Uber Claims No Sensitive Data Exposed in Latest Breach… But There’s More to This

Thursday, 15 Sep 2022 – Uber’s Data leaked. That puts users’ confidential data at risk. The reason behind this was the internal computer system of Uber was hacked. There Uber refused to accept that the users’ data had been compromised.
| Uber (Cab Service Firm)
“We have no evidence that the incident involved access to sensitive user data (like trip history),” the company said. “All our services, including Uber, Uber Eats, Uber Freight, and the Uber Driver app, are operational.” |
Uber also stated – They are returning with all internal software tools that were previously revoked as a precautionary measure, continuing its notified law enforcement of the matter.
The count of things compromised and the existence time of the adversary in Uber’s network isn’t cleared yet. Uber hasn’t placed any references to how the event took place. While they said – Investigation and Response are in the process right now.
| Bill Demirkapi, (Independent Security Researcher)
However, according to Bill Demirkapi (Independent Security Researcher), the firm’s “no evidence” sounds “Sketchy.” “‘No evidence’ could mean the attacker did have access; Uber just hasn’t found evidence that the attacker *used* that access for ‘sensitive’ user data,” Demirkapi said. “Explicitly saying ‘sensitive’ user data rather than user data overall is also weird.” |
Behind this breach was a teenager of 18-Year-Old, trying to make money out of an Uber employee. He contacted Uber Employee and asked for access to an account via social engineering, after which the victim had to accept an MFA prompt. The prompt allowed the adversaries to register their own devices with the account access provided by an Uber employee.
