10 Best Anti-Phishing Tools and Services

Certain technologies can effectively identify and mitigate the impact of phishing emails, thereby preventing potential harm. Additionally, other measures can be employed to detect instances where malicious actors exploit your business’s brand for fraudulent purposes.
The utilization of phishing remains a prominent method employed by malicious individuals who possess diverse objectives. This is mostly due to the ease of initiating phishing assaults and the inherent challenges associated with providing comprehensive protection against them. Certain phishing attacks specifically focus on targeting consumers instead of employees, while others have the sole objective of tarnishing your corporate reputation rather than infiltrating your systems. One crucial aspect in safeguarding a business against phishing is to comprehend its weaknesses, assess the possible risk posed to the business, and determine the most effective protective measures that align with the specific requirements of the business.
What Are Anti-Phishing Tools and How Do They Work?
By automatically recognizing and eliminating suspicious activity, links, attachments, and communications, anti-phishing systems shield people and organizations from phishing attempts. The following are some typical categories of anti-phishing tools:
| Email filters | Email filtering programs examine many elements of an email, including the sender, subject line, content, attachments, and embedded links, in order to detect dangers, flag questionable emails as spam, and either delete or block them. |
| Anti-virus software | Malicious attachments or links in emails that lead to phishing websites can be found and blocked with the use of this program. It employs heuristics to find novel, unidentified threats and signature-based detection to match recognized threats. Additionally, it can check incoming emails for viruses that could be used in phishing scams. |
| Authentication solutions | By requiring users to supply two kinds of identity, such as a password and an SMS code or biometrics, authentication solutions like multifactor authentication (MFA) promise an additional layer of security against phishing attempts. By sending a special code to the user’s phone, SMS-based MFA makes it more difficult for hackers to access accounts. Additionally, passwordless authentication lowers the danger of phishing and credential theft by doing away with passwords through the use of biometrics or push notifications.
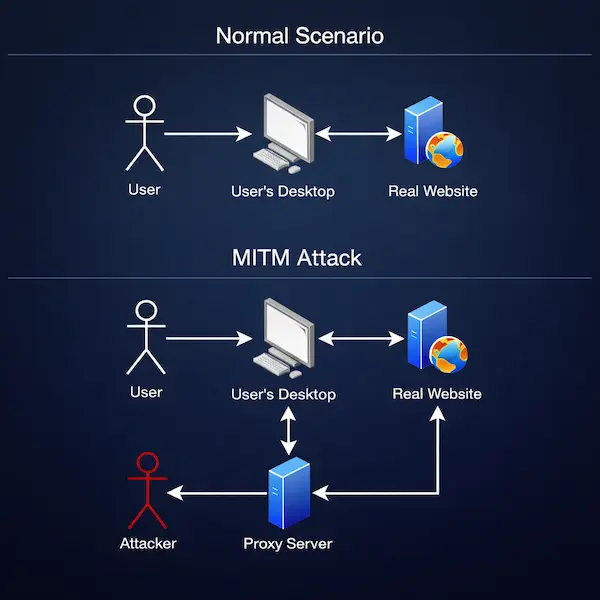
Even with its widespread use, MFA is still susceptible to man-in-the-middle attacks (MitM), which can get around it in a number of ways. Consumers could not even be aware of MFA bypass events and might not report incidents, which would leave the affected business with only damage control once prevention is no longer an option.
Preventive solutions that incorporate proactive real-time measures are being used by scam-prone businesses to combat MFA bypass and lower incidents and associated costs. |
Why is phishing successful?
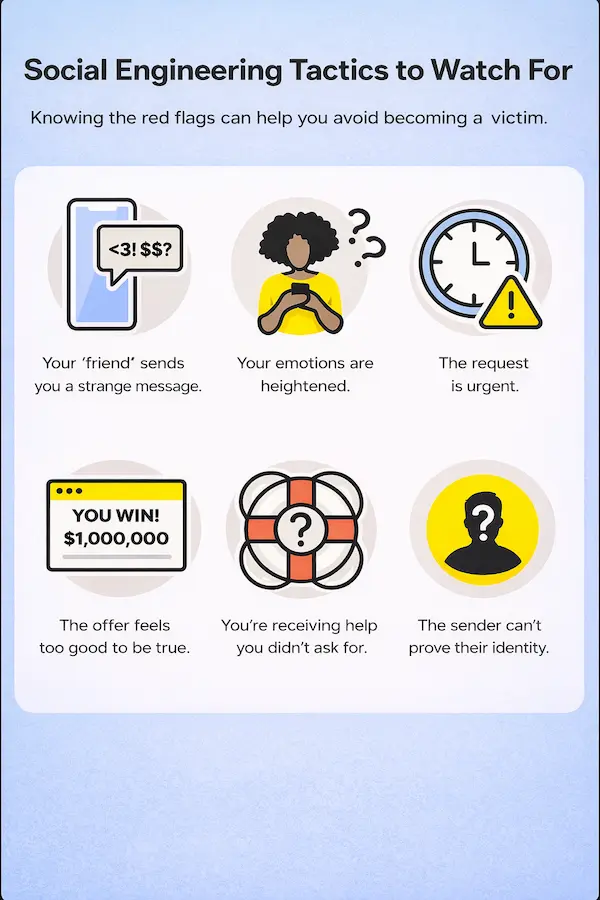
The primary focus of phishing assaults tends to revolve around social engineering rather than technological aspects. The susceptibility of humans to manipulation is remarkable when emotions are effectively stimulated. Numerous contemporary phishing emails exploit emotions such as empathy or fear and occasionally employ hostile allegations with the intention of eliciting an angry reaction.
One additional factor contributing to the widespread success of phishing is its versatility in causing disruption to targeted entities. This is exemplified by its ability to hinder human productivity through the necessity of manual validation of message contents or involvement of corporate IT. Furthermore, phishing poses a threat to financial accounts and enterprise systems, frequently resulting in ransomware attacks. Conversely, the prevention of phishing poses challenges due to the potential disruption of real business communication caused by false positives.
How to protect your business against phishing?
One crucial aspect of safeguarding one’s organization, employees, and customers against phishing assaults involves utilizing established industry standards and adopting optimal practices wherever feasible. Standards such as Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC) have been developed with the purpose of combating the widespread issue of SPAM. These standards enable recipient email servers to verify the authenticity of the servers from which they receive emails. In other words, the objective of these standards is to guarantee that mail servers asserting to transmit messages on behalf of your domain possess the necessary authorization to do so. Each of these standards is rooted in the Domain Name System (DNS) and can be implemented with relative ease.
Indeed, it is highly likely that individuals obtain their email services from a provider such as Google or Microsoft, wherein these services incorporate contemporary implementations of the aforementioned standards. Email services offered by professionals already offer a certain degree of security against phishing attempts. However, these services are not flawless, hence creating a demand for alternative solutions on the market.
One prominent method of attack focuses on the acquisition of information using low-tech means, specifically by exploiting email answers. Content controls offered by commercial productivity platforms like Microsoft 365, Google Workspace, and third-party vendors play a crucial role in thwarting the successful execution of such attacks. Content policies are implemented to automate the process of identifying crucial categories of information, such as credit card or bank account numbers, social security numbers, and other sensitive data that necessitates strict protection. These policies serve the purpose of preventing the transmission of such information beyond the confines of the company.
The primary concern for most organizations regarding phishing attempts is the potential vulnerability of their systems, which can ultimately lead to financial or data loss and, in some cases, even ransomware. Therefore, it is imperative to implement a robust multi-factor authentication (MFA) system as the principal defense mechanism. This can be achieved by adopting authentication standards, such as Fast Identity Online v2 (FIDO2) or Web Authentication (WebAuthn). Ideally, organizations should consider enhancing their security measures by implementing multi-factor authentication (MFA) and advancing towards password-less authentication, using the principles of zero-trust. Contemporary authentication solutions, such as risk-based authentication and Security Assertion Markup Language (SAML), serve as effective measures in mitigating the potential consequences resulting from a successful phishing assault. Each of these components plays a crucial role within an organization, offering dual advantages. Firstly, the potential harm caused by a compromised password is significantly reduced, if not completely eliminated. Secondly, these components establish mechanisms to analyze authentication attempts and promptly respond to compromised credentials in real time.
Top Anti-Phishing Tools
There exists a diverse range of tools that can be utilized to safeguard businesses from the various hazards posed by phishing attacks on their organizational infrastructure. Understanding the available solutions and their potential to safeguard one’s organization, employees, and consumers constitutes a significant aspect of addressing this challenge.
1. Avanan

