A Romance Scam Patchwork Lures To Infect Android Devices with the VajraSpy Malware
A Romance Scam Patchwork Lures To Infect Android Devices with the VajraSpy Malware
Patchwork likely enticed victims in Pakistan and India with romance fraud lures in order to infect their Android devices with VajraSpy, a remote access trojan.
ESET, a Slovak cybersecurity firm, disclosed the discovery of twelve espionage applications between April 2021 and March 2023. Among these, six were accessible for installation from the official Google Play Store and accumulated a total of over 1,400 downloads.

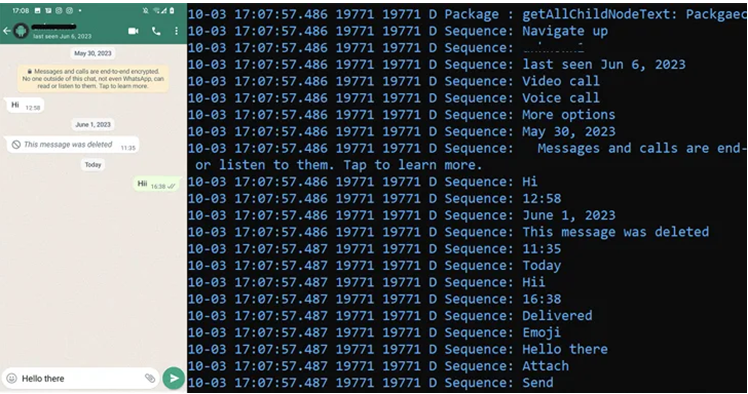
Security researcher Lukáš Štefanko stated, “VajraSpy possesses a variety of espionage capabilities that are expandable depending on the authorizations allowed to the application bundled with its code.” “It obtains contacts, files, call logs, and SMS messages, but a few of its methods may additionally collect WhatsApp and Signal messages, record phone calls, and take pictures with the camera.”

It is estimated that a maximum of 148 devices in Pakistan and India were compromised while in the open. The most recently propagated malicious applications, which were primarily masquerading as messaging applications and were distributed via Google Play and other platforms, did so in September 2023.
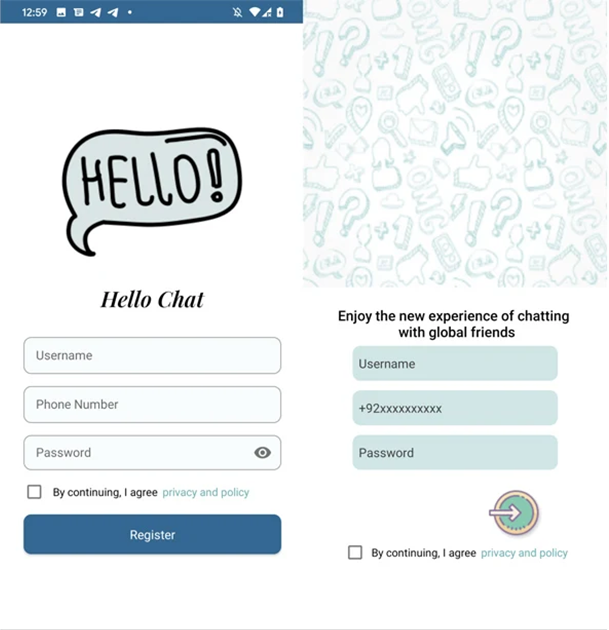
- Privee Talk (com.priv.talk)
- MeetMe (com.meeete.org)
- Let’s Chat (com.letsm.chat)
- Quick Chat (com.qqc.chat)
- Rafaqat رفاق (com.rafaqat.news)
- Chit Chat (com.chit.chat)
- YohooTalk (com.yoho.talk)
- TikTalk (com.tik.talk)
- Hello Chat (com.hello.chat)
- Nidus (com.nidus.no or com.nionio.org)
- GlowChat (com.glow.glow)
- Wave Chat (com.wave.chat)
Notable for being the only non-messaging application, Rafaqat رفاق was promoted as a means to obtain the most recent news. Since its removal by Google on October 26, 2022, the application in question has accumulated 1,000 downloads since its developer, Mohammad Rizwan, uploaded it to Google Play.

At this time, the precise method by which the malware spreads remains unknown. However, based on the characteristics of the compromised applications, it appears that the targets were duped into downloading them as a component of a honey-trap romance scam. In this type of scam, the attackers convince the victims to install illegitimate applications under the guise of conducting a more secure conversation.
Patchwork, a threat actor suspected of having connections to India, has utilized this method previously. Meta disclosed in March 2023 that the hacking group fabricated Facebook and Instagram accounts in order to distribute connections to malicious applications with the intention of compromising individuals in China, Pakistan, India, Bangladesh, Sri Lanka, and Tibet.

Furthermore, this is not the initial occurrence in which the assailants have been spotted employing VajraRAT. In early 2022, the Chinese cybersecurity firm QiAnXin published documentation of a campaign utilizing VajraRAT to target Pakistani military and government organizations. Vajra is derived from the Sanskrit term denoting a discharge of lightning.
In its November 2023 analysis of the malware, Qihoo 360 linked it to a threat actor it monitors using the alias Fire Demon Snake (APT-C-52).
It is probable that Nepalese government entities, in addition to those in Pakistan and India, have fallen prey to phishing campaigns that distribute Nim-based backdoors. It has been ascribed to the SideWinder group, an additional organization that has been identified as operating with the intention of benefiting India.

The development coincides with the discovery of financially motivated threat actors from Pakistan and India targeting Indian Android users with a bogus loan application (Moneyfine or “com.moneyfine.fine”) as an element of an extortion scheme. The app manipulates a user-uploaded selfie, which is a prerequisite for the Know Your Customer (KYC) procedure, to generate a nude image. Victims are enticed to make a payment or face the possibility that the altered photos will be shared among their social media connections.
“These unknown, financially motivated threat actors make enticing promises of quick loans with minimal formalities, deliver malware to compromise their devices, and employ threats to extort money,” Cyfirma stated in a report released late last month.

Additionally, this development coincides with a larger pattern of individuals succumbing to predatory loan applications, which are notorious for stealing confidential data from compromised devices and pressuring victims into making payments through blackmail and harassment.
A recent report published by the Network Contagion Research Institute (NCRI) indicates that Yahoo Boys, a Nigeria-based cybercriminal group, is increasingly targeting adolescents in the United States, Canada, and Australia with financial extortion attacks.

“Nearly all of this activity is linked to West African cybercriminals known as the Yahoo Boys, who are primarily targeting English-speaking minors and young adults on Instagram, Snapchat, and Wizz,” according to NCRI.
Wizz, whose Android and iOS applications were subsequently removed from the Apple App Store and the Google Play Store, issued a rebuttal to the NCRI’s report, claiming “not informed of any successful extortion attempts that transpired during Wizz app communications.”
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager entered the field of content in an unusual way. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.
Read more news here