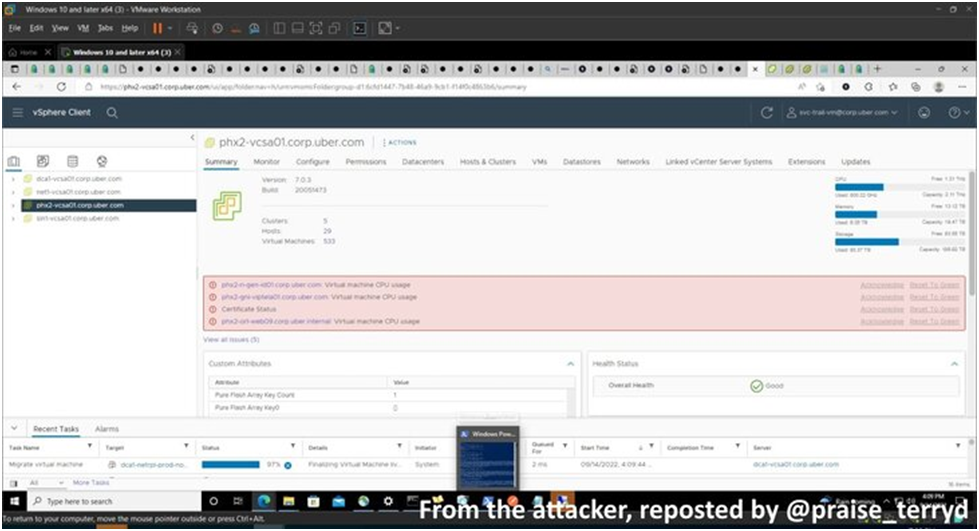
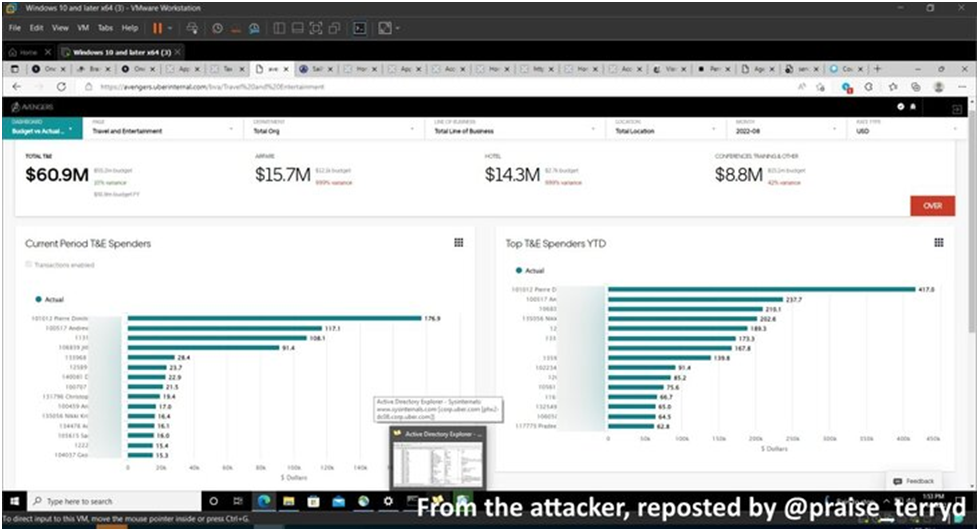
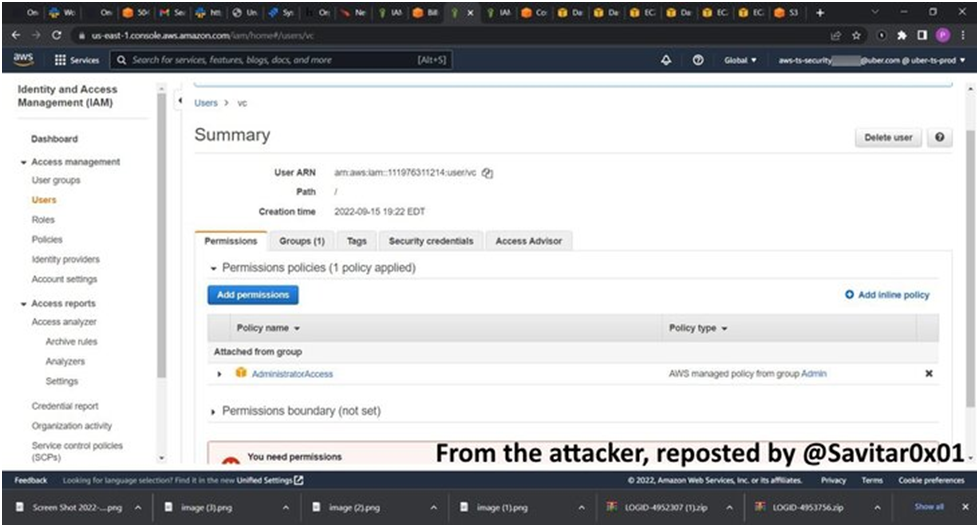
After getting initial access, the adversary got his hands on an internal network share that contained PowerShell Scripts with privileged admin credentials. It provided carte blanche access to other vital systems that are as follows:
- AWS
- Google Cloud Platform
- OneLogin
- SentinelOne Incident Response Portal
- Slack
| “Singapore-based Group-IB’s follow-up analysis of downloaded artifacts, as captured in some of the screenshots shared by the threat actor, has revealed them to be logs gathered from info-stealing malware that was put up for sale just days before cybercriminal underground.” |
Cybersecurity Firm
“These logs were put up for sale on September 12 and 14, which means this was very fresh data because the hack that utilized them was revealed from 15 to 16 September.” Moreover, they said the logs had authorization data for OneLogin.
Group-IB
“These logs indicate that at least two Uber employees (from Indonesia and Brazil) have been infected by stealer malware: Raccoon and Vidar stealers.” it was just their suggestion that the adversary might have tried to get more data out of Uber’s network via the purchased stolen data.
Sam Curry, Security Researcher
It is said that the teenager also got his hands on privately disclosed loopholes reports presented by HackerOne as part of Uber’s Bug Bounty Program.
HackerOne has disabled Uber’s account. However, the illegal access to unpatched loopholes in the platform could create a commotion on HackerOne (San Francisco). That’s because the adversary could sell the data to other cybercriminals in greed for monetary benefits.
