10+ Best Operating Systems (OS) for Hacking in 2024
10+ Best Operating Systems (OS) for Hacking in 2024
The goal of ethical hacking is to find holes in computer networks or systems and take advantage of them so they may be corrected later. Hackers employ a variety of methods to find dangers and consequently improve the device’s security. These persons are capable of hacking networks or computers using Linux-based operating systems. It has many applications that can stop cybersecurity assaults.
The list of best operating systems for hacking, along with links to download them, is provided below:
Best Operating System for Hacking: Top Picks
1) Kali Linux
For digital forensics and penetration testing, there is a Linux security distribution called Kali Linux. One of the greatest hacking operating systems, it comes with over 600 inbuilt penetration-testing programs (which test for computer vulnerabilities). Both Windows and Mac OS support this OS.
Features:
- Penetration Testing is possible with it.
- This platform comes in both 32 and 64-bit versions.
- Updates for Kali Linux can be made without downloading a new version.
- This OS supports complete disk encryption.
- The network installation of Kali Linux may be readily automated and modified.
- Support for live USB installations.
- Forensic work can be done using its forensics mode.
2) Parrot OS

Hackers can use Parrot OS as a platform. A user-friendly editor is available for program development. You can browse the web safely and discreetly with this platform. In addition, Parrot OS can be used by hackers for a variety of tasks, including vulnerability analysis, penetration testing, computer forensics, and more.
Features:
- It is offered as resource-constrained, lightweight software.
- The source code is open for anybody to read and modify.
- Offers assistance from professionals to aid you with cybersecurity.
- This hacking operating system has a distributed infrastructure with specialized CDNs.
- This operating system can be shared with others.
3) BackBox
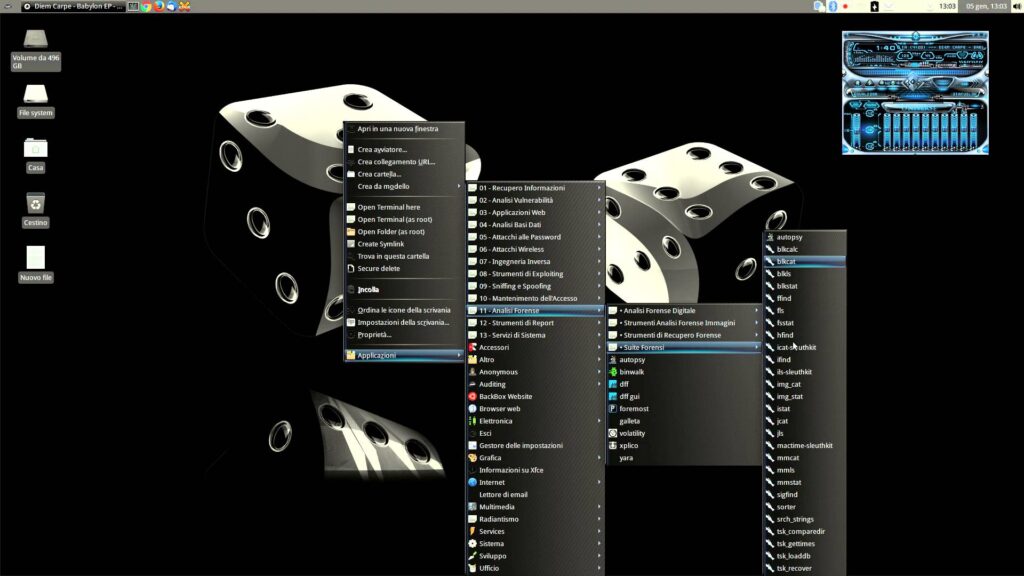
BackBox is an open-source operating system based on Ubuntu that provides a capability for penetration testing and security evaluation. In addition, this system offers a network analysis toolkit for IT environment security. It consists of a toolbox required for ethical hacking.
Features:
- It aids in tasks like vulnerability analysis and computer forensics.
- Design carefully to eliminate duplication.
- It uses the fewest resources possible from your machine.
- This hacker operating system offers a user-friendly desktop setting.
- Allows you to practice attacking a network or application.
- It provides both speed and stability.
