Cyber Attacks in 2023: What Is a Brute Force Attack?

Cyber Attacks in 2023: What Is a Brute Force Attack?
One kind of account takeover attack is a brute force attack. It makes an effort to deduce passwords and other secrets that would allow access to content that is prohibited by using trial and error.
An attacker using a brute force attack attempts every password or other secret value in an effort to find the right one. Although the success of these assaults is inevitable, they can be prevented by employing multi-factor authentication (MFA) or creating strong passwords.
How Does a Brute Force Attack Work?
The foundation of a brute force attack is the expectation that the attacker would eventually figure out the password, assuming one exists. If a user has an eight-character password, for instance, an attacker will eventually get the right password if they attempt every possible eight-character combination.

The first drawback of brute force attacks is their potential for high execution times. A lengthy random password may take millions of years or longer to crack, even if automated brute forcing techniques can attempt several passwords per second.
Nevertheless, this degree of security is sometimes absent from passwords, which makes brute force an effective attack vector. The attacker can steal money or data, infect computers with malware, or carry out other nefarious deeds if they are able to figure out the proper password and access the user’s account.
Types of Brute Force Attacks
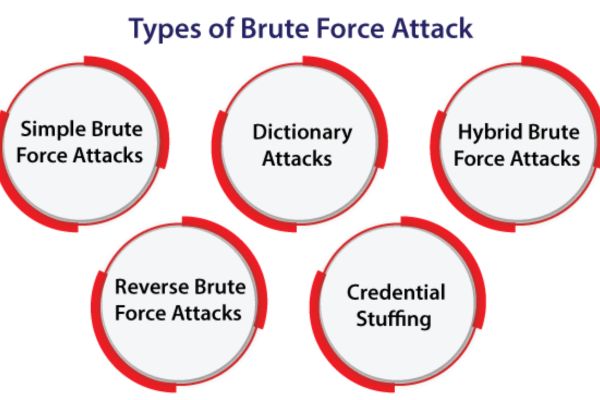
The process of trying different password guesses until the attacker finds the right one is known as a brute force attack. There are a few different types of brute force attacks, including:
| S.No. | Types | How? |
| 1. | Simple Brute Force Attack | An attacker using a basic brute force assault verifies each potential password choice in detail. They might attempt aaaaaaaa, aaaaaaaab, etc. as examples. |
| 2. | Dictionary Attack | Dictionary attacks are based on a list of frequently used words from dictionaries and password breaches.
These passwords are frequently also subjected to basic manipulations, including changing special characters (@ for a, etc.) or appending numbers at the end of words. |
| 3. | Hybrid Brute Force Attack | A dictionary attack and a basic brute force attack are combined to create a hybrid brute force attack.
When it fails, the attacker uses a dictionary to attempt to guess the user’s password before switching to a straightforward brute force attack. |
| 4. | Reverse Brute Force Attack | An attacker using a reverse brute force attack begins with a password that is well-known or widely used. After that, they look for usernames that have that password. |
| 5. | Credential Stuffing Attack | An attacker using credential stuffing attempts to access other websites using credentials for one site. This makes an effort to find passwords that are reused on several accounts. |
How to Prevent Brute Force Password Attacks?
The possibility of a successful account takeover exists with brute force password guessing attacks. Some ways to protect against these threats include:
- Strong Passwords
The foundation of brute force password assaults is the ability to quickly guess a password. A brute-force assault takes longer and requires more complexity when a long, random password is used.
- Salted Hashes
Before hashing and storing a password, salting entails mixing each one with a distinct random number. This makes it harder to discover and crack passwords by preventing identical passwords from having identical password hashes.
- Rate Limiting
Passwords are tested against a live login page in online brute force attacks. By restricting the amount of login requests that may be made in a minute, or by implementing rate limitation, these attacks become less efficient and slower.
- Account Lockouts
After a certain amount of unsuccessful login attempts, account lockouts prohibit access to a user’s account, even with the proper password. With only a few guesses remaining, an attacker’s chances of success are drastically decreased, effectively disincentivizing brute force attacks.
- Two-Factor/ Multi-Factor Authentication (2FA/MFA)
To access a user’s account using 2FA or MFA, two or more distinct authentication factors must be used. For instance, MFA might make it necessary for an attacker to figure out or obtain both the password and the one-time password (OTP) that an authenticator software generates.
- Behavioral Analytics
Behavioral analytics can be used by a company to spot unusual activity pertaining to user accounts. An attempt at a brute-force password guessing assault, for instance, is indicated by a high volume of unsuccessful login attempts.
- IP Blocklisting
Also, a hacker has the ability to specifically stop traffic coming from known malicious IP addresses. This may make it more challenging for a botnet to launch a brute force assault designed to guess a password.
Defending Against the Modern Cyberattack
In recent years, the environment of cyber threats has drastically changed. Although brute force attacks are not as new as they once were, they are still a concern thanks to contemporary technologies. Consequently, there is an increased likelihood for a brute force attacker to obtain access to a user’s account and pilfer funds or data.

Account takeover is just one type of cyberattack that businesses must deal with, though. Check out Check Point’s 2023 Mid-Year Cyber Security Report for additional details on the state of cyber threats today.
Organizations now have to contend with the Fifth Generation of cyberattacks, which are more sizeable, intelligent, and cunning than in the past. Find out more about using Check Point to defend against the Gen V cyberthreat.
About The Author
Suraj Koli is a content specialist with expertise in Cybersecurity and B2B Domains. He has provided his skills for News4Hackers Blog and Craw Security. Moreover, he has written content for various sectors Business, Law, Food & Beverage, Entertainment, and many others. Koli established his center of the field in a very amazing scenario. Simply said, he started his career selling products, where he enhanced his skills in understanding the product and the point of view of clients from the customer’s perspective, which simplified his journey in the long run. It makes him an interesting personality among other writers. Currently, he is a regular writer at Craw Security.
READ MORE ARTICLE HERE









