Navigating Threat Situations 2021 – From Ransomware to Botnets

Navigating Threat Situations 2021 – From Ransomware to Botnets
Despite recovering from the worst pandemic, cyber threats show no signs of downshifting, and cybercriminals are still lacking in malicious and sophisticated ways to reach their goals.
NS Global Threat Landscape Report It shows a dramatic increase in advanced cyberattacks targeting digital infrastructure, organizations and individuals in 2021. Threats can take many forms with the goal of committing fraud and harming businesses and people. Ransomware, DDoS attack, Phishing, malware, and man-in-the-middle attacks are the greatest threats to today’s businesses.
As new threats emerge, attackers take advantage of them, but most companies are only aware of the current threat.
Organizations are struggling to deal with these threats because they are resource-intensive and do not understand the context of evolving threats. For these reasons, organizations need visibility into advanced threats, especially for infrastructure. This article outlines the evolution of the 2021 cyber threat landscape.
Evolving Threat Situation – Find What You Don’t Know
1 — — Ransomware
Ransomware remains a common and evolving cybersecurity threat, with some highly publicized incidents. Ransomware incidents affect organizations, businesses, and individuals, resulting in financial losses, operational disruptions, and data breaches. Vulnerabilities and misconfigurations facing the Internet, third-party and managed service providers, Remote Desktop Protocol (RDP), and phishing email compromises remain the most common transmission routes.
The outbreak of extortion schemes increased from single to multiple schemes in 2021. After first encrypting sensitive information from the victim and threatening to disclose it unless the ransom is paid, the attackers are now targeting the victim’s partners and customers as a ransom to maximize profits.
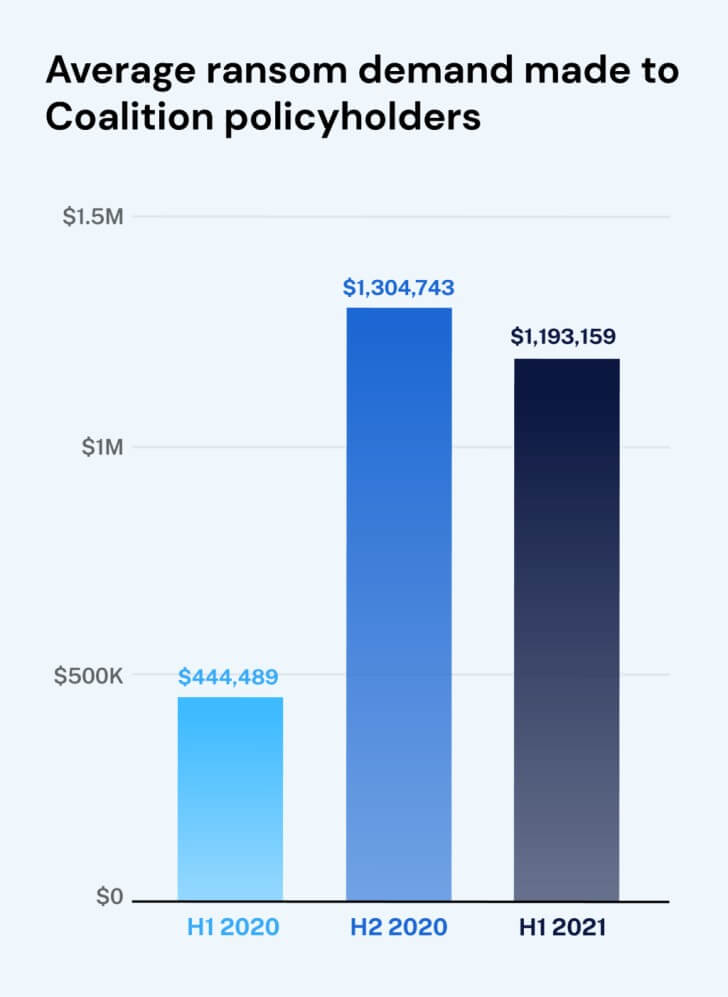
New research from Coalition It was revealed that the average ransom demand in the first half of 2021 increased by 170% compared to last year.
It is likely to reach $ 100 million in 2022. ENISA threat status 2021.
In addition, cryptocurrencies are a payment method choice as they promise a secure, fast and anonymous channel for trading money. Attackers have also moved their options from Bitcoin to Monero due to their increased anonymity.
Recommendations to prevent becoming a victim:
- Security awareness training
- Use a secure website
- Defense-in-depth cybersecurity strategy
- Vulnerability assessment and penetration testing
2 — — Cryptographic jack
Another attack trend in 2021 is crypto jacks related to the growing instability of the crypto market. Given the anonymity of cryptocurrencies, it is a convenient and attractive medium of exchange for attackers. In this attack, a cybercriminal deploys hidden crypto jack software on a targeted device and steals it from a crypto wallet. Siloscape, a new malware that appeared in June 2021, targets Windows containers to create malicious containers, load cryptocurrency miners, and identify and steal cryptocurrencies.