4) BlackArch
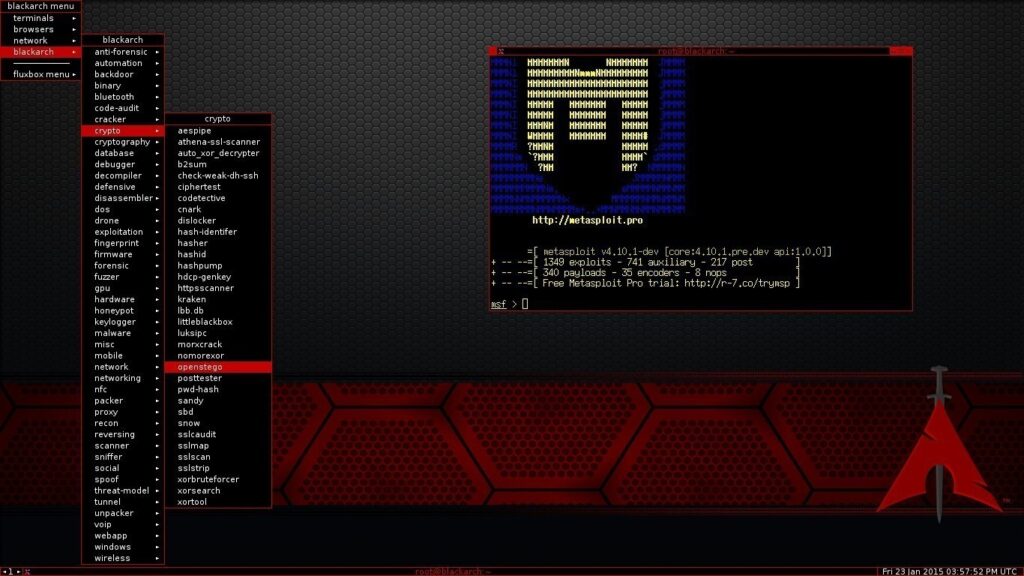
BlackArch is a freeware Linux-based system that includes a large selection of tools for networking, automation, and other areas. It is an operating system that is open-source and was made specifically for security analysts and penetration testers. Either individually or collectively, you can install it.
Features:
- It provides numerous window managers and lives ISO (International Organization for Standardization).
- The resources needed to execute this operating system are minimal.
- Supports a variety of architectural styles.
- You can create the installer from scratch.
5) Fedora Security Lab

You may perform security auditing, forensic analysis, and hacking in the Fedora Security platform. It includes a quick and tidy desktop interface. This OS includes crucial networking utilities like Wireshark, Medusa, Sqlninja, and others. Pen testing and security testing are made easier by the Fedora Security platform.
Features:
- It features a personalized menu that provides all the guidance required to choose the appropriate exam path.
- You can preserve your test results permanently with this application, which can create Live USB drives (a complete operating system that can be loaded).
- To enable software installation while it is already running, it builds a live image.
6) Dracos Linux

Open-source OS Dracos Linux provides penetration testing. It is completely loaded with several different capabilities, including forensics, data collection, malware analysis, and others.
Features:
- This platform can be used by anybody to research, edit, and distribute.
- A quick operating system for malware investigation is Dracos Linux.
- Your private information is not collected by this hacker operating system.
- It makes it simple for moral hackers to conduct vulnerability analysis.
7) CAINE

An application called CAINE, which runs on Ubuntu, delivers a full forensic context with a graphical interface for users. This operating system can be added as a module to already installed software applications. One of the better operating systems for hacking is this one since it automatically pulls a chronology out of RAM.
Features:
- The project is open-source.
- All read-only devices are blocked by CAINE.
- This OS is compatible with current software.
- The digital investigator is supported by an environment while doing the investigation.
- CAINE features can be changed.
- It provides an operating system that is easy to use.
8) Samurai Web Testing Framework
Samurai Web Testing Framework is a simulated machine that can be utilized by VirtualBox and VMWare (cloud computing software). The configuration of this live Linux installation is set up for web pentesting. It comes with a variety of website-attacking capabilities.
Features:
- Samurai Web Testing Framework is a freely available project that focuses on attacking sites.
- It has already been set up for web penetration testing.
- Characteristics that can be employed to prepare the website for an attack.
- It includes tools like WebScarab (a tool for evaluating web security applications) and ratproxy (a program for running a web proxy server).
9) Network Security Toolkit (NST)
The Linux-based Network Security Toolkit (NST) is a Live USB/DVD flash device. It provides security for computers and network tools that are open-source, free, and vulnerable to hacking. Cybercriminals employ this form of distribution to carry out routine safety and monitoring of network traffic tasks.
Features:
- Free-of-charge network security programs are simple to access.
- Its Web User Interface (WUI) is simple to use.
- A network security evaluation and validation tool is the Network Security Toolkit.
- It involves keeping track of virtual computers on a remote server.
