Technology-Facilitated Sextortion: Scammers Employed Nude Video Calls to Extort Money from a Businessman

Technology-Facilitated Sextortion: Scammers Employed Nude Video Calls to Extort Money from a Businessman
Moradabad: Law enforcement officials in Moradabad, Uttar Pradesh, have successfully caught five individuals who were engaged in a sextortion scheme specifically targeting local businessmen. The authorities uncovered a fraud that involved coercing victims through explicit video chats, where they were threatened with the release of incriminating recordings unless they paid significant amounts of money.

The fraudsters, employing advanced technology, enticed their targets into participating in video conferences of a sexual nature. The phone conversations were covertly taped without the victims’ awareness. Afterward, the defendant would intimidate the targeted individuals by threatening to publicly disclose the compromising footage unless they responded with their money requests.

After receiving many complaints from concerned businessmen who were being targeted by this blackmail strategy, law enforcement agencies promptly launched an inquiry. By exerting persistent efforts, they successfully identified and captured five suspects who are thought to be the masterminds of the scheme.
According to Ramit Sharma, the Inspector General of Police (IG) for Moradabad Zone, the individuals who were apprehended employed counterfeit profiles on social media platforms to entice businessmen. Subsequently, they documented their video conversations and extorted money from the individuals involved, employing the threat of disseminating their films widely.

The Inspector General (IG) stressed the significance of digital awareness and advised residents to show prudence when engaging online, particularly when encountering unfamiliar individuals.
The quintet of apprehended persons are being detained by law enforcement, confronting charges pertaining to extortion and cybercrime. Ongoing investigations are being conducted to determine the complete scope of their actions and ascertain the presence of any more collaborators.
Authorities have urged individuals who may have been targeted by similar scams to step forward and swiftly report such cases. The police have affirmed their dedication to guaranteeing a safe and secure atmosphere, asking individuals to stay alert to online dangers and swiftly report any suspicious actions.
Working Methodology of Sextortion Gangs
| Targeting | Scammers employ fraudulent profiles to establish contact with individuals on social media or dating services. |
| Building Trust | They establish rapport with the target and gradually progress the discussions towards explicit material, such as engaging in video calls. |
| Recording | Scammers surreptitiously capture these encounters without the victim’s awareness. |
| Threats and Extortion | The perpetrators employ the tactic of extortion by coercing the victim to either make a monetary payment or fulfill their requests, under the threat of publicly disclosing sexual material. |
| Harassment and Demands | Scammers exert pressure on their victims to make prompt payments and may persist in demanding further funds or favors. |
How To Stay Safe From Sextortion?
By following the below-mentioned best practices, one can nicely stay avert from the Sextortion gangs:
- Be Vigilant: Extreme caution should be exercised when interacting with acquaintances online, particularly on dating or social media platforms.
- Limit Sharing: It is advisable to refrain from disclosing personal or intimate information to individuals whom you have recently encountered online or do not know well.

- Verify Identities: It is advisable to authenticate the identities of individuals with whom you establish online connections prior to participating in sensitive discussions or activities.
- Disable Location Services: Disable location services to safeguard against the unintended disclosure of your current location.
- Secure Privacy Settings: Consistently assess and enhance your privacy configurations on social media platforms in order to regulate access to your content.
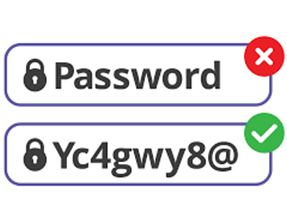
- Use Strong Passwords: Implement robust and distinct passwords for your accounts in order to avert unauthorized entry.
- Avoid Impulsive Actions: Cease acquiescing to demands or threats posed by unidentified individuals on the internet.
- Trust Your Instincts: When you sense suspicion or unease, follow your intuition and immediately terminate any communication.
- Report Suspicious Activity: Sextortion attempts and suspicious behavior should be reported promptly to the authorities.
- Educate Yourself: Maintain awareness of the most recent online falsehoods and educate yourself on how to avoid them.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager entered the field of content in an unusual way. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.
READ MORE ARTICLE HERE