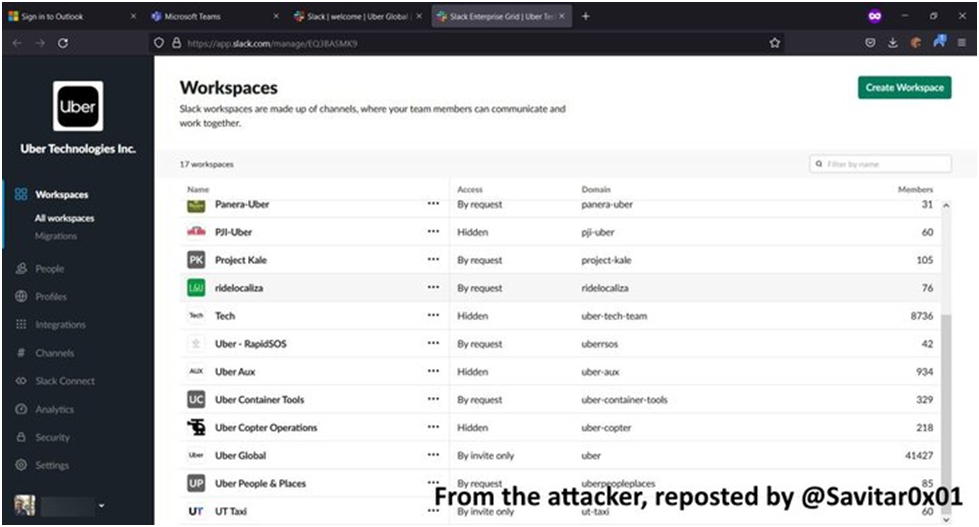
Till now, the adversary’s intentions behind the breach are anonymous, while content posted by the cybercriminal stated that the breach on Slack included a call for a high-end salary package for Uber’s Drivers.
| A report from The Washington Post noted that the attacker broke into the company’s networks for fun and might leak the company’s source code in months while describing Uber’s security as “awful.” |
Ismael Valenzuela Espejo, (vice president) threat research and intelligence, BlackBerry
“Many times, we only talk about APTs, like nation states, and we forget about other threat actors including disgruntled employees, insiders, and like in this case, hacktivists.”
“Organizations should include these as part of their threat modeling exercises to determine who may have a motivation to attack the company, their skill level and capabilities, and what the impact could be according to that analysis.”
The event happened to Uber, with other recent tabs involving Twilio, Cloudflare, Cisco, and LastPass, stating that social engineering has already begun taking over organizational security by becoming a persistent threat.
This practically shows that to compromise the data, only employees’ login credentials are needed. That proves if you depend on only password authentication, then your account security is weak.
| Masha Sedova, (co-founder and president) Elevate Security
“Once again, we see that a company’s security is only as good as their most vulnerable employees.” “We need to think beyond generic training; instead, let’s pair our riskiest employees with more specific protective controls. As long as we address cybersecurity as solely a technical challenge, we will continue to lose this battle.” |

Time-based One-Time Passwords (OTPs) are usually created via authenticator apps/ or sent as SMS messages are not enough to protect against 2FA roadblocks. It is proven by the event that happened.
Advice
To block such attacks, you can use FIDO2- Compliant physical security keys that are phishing-resistant. These drop passwords in exchange for an external hardware device that takes care of the authentication process.
“MFA providers should *by default* automatically lock accounts out temporarily when too many prompts are sent in a short period,” Demirkapi suggested, urging organizations to limit privileged access.
Conclusion
Online Apps are not perfectly secured enough to secure your confidential data over the platform. To protect your personal information from unauthorized access, you should get to learn the techniques and the use of tools to protect your data.
Kindly read more articles:
Over 280,000 WordPress Sites Attacked Using WPGateway Plugin Zero-Day Vulnerability
Grand Theft Auto VI footage leaked after hack, developer Rockstar confirms