Avanan provides cloud-hosted email users with anti-phishing software that integrates with their email provider through APIs. This integration allows Avanan to utilize past email data to train its artificial intelligence algorithms. The service does an analysis that encompasses not only the contents, formatting, and header information of messages but also evaluates the pre-existing relationships between senders and receivers in order to determine a measure of trust.
2. Barracuda Sentinel
Barracuda Sentinel is an additional software application that utilizes application programming interfaces (APIs) of mail providers in order to provide protection against phishing attempts, as well as mitigate the risks associated with business email compromise (BEC). The prioritization of mitigating subsequent harm resulting from successful phishing attempts, rather than depending exclusively on prevention, holds greater significance for Barracuda due to the tendency of compromised email accounts to facilitate additional phishing attempts or account-based assaults. Barracuda offers brand protection and domain fraud prevention by means of DMARC analysis and reporting.
3. PhishNext by Craw Security

Enterprise-grade phishing detection is brought straight to your email interface with PhishNext, a lightweight browser extension. In contrast to intricate server-side alternatives, our product offers instant visual threat indicators next to each email, integrating smoothly with your workflow. PhishNext provides real-time protection without interfering with your email experience by using sophisticated AI analysis of headers, content, and sender behavior. It is a straightforward Chrome extension that requires no configuration and gives instantaneous actionable intelligence, automatic batch scanning, and analysis history maintenance to avoid unnecessary checks.
4. BrandShield

