CERT-In Issued “Warning” for Galaxy S23, and Other Samsung Smartphone Users

CERT-In Issued “Warning” for Galaxy S23, and Other Samsung Smartphone Users
GOI Cybersecurity Watchdog CERT-In has Issued a Regulatory “Warning” for Samsung Galaxy S23, and Other Samsung Smartphone Users.
The government has issued a high-risk advisory for owners of Samsung mobile phones. CERT-In has issued a high-risk warning (Note CIVN-2023-0360) specifically for Samsung cellphones that are operating on Android versions 11, 12, 13, and 14. Several vulnerabilities have been revealed, enabling attackers to circumvent security measures, execute code of their choice, initiate heap overflow, gain access to SIM PIN, retrieve sandbox data, break Knox Guard lock, and exploit other weaknesses. Users are recommended to install security updates, apply software patches, and exercise vigilance while dealing with programs, links, and unfamiliar websites.
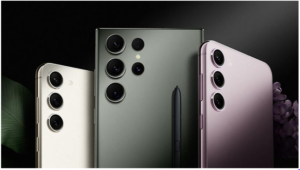
The Computer Emergency Response Team (CERT-in), which is the primary cybersecurity section of the Indian government, has issued a warning specifically for users of Samsung smartphones. CERT-In has issued a high-risk warning to users regarding various vulnerabilities. Specifically, Note CIVN-2023-0360 highlights severe security problems found in phones running Android versions 11, 12, 13, and 14.

The Android 14 update has been released for Samsung’s top smartphone series, the Galaxy S23. CERT-IN, the cybersecurity agency, has issued a note stating that Samsung devices have been found to contain various vulnerabilities. These flaws have the potential to enable an attacker to circumvent existing security measures, thereby granting unauthorized access to sensitive information. Additionally, they have the ability to execute any code of their choosing in order to compromise the specific system.
The vulnerabilities might potentially enable hackers to exploit memory overflow and stack-based buffer overflow, gain access to the device’s SIM PIN, transmit broadcasts with elevated privileges, retrieve sandbox data of AR Emoji, and overcome Knox Guard lock by manipulating the system time.

What is the cause of this vulnerability?

The vulnerabilities are attributed to an improper access control flaw in KnoxCustomManagerService and SmartManagerCN component, an integer overflow vulnerability in the face preprocessing library, an improper authorization verification vulnerability in AR Emoji, an improper exception management vulnerability in Knox Guard, different write vulnerabilities in the bootloader, HDCP in HAL, liblfaaca and libsavsac.so components, an improper size check vulnerability in softsimd, an improper input validation vulnerability in Smart-Clip, and an implicit intent hijacking vulnerability in contacts, according to Cert-In.
Samsung phones are on high-risk security alert How to protect?

It is recommended that users of Samsung cell phones promptly install security updates. In order to ensure the security of their devices, users should regularly install security updates provided by suppliers. In such instances, the corporations promptly release updates to address vulnerabilities.
Moreover, in the event that you have not updated your phone’s software, it is advisable to be careful when installing applications, clicking on links, and visiting unfamiliar websites.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager entered the field of content in an unusual way. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.
READ MORE ARTICLE HERE
116 Ransomware Files Infecting Linux and Windows Systems Were Discovered on the PyPI Repository
Latest NKAbuse Ransomware Launches DDoS Attacks Using NKN Blockchain Technology.