10) Demon Linux
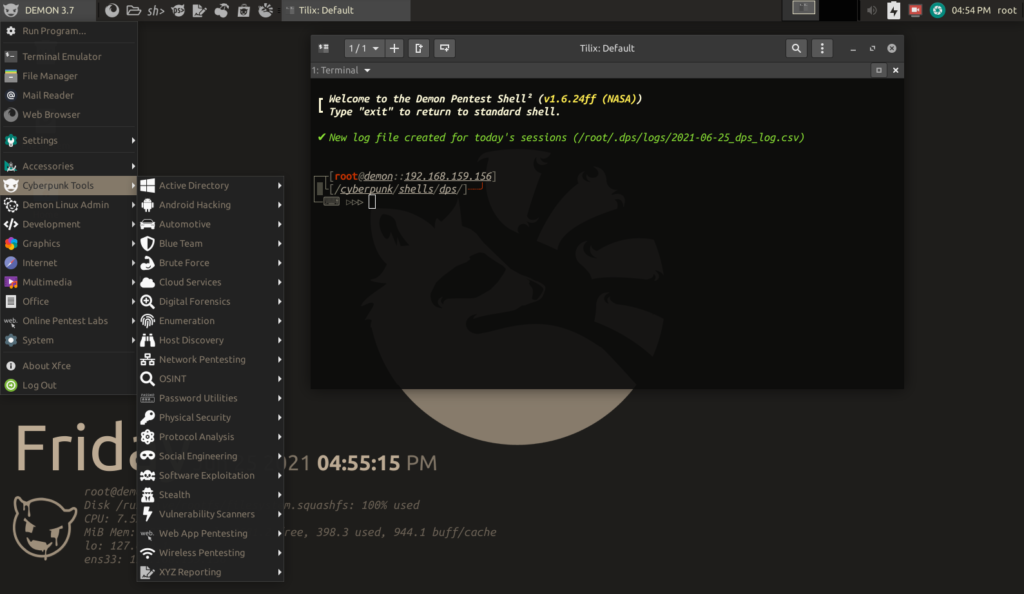
The distribution of Linux employed in hacking is called DemonLinux. It comes with a minimal desktop setting. The system has a straightforward user interface and a dark appearance. You can look up or open any stuff using DemonLinux by hitting just one key.
Features:
- By tapping the Windows key, you can quickly search for the items that you need.
- It has a straightforward dock layout with a bar at the OS’s base.
- It is duly compatible with Google Chrome and Firefox.
- Use a quick access option to quickly record the desktop or take a screenshot to save time.
11) DEFT Linux
Specifically designed for use in digital forensics investigations, the Digital Evidence and Forensic Toolkit (DEFT) Linux software is available. An environment that is suitable for forensic workstations is provided, which allows for the collection, preservation, examination, and reporting of digital evidence
Features:
- Digital forensics investigations are the primary focus of DEFT Linux.
- Minimizes the possibility of modifying evidence on a suspect machine by operating from a live DVD or USB drive.
- Autopsy and Sleuth Kit, which are industry-standard tools for the acquisition, analysis, and reporting of digital evidence, are pre-installed.
- Prevents accidental writes to storage devices, thereby guaranteeing forensic integrity.
- Efficient forensic workflows are facilitated by a user-friendly interface and a lightweight desktop environment (LXDE).
12) NodeZero Linux
In order to facilitate penetration testing on PCs with limited resources, this lightweight and modular distribution was developed. It provides a user-friendly interface in addition to a comprehensive collection of important security capabilities.
Features:
- Designed to operate efficiently on machines with restricted resources.
- Pre-configured with the necessary tools for security assessments, exploitation, and vulnerability scanning.
- Utilizes a user-friendly interface that is intuitive for both beginner and seasoned penetration testers.
- Provides modularity, enabling users to incorporate or eliminate particular tools to their testing requirements.
- Operates efficiently on virtual machines or older hardware that has limited RAM and processing capacity.
13) Linux Kodachi
This distribution, which is based on Ubuntu, is yet another alternative that is suitable for beginners and places an emphasis on penetration testing and security assessments. There is a decent balance between the pre-installed tools and the ease of use that it offers.
Features:
- System security and user privacy are the primary concerns of Linux Kodachi.
- The anonymization of your traffic is facilitated by built-in features such as Tor and VPN, which render it challenging to monitor your online activity.
- The distinctive “Nuke” feature enables the complete encryption of the system with a secondary password, thereby safeguarding data in the event that the user is compelled to disclose their logon credentials.
- Includes tools for administering encryption, minimizing online traces, and anonymizing browsing data.
- Employs the Xfce desktop environment to provide a user-friendly and recognizable interface.
Conclusion
All in all, these were the Top 10 Best Operating Systems (OS) for Hacking in 2024. In addition, if a person is willing to know more about the same topic or any other concerning topic of ethical hacking and cyber security, the same can go forCraw Security, the Best Cyber Security Training Institute in India, which delivers the best quality information security knowledge to all individuals via both online and offline training methods. Call +91-9513805401 to know more.
Moreover, an interested person in the trajectory of Linux Essentials can even track down our world-class Red Hat Certifications Training through the most suitable instructors with 10+ years of quality experience in the trajectory of Linux. Craw Security is a prestigious as well as Accredited Training Partner of Red Hat Inc. to deliver their certifications and training in a cost-effective manner to all interested persons.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blogs, he also writes for brands including Craw Security, Bytecode Security, and NASSCOM.