BrandShield is a specialized company that is dedicated to safeguarding the corporate brand and the personal brands of executives. One aspect of BrandShield’s portfolio involves the identification of phishing assaults that exploit your brand or the identities of your executives, whether through email, social media, or other communication channels. BrandShield is capable of monitoring various online platforms, including the internet and marketplaces such as Amazon, in order to identify unauthorized websites that exploit your brand and detect instances where counterfeit physical objects bearing your brand may be offered for sale.
5. Cofense PDR

Cofense PDR (Phishing Detection and Response) is a managed service that combines the utilization of AI-based solutions with security specialists to effectively detect and respond to phishing assaults in real time. Utilizing managed services can prove advantageous for individuals seeking to optimize their degree of safety, as they often exhibit superior efficacy compared to the employment of a dedicated in-house team only focused on phishing avoidance. This is mostly due to the managed services team’s ability to comprehensively assess threat data originating from all corporate systems under their safeguard.
6. RSA FraudAction

The RSA FraudAction anti-phishing solution is evidently provided by a prominent entity in the field of network security. The range of capabilities provided aligns with the expectations associated with a very influential player in the industry. The anti-phishing service provided by Cofense is a form of managed service. RSA, on the other hand, offers additional features such as site shutdown, forensics, and optional countermeasures. These countermeasures involve strategically responding to phishing attempts by planting credentials, which allows for tracking of the attack chain and appropriate response.
7. IRONSCALES

IRONSCALES is an email security platform designed to enhance the effectiveness of your current email system by employing dynamic detection and analysis techniques. This includes the ability to block, flag, or apply a banner to emails that may be deemed potentially suspicious. IRONSCALES provides end-user training that specifically targets email security and general awareness. This training aims to enhance your defense mechanisms against the primary component of phishing attacks, namely social engineering tactics.
8. KnowBe4

KnowBe4 proudly appoints Kevin Mitnick, a prominent figure in the field of hacking, as its Chief Hacking Officer. A significant portion of Mitnick’s endeavors revolved around the practice of social engineering, and the company’s operations align with this emphasis by prioritizing the facilitation of enhanced decision-making among employees through educational means. In addition to their highly regarded awareness training, KnowBe4 also provides PhishER, a Security Orchestration, Automation, and Response (SOAR) platform that focuses on phishing endeavors. This platform empowers security teams to enhance their responsiveness to email-based attacks targeting their organization, hence improving overall efficiency.
9. Mimecast

Mimecast provides a range of solutions designed to mitigate the risks associated with phishing attacks. These tools encompass various aspects that enable the detection of malicious links and attachments. Upon detection, these elements are either removed or rendered safe through the implementation of advanced techniques such as sandboxing. Mimecast possesses the capability to effectively thwart code-based attacks that are instigated by phishing emails or more advanced techniques, such as QR codes, achieved by accessing URLs within the Mimecast cloud. This streamlined deployment approach guarantees that protection measures remain consistently updated to the most current standards.
10. Microsoft Defender for Office 365

Microsoft Defender for Office 365 has comparable functionalities to certain products mentioned in this compilation, encompassing user education, identification and mitigation of phishing attempts, examination of digital evidence and determination of underlying causes, and even proactive pursuit of potential threats. Due to its status as an add-on for Office 365, Defender exhibits a high level of integration that does not necessitate any initial configuration. Microsoft also provides preconfigured security rules that may be customized according to individual requirements. These policies facilitate the implementation of enforcement measures, allow users to override certain settings, and enable the tracking of policy modifications over a period of time. This service offers distinct benefits to Office 365 customers while presenting specific drawbacks for individuals who are not part of this customer base.
Key Features of Anti-Phishing Tools
The following features should preferably be combined in specialized anti-phishing software:
| Real-time detection | Phishing attempts are detected and blocked in real time by continuously monitoring incoming emails and online traffic. |
| ML-based analysis | ML-based research to spot trends in phishing attempts. |
| Proactive ATO protection | Proactive ATO prevention to thwart attempts at card data theft and credential theft in real time. |
| Deny lists and safe lists | To keep an up-to-date database of known phishing websites and email addresses, use safe lists and deny lists. |
| Integration with other security systems | Integration with other security systems to enhance risk engine models for better fraud predictions and deliver actionable, real-time intelligence. |
| Detailed reports and analytics | Comprehensive reporting and analytics on phishing attempts, including the target, the attack type, and the attacker’s origin. |
Conclusion
In the bottom line, we would like to state that we have tried our level best to mention and elaborate on the 10 Best Anti-Phishing Tools and Services. However, there are many more anti-phishing tools and services that are genuinely available in the current market scenarios. If a person has a mindset to take some of the prominent anti-phishing tools and services from the highlighted VAPT Solutions Providers in India, such as Craw Security, a sister vertical of News4Hackers, which is dedicatedly working as the Best VAPT Services Company in India and other reputed nations worldwide, they can opt for Craw Security.
For more information on any particular cybersecurity service in India or any other country of the world, you can contact their hotline mobile number at +91-9513805401 and have a word with our superb penetration testers.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager unusually entered the field of content. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.
Read More Article Here