“The Largest Breach of All Times”: The Discovery of 26 Billion Records Found Online
“The Largest Breach of All Times”: The Discovery of 26 Billion Records Found Online
It has been dubbed the “mother of all breaches” by security researchers who ran across billions of exposed records online.

However, it appears that the dataset is a compilation of multiple breaches rather than a singular breach. Frequently, these collections are produced by data enrichment firms. The process of integrating disparate data from external sources or third-party data from internal systems with first-party data from internal sources is known as “data enrichment.” Any organization would benefit greatly from enriched data, as it becomes more insightful and practical.
The investigators reported:
| “While more than 26 billion records were identified by the team, duplicates are also extremely probable. However, the compromised data comprises significantly more than mere login credentials; the majority of the exposed data is sensitive and, as such, advantageous for malicious entities.” |
An additional development pertaining to compromised personal information involves a cybercriminal known as “emo” claiming to be in possession of 15 million distinct records of Trello project management accounts for sale.
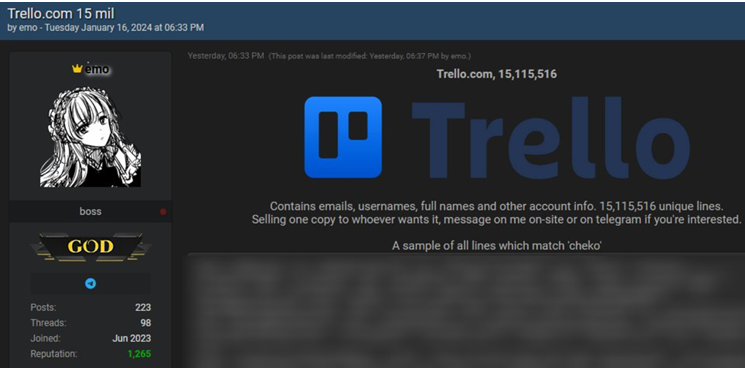
Given its widespread adoption among organizations, Trello’s utilization elicited certain concerns.
Atlassian, the operator of Trello, refutes any allegations of a security compromise. It appears that a substantial compilation of email addresses was utilized to conduct a test against Trello.

This raises the inquiry: under what circumstances is a massive disclosure of personal information not considered a breach?
The following is a definition of a breach that I can comprehend:
| “A compromise occurs when information is unintentionally made public within a susceptible system, typically as a result of inadequate access controls or software security vulnerabilities.” |
The exposure of billions of records can be considered a breach, given it is highly improbable that the instance was intentionally left open. Ultimately, that quantity of data can be sold for a substantial sum of money.
Atlassian can confidently affirm that it was not subjected to a security compromise, as the perpetrators exploited an already present functionality. Perhaps due to an unintentional oversight, but why acknowledge that you should not have permitted it?

Certain individuals argue that a data breach can alone occur as a consequence of a hacking incident, whereas any other form of unauthorized disclosure is considered a leak. From that perspective, neither of the databases originated from a security breach. One set was discovered accidentally, whereas the other was generated via a valid API.
However, for those who have been impacted, the ultimate outcome is essentially identical, regardless of whether their data was exposed in a security breach, collected through scraping, or obtained by a data enrichment firm. Your information is readily accessible to any cybercriminal who wishes to exploit it.

To determine if your data is accessible on the internet, you may utilize our complimentary Digital Footprint scan. Please provide the email address you are interested in (preferably the one you use most frequently), and we will send you a report.
It is possible that you will experience astonishment. However, it is important to note that it is not a source of embarrassment if your email address is discovered in a security breach. Nevertheless, it is crucial to be aware of such incidents and identify whether your password was compromised.
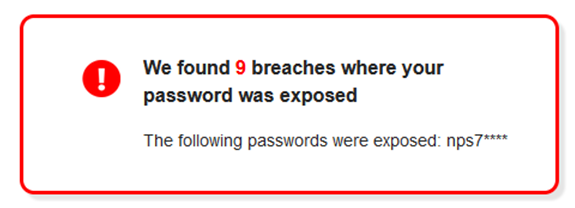
If the passwords generated are recognizable, it is advisable to modify the password in the corresponding location, activate two-factor authentication (2FA), and verify if it has been employed for other accounts.
Scammers possess exceptional proficiency in leveraging data obtained from security breaches to carry out social engineering attacks. Scammers will exploit the possibility of your data being released in a breach to initiate a phishing attack and gather additional information from you.

In the previous year, more than 2,000 companies and government entities disclosed incidents of data breaches that affected more than 400 million personal accounts. Establish Identity Monitoring to receive notifications anytime your personal information is compromised in a recent security breach.
About The Author:
Yogesh Naager is a content marketer who specializes in the cybersecurity and B2B space. Besides writing for the News4Hackers blog, he’s also written for brands including CollegeDunia, Utsav Fashion, and NASSCOM. Naager entered the field of content in an unusual way. He began his career as an insurance sales executive, where he developed an interest in simplifying difficult concepts. He also combines this interest with a love of narrative, which makes him a good writer in the cybersecurity field. In the bottom line, he frequently writes for Craw Security.
READ MORE NEWS HERE