Recommendations for combating cryptojacking:
- Implement web filters and blacklisted IP addresses from encrypted IP pools
- Develop patches for well-known exploits
- Implement a robust vulnerability management program
3 — — Data leak
Stealing sensitive data from organizations and users is nothing new, but how threat actors approach data is evolving. Just as organizations employ new technologies to survive in a digital environment, threat actors use sophisticated methods to exploit attacks. For example, deepfake technology.
This is not a new concept, but it has evolved significantly. With MI and AI, Deepfake technology allows you to digitally create portraits of individuals and impersonate victims. With AI and ML tools, you can create artificial versions of any audio or any video.
Cyber cube security researcher Deepfake audio and video content has warned that it could pose a major cyber threat to businesses around the world. Also, the widespread damage associated with this pretending content is expected to increase over the next few years. Also, increasing reliance on video-based communications is expected to be a major factor in motivating attackers to focus more on deepfake technology.
Recommendations for monitoring and removing deepfake:
- Improved digital archive to identify fake video and fake audio clips
- Implement the Content Authenticity Initiative to validate the creator and source of your data
Four — — Botnet
New botnets continue to emerge as older botnets continue to change to circumvent current security solutions. This is because cybercriminals are aware of the new paradigm of botnets as a service. In this paradigm, bonnets can be leased/sold to businesses and individuals for misuse and financial gain.
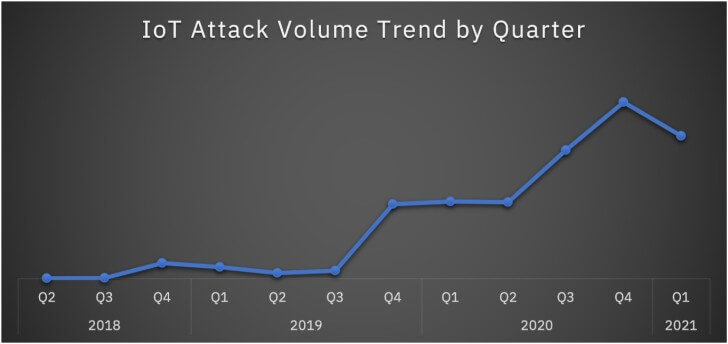
In addition, the presence of botnets in the cloud and mobile environments offers new possibilities for quickly learning and exploiting weaknesses in user behavior patterns. Increasing IoT adoption and lack of security during IoT development and deployment represent another feasible frontier for botnet proliferation.
NS Recent reports It turns out that overall IoT attacks by well-known IoT botnets such as Mirai and Mozi have increased by 500%.
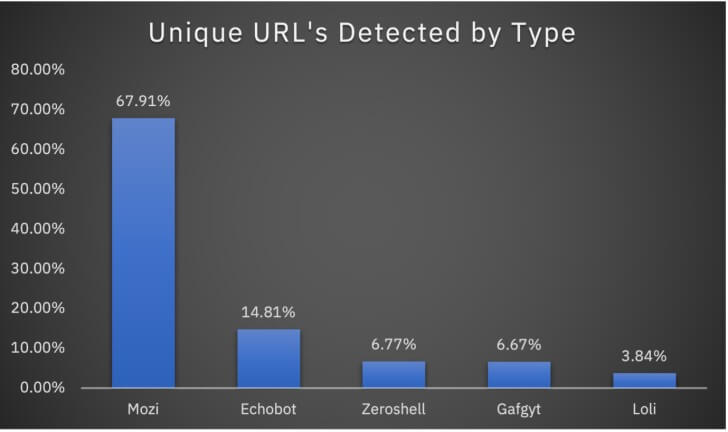
2020, Mozi Botnet attack according to an X-Force survey, it accounts for 89% of IoT attacks. In addition to Mozi, several other botnets continue to target the IoT landscape. Eco boat, Zeroshell, Gafgyt, and Loli are four notable botnets that impact businesses around the world.
Recommendations for counterattacking:
- Hire Penetration test
- Change the default IoT settings when installing a new device
- Implement a powerful patch management program
- Practice effective bot protection and mitigation strategies
Big picture
New cyber threats are constantly being detected and can affect operating systems such as Linux, Windows, iOS, Mac OS and Android. In addition, new threat vectors are evolving due to potential vulnerabilities in the continued adoption of remote working and the increasing number of connected IoT devices.
This evolution of the cyber-threat situation has forced enterprises to stay ahead by upgrading their vulnerability management programs, security tools, processes, and skills. Fully managed Indusface AppTrana Web Application and API Protection (WAAP)Address these challenges and speed up threat detection and response.
If you want to be proactive and active to protect your information, be aware of the recent cybersecurity threat situation.
Read Another Article: Malware Malicious Apps Remove: 1 Crore People Downloaded These Common Apps. 3 Thousand Rupees To Be Deducted Every Month






Thank you for sharing such a great piece of information. This is the thing we all had to seriously look into this or you want to save your data from hackers or you want to learn ethical hacking you can visit CRAW SECURITY. Craw Security offers a high level of technical education to its students, clients, and partners in the IT Industry. We have got a team of well-qualified, certified, and experienced trainers to give the best training.