentioned and others. The Craw Security integrates cyber threat intelligence, as well as hardware and software components, to enhance the effectiveness of your security solution, enabling it to counter a diverse array of attacks effectively. The security solutions offered by Craw Security encompass comprehensive protection for all network endpoints, spanning from the edge to the core. These solutions not only provide insight into the network but also offer automated reactions to ensure the security of all endpoints that are connected.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager entered the field of content in an unusual way. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.
Read More Blogs Here







